Ad
Building a Security Operations Center (SOC).pdf
- 1. Session ID: Session Classification: Ben Rothke, CISSP CISM Wyndham Worldwide Corp. Building a Security Operations Center (SOC) TECH-203 Advanced
- 2. About me… ƒ Ben Rothke, CISSP, CISM, CISA ƒ Manager - Information Security - Wyndham Worldwide Corp. ƒ All content in this presentation reflect my views exclusively and not that of Wyndham Worldwide ƒ Author - Computer Security: 20 Things Every Employee Should Know (McGraw-Hill) ƒ Write the Security Reading Room blog ƒ https://365.rsaconference.com/blogs/securityreading 2
- 3. Agenda ƒ Introduction ƒ Need for a Security Operations Center (SOC) ƒ Components of an effective SOC ƒ Deciding to insource or outsource the SOC ƒ Outsourced SOC = MSSP ƒ SOC requirements ƒ Q/A 3
- 4. Building a Security Operations Center (SOC) 4
- 5. Current information security challenges ƒ Onslaught of security data from disparate systems, platforms and applications ƒ numerous point solutions (AV, firewalls, IDS/IPS, ERP, access control, IdM, SSO, etc.) ƒ millions / billions of messages daily ƒ attacks becoming more frequent / sophisticated ƒ regulatory compliance issues place increasing burden on systems and network administrators 5
- 6. Why do you need a SOC? ƒ because a firewall and IDS are not enough ƒ nucleus of all information security operations ƒ provides ƒ continuous prevention ƒ protection ƒ detection ƒ response capabilities against threats, remotely exploitable vulnerabilities and real-time incidents on your networks ƒ works with CIRT to create comprehensive infrastructure for managing security operations 6
- 7. SOC benefits ƒ speed of response time ƒ malware can spread throughout the Internet in minutes or even seconds, potentially knocking out your network or slowing traffic to a crawl ƒ consequently, every second counts in identifying these attacks and negating them before they can cause damage ƒ ability to recover from a DDoS attack in a reasonable amount of time 7
- 9. SOC functions ƒ Real-time monitoring / management ƒ aggregate logs ƒ aggregate data ƒ coordinate response and remediation ƒ Reporting ƒ executives ƒ auditors ƒ security staff ƒ Post-incident analysis ƒ forensics ƒ investigation 9
- 10. SOC planning ƒ full audit of existing procedures, including informal and ad-hoc ƒ planning of location, resources, training programs, etc. ƒ plans change; don’t try to prepare everything ahead of time ƒ sometimes best approach is not clear until you have actually started ƒ build it like aircraft carrier - change built into design 10
- 11. SIM/SIEM/SEM tools ƒ Many SOC benefits come from good SIM tool ƒ consolidates all data and analyzes it intelligently ƒ provides visualization into environment ƒ Choose SIM that’s flexible and agile, plus: ƒ track and escalate according to threat level ƒ priority determination ƒ real-time correlation ƒ cross-device correlation ƒ audit and compliance 11
- 12. Challenge of SIM & automation ƒ A well-configured SIM can automate much of the SOC process. But… ƒ “The more advanced a control system is, so the more crucial may be the contribution of the human operator” ƒ Ironies of Automation - Lisanne Bainbridge ƒ discusses ways in which automation of industrial processes may expand rather than eliminate problems with the human operator ƒ don’t get caught in the hype that a SIM can replace good SOC analysts ƒ no secret that they can’t 12
- 13. Which SOC? ƒ Outsourced ƒ Symantec, SecureWorks (Dell), Solutionary, WiPro, Tata, CenturyLink (Savvis, Qwest), McAfee, Verizon (Cybertrust / Ubizen), Orange, Integralis, Sprint, EDS, AT&T, Unisys, VeriSign, BT Managed Security Solutions (Counterpane), NetCom Systems and more ƒ Centralized group within enterprise ƒ Corporate SOC 13
- 14. In-house SOC vs. outsourced MSSP 14 The Business Case for Managed Security Services Managed Security Services Providers vs. SIEM Product Solutions http://www.solutionary.com/dms/solutionary/Files/whitepapers/MSSP_vs_SIEM.pdf
- 15. Define the SOC requirements ƒ define specific needs for the SOC within the organization ƒ what specific tasks will be assigned to the SOC? ƒ detecting external attacks, compliance monitoring, checking for insider abuse, incident management, etc. ƒ who will use the data collected and analyzed by the SOC? ƒ what are their requirements? ƒ who will own and manage the SOC? ƒ types of security events will be fed into the SOC 15
