Best Practices in IBM i Security
- 1. IBM i Security Best Practices Jeff Uehling Security Expert Becky Hjellming Sr. Director, Product Marketing
- 2. Today’s Topics • Security assessment and physical security • Staying current • Virus and ransomware protection • System security levels • System value settings • Security audit journal • Resource security, authority collection and RCAC • Cryptography • Network security best practices • How Syncsort can help 2
- 3. Perform a periodic security assessment of all infrastructure by: • Your corporate security team • IBM X-Force security team (network experts) • IBM i Security consultants, Syncsort This is NOT just an IBM i statement, it’s everything. Perform a security assessment and penetration testing on: • Networks • Laptops, desktops & mobile devices and strategy • Servers • Applications Security Assessment Recommendation 3 Do you have the necessary skills? If not, resources do exist to help you!
- 5. Physical Security, Networking • Firewalls, routers, switches, cabling, power • Prevent configuration changes and sniffing equipment • Wireless challenges – secure networks are necessary (WPA, WPA2. etc.) Physical Security, Server • Front panel • Power, cabling • Racks/Storage devices Physical Security, Peripherals • Tape drives/cartridges, printers/output, fax, etc. • Printed output and backup media • SAN attached DASD Physical Security, Mobile Devices • Mobile Device Management considerations (ownership, “Secure Wipe”, etc.) Physical Security – a Necessity 5
- 7. Stay Current with Technology Staying current is vitally important for security IBM i release level • Older releases cannot be kept current • New technology changes cannot move backward Open Source technology • Changes rapidly and fixes for old versions are not developed by the open source community • Includes Java, OpenSSL/SSH, Apache, etc. Hardware technology • Like everything, hardware advances with new technology • Includes routers, switches, firewall, IDS/IPS, laptops/desktops/mobile devices, servers and more 7
- 8. Staying Current on Fixes ̶ Required Now More than Ever!
- 9. There are over 130 large-scale, targeted breaches in the U.S. per year, and growing by 27 percent per year. (Accenture, 2018) Statistics There are 24,000 malicious mobile apps blocked every day. (Symantec) A new organization will fall victim to ransomware every 14 seconds in 2019, and every 11 seconds by 2021. (Source: Cyber Security Ventures) 34% of businesses hit with malware took a week or more to regain access to their data. (Source: Kaspersky) The 2018 global average cost of a data breach is up 6.4 percent over the previous year to $3.86 million (Ponemon). Ransomware attacks are growing rapidly from year to year. (Cisco) 1.5 million new phishing sites are created every month. (Source: webroot) The number of cyber attacks is growing. In 2018, 758 million malicious attacks occurred according to KasperskyLab, (an attack launched every 40 seconds). 77 percent of compromised email attacks in 2017 were fileless (click URL to malicious website rather than email attachment). 9
- 10. Security Vulnerabilities • Numerous independent researchers • Lots of open source so easy to review code and look for issues • Common OS in many products (Linux, Unix, Windows) • When a vulnerability is found, it’s likely to be everywhere • Tools are available to exploit technology (look for holes) • Hacker tools, penetration testing tools, code scanners • High use technology, like Java, SSL, OpenSSL, is scrutinized • Vendors are doing more penetration testing and thus finding bugs Many security vulnerabilities are being reported… Spectre/Meltdown, ILOVEYOU, Heartbleed, Bash/Shellshock, Poodle, Ghost, Freak, Bar Mitzvah plus many, many more! What’s happening and why so many? 10
- 11. Security Vulnerabilities – IBM i 11 • Java (quarterly updates, you need to stay current) • OpenSSL / SSH • Web and Application Servers • Samba • Networking technology and (infrequently) cryptographic algorithms • IBM i OS IBM i technology with multiple (recent) reported vulnerabilities Typically, apply the PTF/Fix/Product Update, and the vulnerability is fixed, but not always. Additional actions may be required.
