Android secure coding
- 1. © Blueinfy Solutions Secure Coding For Android Applications
- 2. © Blueinfy Solutions Local Storage - Example • Remember me option – NOT SECURE WAY
- 3. © Blueinfy Solutions Token stored • On local file – NOT SECURE WAY
- 4. © Blueinfy Solutions Shared Preferences • SHARED PREFERENCE – NOT SECURE WAY
- 5. © Blueinfy Solutions Writing to file • When opening file for writing, make sure to open it in private mode as shown below – String FILENAME = “temp"; String string = “token”; FileOutputStream fos = openFileOutput(FILENAME, Context.MODE_PRIVATE); fos.write(string.getBytes()); fos.close();
- 6. © Blueinfy Solutions Local Storage – Secure Method • Encrypt the data using strong encryption, possibly AES • Do not decrypt the data at client side • Send Encrypted Data to the server • Server decrypts the data before validating it
- 7. © Blueinfy Solutions Securing Secrets • AES encryption to store secret information and making secure storage. • APIs and Libs for it. • Random cookies and keys. • Not to open and shared storage. • Cache and File writing is not enough. • Design level strategy for it.
- 8. © Blueinfy Solutions Secure Method – Sample Code
- 9. © Blueinfy Solutions Sending Encrypted in JSON
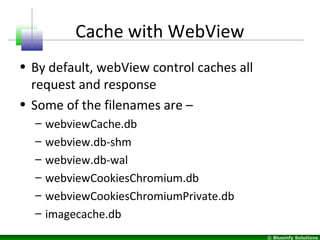
- 11. © Blueinfy Solutions Cache with WebView • By default, webView control caches all request and response • Some of the filenames are – – webviewCache.db – webview.db-shm – webview.db-wal – webviewCookiesChromium.db – webviewCookiesChromiumPrivate.db – imagecache.db
- 12. © Blueinfy Solutions Sample code to clear the cache
- 13. © Blueinfy Solutions SSL Implementation • Application sends request to server over SSL (Secure Way) • Most application fails to handle SSL certificate validation error on the client side • Only certificate from the OWNER server and sub-domain should be allowed
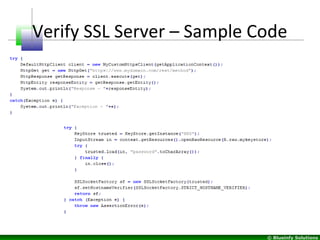
- 14. © Blueinfy Solutions Verify SSL Server – Sample Code
- 15. © Blueinfy Solutions Copy/Paste in the text fields • Services are shared between all the applications • Attacker can write malicious program to monitor clipboard to get access to sensitive data if copy/paste is not disabled • Copy/Paste must be disabled on the sensitive fields
- 16. © Blueinfy Solutions Screenshot in temporary files • Pressing HOME button takes screenshot of the last screen and saves it in local storage • To disable this, manifest file needs to be updated under Activity Tag
- 17. © Blueinfy Solutions Protecting IP • Unlike iOS, there is no encryption supported by android platform • Possible to Decompile binary and get access to source code • “ProGuard” can be leveraged to protect against Decompile
- 18. © Blueinfy Solutions Code Analysis with AppCodeScan • Semi automated tool • Ability to expand with custom rules • Simple tracing utility to verify and track vulnerabilities • Simple HTML reporting which can be converted to PDF
- 19. © Blueinfy Solutions Sample Rules - Android