- 16. Internal SOC 16 Advantages Disadvantages ƒ dedicated staff ƒ knows environment better than a third-party ƒ solutions are generally easier to customize ƒ potential to be most efficient ƒ most likely to notice correlations between internal groups ƒ logs stored locally • larger up-front investment • higher pressure to show ROI quickly • higher potential for collusion between analyst and attacker • less likely to recognize large-scale, subtle patterns that include multiple groups • can be hard to find competent SOC analysts
- 17. Internal SOC - Questions 1. does your staff have the competencies (skills and knowledge) to manage a SOC? 2. how do you plan to assess if they really do have those competencies? 3. are you willing to take the time to document all of the SOC processes and procedures? 4. who’s going to develop a training program? 5. who’s going to design the physical SOC site? 6. can you hire and maintain adequate staff levels? 17
- 18. Internal SOC success factors 1. Trained staff 2. good SOC management 3. adequate budget 4. good processes 5. integration into incident response ƒ If your organization can’t commit to these five factors, do not build an internal SOC – it will fail ƒ will waste money and time and create false sense of security ƒ if you need a SOC but can’t commit to these factors, strongly consider outsourcing 18
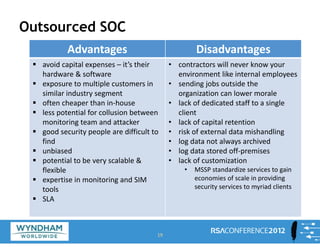
- 19. Outsourced SOC 19 Advantages Disadvantages ƒ avoid capital expenses – it’s their hardware & software ƒ exposure to multiple customers in similar industry segment ƒ often cheaper than in‐house ƒ less potential for collusion between monitoring team and attacker ƒ good security people are difficult to find ƒ unbiased ƒ potential to be very scalable & flexible ƒ expertise in monitoring and SIM tools ƒ SLA • contractors will never know your environment like internal employees • sending jobs outside the organization can lower morale • lack of dedicated staff to a single client • lack of capital retention • risk of external data mishandling • log data not always archived • log data stored off‐premises • lack of customization • MSSP standardize services to gain economies of scale in providing security services to myriad clients
- 20. Outsourced SOC – general questions 1. Can I see your operations manual? 2. what is its reputation? 3. who are its customers? 4. does it already service customers in my industry? 5. does it service customers my size? 6. how long have its customers been with it? 7. what is its cancellation/non-renew rate? 8. how do they protect data and what is the level of security at their SOC? 20
- 21. Outsourced SOC – staffing questions 1. what is the experience of its staff? 2. does it hire reformed hackers? 3. are background checks performed on all new employees? 4. does it use contractors for any of its services? 5. are personnel held to strict confidentiality agreements? 6. what is the ratio of senior engineers to managed clients? 7. what certifications are held by senior/junior staff? 8. what is its employee turnover rate? 21
- 22. Outsourced SOC – stability questions 1. Is it stable? 2. does it have a viable business plan? 3. how long has it been in business? 4. positive signs of growth from major clients? 5. consistent large account wins / growing revenue? 6. what is its client turnover rate? 7. what are its revenue numbers? ƒ If private and unwilling to share this information, ask for percentages rather than actual numbers 8. will it provide documentation on its internal security policies and procedures? 22
- 23. Outsourced SOC - sizing / costs ƒ should provide services for less than in-house solution ƒ can spread out investment in analysts, hardware, software, facilities over several clients ƒ how many systems will be monitored? ƒ how much bandwidth is needed? ƒ potential tax savings ƒ Convert variable costs (in-house) to fixed costs (services) 23
- 24. Outsourced SOC – performance metrics ƒ must provide client with an interface providing detailed information ƒ services being delivered ƒ how their security posture relates to overall industry trends ƒ provide multiple views into the organization ƒ various technical, management and executive reports ƒ complete trouble ticket work logs and notes 24
- 25. Outsourced SOC – SLA’s ƒ well-defined SLA’s are critical ƒ processes and time periods within which they will respond to any security need. ƒ SLA should include specific steps to be taken ƒ procedures the company takes to assure that the same system intrusions do not happen again ƒ guarantee of protection against emerging threats ƒ recovers losses in the event service doesn’t deliver as promised ƒ commitments for initial device deployment, incident response/protection, requests for security policy & configuration changes, acknowledgement of requests 25