- 12. Security Vulnerabilities – Not just the OS • IBM i OS, LIC and Products • VIOS, IBM i, AIX, Linux partitions • HMC & Firmware • 3rd party (vendor) applications • SAN/Storage, Tape, Printers • Networking Switches, Firewalls & Routers • Each and every server, client (including mobile) and HW component in your enterprise • Nearly everything includes an OS and/or FW • Where there is code, a vulnerability is a possibility & likely exists Staying current on fixes is not just a client and server problem. The vulnerabilities affect most everything in your enterprise. 12
- 13. Security Fixes IBM i Security PTF Group • Not all PTFs/Fixes can be added to the Security PTF Group because of installation requirements! • Java updates • IBM i Access • Web and Application Servers • Lotus Products • etc. IBM My Notifications (Customer Subscription) • Security Bulletins • Technotes If necessary, contact IBM support for registration instructions 13
- 14. Virus Scanning for IBM i & Ransomware 14
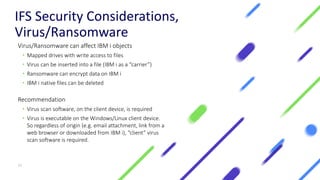
- 15. IFS Security Considerations, Virus/Ransomware Virus/Ransomware can affect IBM i objects • Mapped drives with write access to files • Virus can be inserted into a file (IBM i as a “carrier”) • Ransomware can encrypt data on IBM i • IBM i native files can be deleted Recommendation • Virus scan software, on the client device, is required • Virus is executable on the Windows/Linux client device. So regardless of origin (e.g. email attachment, link from a web browser or downloaded from IBM i), “client” virus scan software is required. 15
- 16. IBM i Server Security
- 17. System Security Levels System Value: QSECURITY 17
- 18. Security Levels ̶ Why Run at a High Level? System security level 50... Good reasons to run there. The System Integrity support, listed here, is activated: 18 1. Object Domain Checking 2. Hardware storage protection 3. Parameter validation Running at security level 40 and 50 is required as these two security levels support the integrity protection that all other security levels DO NOT!
- 19. Authority Checking and Integrity Support at Levels 40 & 50 User written programs, running at security level 40 or 50, MUST use system interfaces (commands and APIs) to gain access to the objects. • Authority checking is enforced by the system interface • Parameter Validation is enforced • Object Domain checking is enforced • Object Hardware Storage Protection checking is enforced 19 Direct access [defined as “direct object access via address”] by user programs to system objects is not allowed at Security Levels 40 and 50 due to domain and hardware storage protection attributes
- 21. Securing Service Tools Controlling access to the Service Tools is necessary for a secure system • Create as few Service Tools User IDs (SST/DST) as possible • Create a Service Tool user with the same privileges as QSECOFR (QSECOFR can become disabled) • Never use QSECOFR Service Tool USERID (save the password in a secure location) DSPSSTUSR (Display Service Tool User CL command) • Command line interface to “audit” service tool users and privileges 21
- 22. System Value Settings NOTE: Lock down system values via SST after setting
- 23. Auditing Related System Values QAUDCTL - Audit on/off switch QAUDLVL and QAUDLVL2 QAUDENDACN and QAUDFRCLVL - Use default values QCRTOBJAUD - Audit newly created objects 23 NOTE: See chapter 9 and appendix E & F of the security reference .pdf for audit doc
- 24. Auditing Continued Create the QAUDJRN audit journal Set QAUDCTL to *OBJAUD, *AUDLVL and *NOQTEMP Set QAUDLVL to *AUDLVL2 Set system wide auditing values in QAUDLVL2 sysval • Many QAUDLVL2 values exist, see QAUDLVL2 help text Audit sensitive objects via CHGOBJAUD 24 Turn on audit and save the audit journal receivers. You may need the audit data in the future!
- 25. Auditing Continued – Data Objects Security Audit provides who accesses what object A combination of security audit and “data object” journaling provides the complete audit trail Turn on journaling for *FILE and IFS *STMF sensitive objects to get the complete audit of changes, including change to data • CRTJRNRCV JRNRCV(MYLIB/MYRCV0001) • CRTJRN JRN(MYLIB/MYJRN) JRNRCV(MYLIB/MYRCV0001) • STRJRNPF FILE(MYLIB/MYFILE) JRN(MYLIB/MYJRN) IMAGES(*BOTH) • QSYS/STRJRN OBJ(('/mydir/dir1/stmf1' *INCLUDE)) JRN('/qsys.lib/mylib.lib/myjrn.jrn') 25
- 26. Assure Security from Syncsort is available to monitor and report: • View and report on audit data • Control and Monitor object level access (DB2 and IFS) • Monitor & Report on security configuration • And send the information to a SIEM (QRadar, SPLUNK, etc) Web-based dashboard to monitor and report on IBM i security and audit Monitoring and Reporting for Compliance 26
- 27. WRKSYSVAL SYSVAL(QPWD*) • Set password composition rule system values • Min/Max length, required characters, etc • Consider using enhanced password support (QPWDLVL) • Case sensitive long passwords (128 characters) Use the ANZDFTPWD command to check for default passwords Password Composition System Values 27 NOTE: Passwords are well protected when on IBM i but can be exposed when saved and on media. They are encrypted on the save media but subject to a brute force attack.