- 26. Outsourced SOC - Transitioning ƒ ensure adequate knowledge transfer ƒ create formal service level performance metrics ƒ establish a baseline for all negotiated service levels ƒ measure from the baseline, track against it, adjusting as necessary. ƒ create internal CIRT ƒ identify key events and plan the response ƒ hold regular transition & performance reviews ƒ be flexible ƒ schedule formal review to adjust SLA’s after 6 months of service operation and periodically thereafter 26
- 27. Outsourced SOC – Termination ƒ all outsourcing contracts must anticipate the eventual termination at the end of the contract ƒ plan for an orderly in-house transition or a transition to another provider ƒ develop an exit strategy ƒ define key resources, assets and process requirements for continued, effective delivery of the services formerly provided by the outgoing provider 27
- 28. Outsourcing: don’t just trust - verify ƒ Call Saturday night 2AM ƒ Who’s answering? Do they sound competent? ƒ Reports ƒ Are they to your liking? Can they create complex reports? ƒ Set off a few alarms ƒ Are they calling/alerting you in a timely manner? ƒ True process for real-time threat analysis? ƒ Or simply a glorified reporting portal that looks impressive 28
- 29. Mike Rothman on MSSP ƒ We have no illusions about the amount of effort required to get a security management platform up and running, or what it takes to keep one current and useful. ƒ Many organizations have neither the time nor the resources to implement technology to help automate some of these key functions. ƒ So they are trapped on the hamster wheel of pain, reacting without sufficient visibility, but without time to invest in gaining that much-needed visibility into threats without diving deep into raw log files. ƒ A suboptimal situation for sure, and one that usually triggers discussions of managed services in the first place. 29 http://securosis.com/blog/managed-services-in-a-security-management-2.0-world November 2011
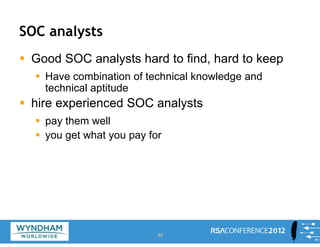
- 30. SOC analysts ƒ Good SOC analysts hard to find, hard to keep ƒ Have combination of technical knowledge and technical aptitude ƒ hire experienced SOC analysts ƒ pay them well ƒ you get what you pay for 30
- 31. SOC analyst – skill sets 31 • O/S proficiency • network protocols • chain of custody issues • ethics • corporate policy • services • multiple hardware platforms • attacks • directories • routers/switches/firewall • programming • forensics • databases • IDS • investigative processes • applications • and much more
- 32. SOC analyst - qualities ƒ extremely curious ƒ ability to find answers to difficult problems / situations ƒ abstract thinker ƒ can correlate IDS incidents and alerts in real-time ƒ ethical ƒ deals with low-level details while keeping big- picture view of situation ƒ can communicate to various groups that have very different requirements ƒ responds well to frustrating situations 32
- 33. SOC analyst burnout ƒ SOC analysts can burnout ƒ have a plan to address this ƒ extensive training ƒ bonuses ƒ promotions ƒ management opportunities ƒ job rotation 33
- 34. SOC management ƒ management and supervision of a SOC is a key factor to ensure its efficiency ƒ while analysts, other staff, hardware and software are key elements, a SOC’s ultimate success is dependent on a competent SOC manager. ƒ inadequate/poor management has significant consequences ƒ from process performance decrements, to incidents being missed or incorrectly handled 34
- 35. SOC processes and procedures ƒ SOC heavily process-driven ƒ processes work best when documented in advance ƒ usability and workflow critical ƒ documentation ƒ adequate time must be given to properly document many different SOC functions ƒ corporate networks and SOC are far too complex to be supported in an ad-hoc manner ƒ documentation makes all the difference 35
- 36. Sample SOC runbook table of contents 36
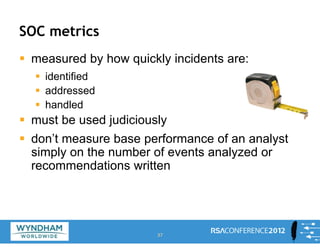
- 37. SOC metrics ƒ measured by how quickly incidents are: ƒ identified ƒ addressed ƒ handled ƒ must be used judiciously ƒ don’t measure base performance of an analyst simply on the number of events analyzed or recommendations written 37
- 39. Apply 39
- 40. Apply ƒ obtain management commitment to a SOC ƒ ensuring adequate staffing and budget ƒ define your SOC requirements ƒ decide to have SOC in-house or outsourced ƒ in-house – create detailed and customized processes ƒ outsourced – ensure their process meets your requirements ƒ create process to ensure SOC is effective and providing security benefits to the firm 40
- 41. Ben Rothke, CISSP CISM Manager – Information Security Wyndham Worldwide Corporation www.linkedin.com/in/benrothke www.twitter.com/benrothke www.slideshare.net/benrothke 41