- 28. WRKSYSVAL SYSVAL(*SEC) for the entire list • QINACTITV - Set to a reasonable number of minutes • QINACTMSGQ - *ENDJOB/*DSCJOB • QMAXSIGN - Consider setting to 3 • QMAXSGNACN - Set to disable profile • QALWOBJDIF, QVFYOBJRST and QFRCCVNRST – control object restore • QNET* - Network Auditing • QSSL* - Control system SSL parameters Additional Security Related System Values 28
- 29. Resource Security Resource Security - Protecting your Objects
- 30. • Network security • Firewalls, IDS/IPS, network segmentation, etc. • Deploy a network security product • “Lock down” IBM i doors & windows (ODBC, FTP, DRDA, etc.) • Multi-factor authentication • Secure sensitive data (*FILE, *STMF, etc.) • Object level authority, public(*exclude) where appropriate • Use Journal to log changes for *FILE and *STMF objects • RCAC (Row and Column Access Control) • Deploy file level protection • Encrypt “confidential” data • Db2 field procedures, tokenization and encryption, for “at rest on media” • Audit sensitive objects and security configuration • Auditing, monitoring and reporting • Monitor security configuration to ensure settings are accurately set Resource Security – A Layered Approach = Assure Security 30
- 31. IBM i OS provides an excellent base security infrastructure However, an intruder who gains access and has complete privileges (security officer authority) has full access and must be stopped before entry into the system or stopped before sensitive data is compromised. Syncsort’s Assure Security provides additional layers of protection • Network security and audit • Monitoring and report for compliance • Elevated authority management • Multi-factor authentication • Encryption and encryption key management • SIEM integration • And much more! Resource Security – Privilege User Concerns 31
- 32. Resource Security – Network Layer 32 Locking the IBM i doors and windows – keeping the intruder out • Minimal support in the IBM i OS – authentication via passwords or Kerberos Syncsort’s Assure Security provides the network layer of protection • Network security and audit • Define rules to block access INTO IBM i • Define rules to block access once the user has authenticated • Plus multi-factor authentication • And monitoring, reporting with SIEM integration
- 33. Keep the number of security officers and security administrators to a minimum • *ALLOBJ, *SECADM, etc. special authority • Service tool userIDs • Syncsort’s Elevated Authority Manager minimizes the need for powerful profiles Audit the actions of the Powerful user • CHGUSRAUD CL command • *CMD action audit value, *SECURITY, etc. • Control and Monitor users via Assure Security Resource Security – Restrict Powerful Users 33 Make sure the security officer understands, procedurally, that audit cannot be turned OFF!
- 34. Protecting your objects with resource security is necessary to protect your data • Run at a security level 50 • Secure your confidential data with *EXCLUDE public authority • *USE access for Db2 and IFS stream files exposes data • Objects that are not security sensitive (public objects) should be protected with *USE public authority. This gives good performance for read operations on the object. • Add Layers of security via Assure Security • Network, Monitoring and Reporting, Encryption, MFA, etc. Resource Security - Protecting your Objects 34
- 35. Row and Column Access Control Release 7.2 - RCAC
- 36. Additional layer of data security available with Db2 in 7.2 Complementary to table level security (object authority checking) Controls access to table data at the ROW, COLUMN or BOTH Two sets of rules • Permissions for rows • Masks for columns IBM Advanced Data Security for i • No-charge feature, OS Option 47 required for RCAC What is RCAC (Row & Column Access Control)? IBM Advanced Data Security for i (Boss option 47) No Charge http://www.redbooks.ibm.com/redbooks.nsf/RedpieceAbstracts/ redp5110.html?Open 36
- 37. View the data via “Run SQL Scripts” and SQL “select” statement & RUNQRY • iNav session user is “UEHLING” & no group profile Example: Multi-Row *FILE with Row Permissions and Column Mask Enabled Select all rows from table EMPTBL via select * from empdta.emptbl results Row Permissions and Column Masking activated 37
- 38. NOTE: See chapter 10 of the Security Reference PDF in the IBM Knowledge Center for Authority Collection documentation Release 7.3 & 7.4 Authority Collection, Managing Object Level Authority
- 39. Customers run many applications on a single partition • No detailed knowledge of the applications… where is the data? • Data in Db2 or IFS … but where? • Once found, how do you lock down security without application breakage? • What is the “minimum” authority level that can be granted for the end user? • Many customers have little to no knowledge of what interfaces an application uses so the authority requirements cannot be determined • Applications are shipped with excessive public authority (common problem) which leads to security exposures Security and Compliance - The Issue 39 Locking Down Object Level Authority
- 40. Build a utility that captures pertinent data associated with an authority check (included as part of the base OS) • The collection covers all native IBM i file systems • Focus on capturing only unique instances of the authority check • Run-time performance, while the collection is active, will degrade 2-3% • Storage consideration for long running authority collection The collection includes key pieces of information… (including) “What authority is required for this authority check?” Solution: Authority Collection 40
- 41. • The Authority Collection is “User Based” in the 7.3 release • Collect authority info for objects accessed by this user • Provide both “User Based” and “Object Based” Authority Collection in 7.4 • Turn on the authority collection for an object(s) in QSYS or IFS file system • Collect authority info for “EVERY USER” that accesses the object • When a user accesses an object, collect authority info for this user • The equivalent authority information, as user based, will be collected • Output the data via the SQL view Release 7.3 & 7.4 Object Level Authority Collection 41
- 42. Authority Collection – View SELECT * FROM qsys2.authority_collection where user_name = ‘FRED1’ 42
- 43. Authority Collection – View Scrolling Right within the Authority Collection Data 43
- 44. IBM i Encryption Protecting your Data
- 45. A data encryption key should be well protected or data is exposed • Key is used to encrypt data (SSN’s, credit card numbers, etc.) It is recommended to encrypt the data key with a key encrypting key (KEK) • Used to encrypt data encryption keys A Master Key can then be used to encrypt all KEKs • A master key is used to encrypt KEKs or Data Encryption Keys • Top level key, in the clear! If master key is compromised, data is compromised. • How do you securely store this master key? Cryptographic Key Protection - Terminology 1 2 3KEK2 1 2 3 KEK1 Master Clear Text NOTE: Encryption Algorithms are public knowledge, encryption keys must be kept secret and protected 45
- 46. Encryption Key Management & Algorithms IBM i has GUI, CL & API interfaces to manage & use master keys, keystore files and encryption algorithms • Included as part of the base OS Syncsort’s Assure Security provides NIST-compliant encryption in its Assure Encryption module • NIST-compliant encryption algorithms Syncsort provides key management via tight integration with encryption products • Local encryption key management • Off-partition encryption key management with FIPS certification via Townsend Security 46
- 47. Db2 column level (field) exit support • Exit program (FieldProc) called on insert/update/read of a column • Similar to “Triggers” but additional support to enable encryption • Masking of Data is also supported IBM i enables column level encryption • Support to enable the Encrypt/Decrypt data in a Db2 column • No need to change column attributes like field length or data type • No application changes required • Encryption & key management must be implemented by the Field Procedure software Syncsort’s Assure Security available for Db2 field procedures and key management Db2 Field Procedures 47
- 48. Tokenization 48 IBM i has no OS support for tokenization Assure Security provides the tokenization solution • Tokenization provides the ability to replace sensitive data, such as a credit card number with a token that represents the sensitive data. • The sensitive data is stored in a token vault, usually off the partition. The token cannot be used to directly obtain the credit card number. • Tokenization is a popular technique for PCI (payment card industry) compliance.
- 49. Encryption of data on tape & disk (HW technologies are recommended for optimal performance) • SW Encrypted backup. Provides encryption support for tape/virtual tape via BRMS and tape management APIs (OS option 44) • HW encrypted backup solutions • SW Encrypted ASP. Provides disk level encryption support for all data written to disk (OS option 45) • HW support for Disk level encryption Encryption key management is required (master keys and data encryption keys) Encryption of Data “at Rest” 49
- 50. Conclusion – Resource Security ✓ Protecting your objects with resource security is necessary to protect your data ✓ Run at a high security level ✓ Secure your confidential data with a combination of authority and encryption ✓ Add Layers of security via Syncsort’s Assure Security ✓ Network control ✓ Monitoring & reporting ✓ Audit and data protection via encryption ✓ Multi-factor authentication ✓ Elevated authority management ✓ And more 50
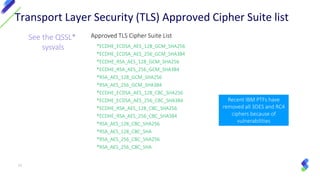
- 52. Best Practices for network connections to and from your system (client/server applications): • TLS1.2 is the current “gold” standard for secure client/server app’s • PCI requirement in June 2018 (TLS 1.1 or TLS 1.2) • TLS 1.1 & 1.2 support exists in 7.1 and 7.2 • What is TLS? • SSL follow-on protocol to encrypt network application data flow • A mixture of TLS enabled and non-TLS enabled applications can be run from the system (secure/unsecure conversations) • Cipher Suite (encryption) strength needs to stay current. Application Security: Secure Socket Layer (SSL) & Transport Layer Security (TLS) 52 NOTE: All versions of SSL and TLS 1.0 have been deemed unsecure and should never be used!
- 53. Approved TLS Cipher Suite List *ECDHE_ECDSA_AES_128_GCM_SHA256 *ECDHE_ECDSA_AES_256_GCM_SHA384 *ECDHE_RSA_AES_128_GCM_SHA256 *ECDHE_RSA_AES_256_GCM_SHA384 *RSA_AES_128_GCM_SHA256 *RSA_AES_256_GCM_SHA384 *ECDHE_ECDSA_AES_128_CBC_SHA256 *ECDHE_ECDSA_AES_256_CBC_SHA384 *ECDHE_RSA_AES_128_CBC_SHA256 *ECDHE_RSA_AES_256_CBC_SHA384 *RSA_AES_128_CBC_SHA256 *RSA_AES_128_CBC_SHA *RSA_AES_256_CBC_SHA256 *RSA_AES_256_CBC_SHA Transport Layer Security (TLS) Approved Cipher Suite list See the QSSL* sysvals Recent IBM PTFs have removed all 3DES and RC4 ciphers because of vulnerabilities 53
- 54. Certificate Types • ECDSA (Eliptic Curve Digital Signature Algorithm), newer technology • Key size of 256 or 384 • RSA (Rivest–Shamir–Adleman) • Key size of 2048 or 4096 bits (4096 is more secure, but may affect performance) • Note: 1024 bit keys are not secure and not trusted by browsers Secure Hash Algorithms A hash algorithm is used when signing the certificate by the Certificate Authority • SHA 2: 256 or 384 bits are acceptable • Note: SHA 1 hash is not secure and not trusted by browsers Certificate Validity Periods Certificates should be occasionally replaced and acceptable algorithms used • Standard certificates are valid for 1 year • Extended validation certs may be good for 2 years • Some free certificates expire every 90 days Digital Certificates: Best Practices 54
- 56. Assure Security A comprehensive solution that addresses all aspects of IBM i security and helps to ensure compliance with cybersecurity regulations. Whether your business needs to implement a full set of security capabilities, or you need to address a specific vulnerability, Assure Security is the solution. 56
- 57. SIEM Integration Integrate IBM i security data with data from other platforms by transferring it to a Security Information and Event Management console System & Database Auditing Simplify analysis of IBM i journals to monitor for security incidents and generate reports and alerts Assure Compliance Monitoring Db2 Data Monitoring Monitor for views of sensitive Db2 data and optionally block data from view 57
- 58. Multi-Factor Authentication Strengthen login security by requiring multiple forms of authentication Elevated Authority Management Automatically elevate user authority as-needed and on a limited basis Access Control Secure all points of entry into to your system including network access, database access, command line access and more Assure Access Control 58
- 59. Secure File Transfer Securely transfer files across internal or external networks using encryption Tokenization Remove sensitive data from a server by replacing it with substitute values that can be used used to retrieve the original data Encryption Transform human-readable data into unreadable cypher text using industry-certified encryption & key management solutions Assure Data Privacy 59
- 60. Security Risk Assessment Service Let Syncsort’s security experts conduct a thorough risk assessment and provide a report with remediation guidance Security Risk Assessment Tool Thoroughly check all aspects of IBM i security and obtain detailed reports and recommendations Assure Security Risk Assessment 60
- 62. • Perform a security assessment • Set the security-related System Values & lock them down • Use the Security Audit Journal • Protect your sensitive objects with object security and encryption • Add layers of security with Syncsort’s Assure Security • Network access control • Multi-factor authentication • Elevated authority management • Data protection • Monitoring & reporting • And more Presentation Summary 62 Learn more at www.syncsort.com/assure-security Syncsort can help with all your IBM i Security needs!
- 63. Learn more Download our white paper out “The Essential Layers of IBM i Security” About layers of IBM i security by visiting the Syncsort website 63


















![Authority Checking and Integrity
Support at Levels 40 & 50
User written programs, running at security level 40 or 50,
MUST use system interfaces (commands and APIs) to gain
access to the objects.
• Authority checking is enforced by the system interface
• Parameter Validation is enforced
• Object Domain checking is enforced
• Object Hardware Storage Protection checking is enforced
19
Direct access [defined as “direct object access via
address”] by user programs to system objects is not
allowed at Security Levels 40 and 50 due to domain
and hardware storage protection attributes](https://image.slidesharecdn.com/dawebcast-ibm-systems-media-best-practices-in-ibm-i-security-q4-2019pdf-191016163547/85/Best-Practices-in-IBM-i-Security-19-320.jpg)