Ad
Cloud Computing Security
- 2. The HypeCluster ComputingCloud ComputingGrid Computing
- 4. “What the hell is Cloud Computing?”- Larry Ellison
- 5. 5th Generation of Computing 1970s 1980s 1990s 2000s 2009+Monolithic Client-Server Web SOA Cloud Services
- 6. Wikipedia’s DefinitionsCloud computing is a computing paradigm shift where computing is moved awayfrom personal computers or an individual server to a “cloud” of computers. – 12/2007Cloud computing is Internet-based ("cloud") development and use of computerTechnology ("computing"). The cloud is a metaphor for the Internet, based on howit is depicted in computer network diagrams, and is an abstraction for the complexinfrastructure it conceals. – 12/2008Cloud computing is a style of computing in which dynamically scalable and oftenvirtualized resources are provided as a service over the Internet. – 6/2009Cloud computing is an example of computing in which dynamically scalable andoften virtualized resources are provided as a service over the Internet. - Now
- 7. Common implies multi-tenancy, not single or isolated tenancy Location-independentOnlineUtility implies pay-for-use pricingDemand implies ~infinite, ~immediate, ~invisible scalability
- 8. Cloud Computing Infrastructure Models
- 9. Public CloudPublic CloudThe Cloud ProviderThe Cloud ProviderSMEHybrid CloudConnectivity(Network Access)SMEEnterprisePrivate CloudEnterpriseSMEPrivate Cloud
- 10. Architectural Layers of Cloud Computing
- 11. Software as a Service (SaaS)
- 12. Platform as a Service (PaaS)
- 13. Infrastructure as a Service (IaaS)
- 16. Comparisons
- 17. Cloud Computing EconomicsTraditional ITVariable Costs(OpEx)Cloud ComputingFixed Costs(CapEx)CostsVariable Costs(OpEx)Users
- 18. Pros and Cons
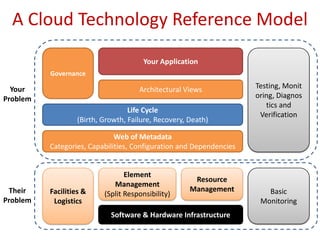
- 20. A Cloud Technology Reference ModelYour ApplicationTesting, Monitoring, Diagnostics and VerificationGovernanceArchitectural ViewsYourProblemLife Cycle(Birth, Growth, Failure, Recovery, Death)Web of MetadataCategories, Capabilities, Configuration and DependenciesResource ManagementBasic MonitoringFacilities & LogisticsElement Management(Split Responsibility)TheirProblemSoftware & Hardware Infrastructure
- 21. Software as a ServiceApplicationApplicationServerMiddlewareDatabaseOperating SystemHypervisorCPUNetworkingStorageYOUR DATABackupDatacenter (Power, Cooling, Physical Security)Your ProblemTheir Problem
- 22. Platform as a ServiceYour ApplicationApplicationServerMiddlewareDatabaseOperating SystemHypervisorCPUNetworkingStorageBackupDatacenter (Power, Cooling, Physical Security)Your ProblemTheir Problem
- 23. Infrastructure as a ServiceYour ApplicationYourApplicationServerYourMiddlewareYourDatabaseYour Operating SystemHypervisorCPUNetworkingStorageBackupDatacenter (Power, Cooling, Physical Security)Your ProblemTheir Problem
- 24. Security Issues
- 25. Overview
- 26. Selected Issues
- 27. Encryption & Key ManagementEncryption on StorageStorageEncryption on TransmissionKey ManagementInternet
- 28. Case StudyAmazon Web Services (AWS)
- 29. AWS Registration and Security
- 31. Multi-Factor AuthenticationAWS Multi-Factor Authentication (AWS MFA)
- 34. HMAC-SHA1
- 35. Summary & Predictions.. We think everyone on the planet deserves to have their ownvirtual data center in the cloud ..- Lew Tucker..Cloud Computing Will Be As Influential As E-business.. - Gartner.. one of the most important transformations the federalgovernment will go through in the next decade ..- Obama’s TIGR Team.. Who knew that the concept of security in cloud computing waseven possible to imagine?..- Scott Bradner
- 37. Thank You
Editor's Notes
- #2: Hello everybody, I am Ninh Nguyen, a CS student. My seminar topic today is Cloud Computing Security.
- #3: First of all, just take a look how people concern about cloud computing. As you can see in this graph, people has been searching a lot for cloud computing in Google since 2007 especially since the first months of 2009. And other kind of computing such as grid computing is falling and cluster computing is still the same for years.
- #4: At the same time, cloud computing also attracts a lot attention of media and news volume still growing over the time.
- #5: So what is cloud computing? I take a quote from Larry Ellison – CEO of Oracle: “What the hell is Cloud Computing?” Why did he say that? Actually, cloud computing is too new and has a standard.
- #6: Look at history, we can say Cloud Computing is the 5th generation of computing, after monolithic, client-server, web, service-oriented architecture and now it’s cloud service.
- #7: I have to say that there is not any formal definition and you can find out many different definitions of cloud computing out there. Here I took definitions on Wikipedia through out the time, since 12/2007. You can see people define cloud computing quite differently through the evolution of it.
- #8: Simply, I can summarize some characteristics of cloud computing. The first characters build up the word CLOUD and it’s very easy to remember. They’re Common, Location-independent, Online, Utility implies and Demand implies.The on-demand, self-service, pay-by-use modelInfrastructure is programmableApplications are composed and are built to be composableServices are delivered over the network
- #9: Then, I want to introduce about infrastructure models of cloud computing.
- #10: Basically there are three types of models. Public Cloud, Private Cloud and another type that mixes of public cloud and private cloud is hybrid cloud.Public clouds are run by third parties, and applications from different customers are likely to be mixed together on the cloud’s servers, storage systems, and networks. Public clouds are most often hosted away from customer premises, and they provide a way to reduce customer risk and cost by providing a flexible, even temporary extension to enterprise infrastructure.Private clouds are built for the exclusive use of one client, providing the utmost control over data, security, and quality of service. The company owns the infrastructure and has control over how applications are deployed on it. Private clouds may be deployed in an enterprise datacenter, and they also may be deployed at a co-location facility.Hybrid clouds combine both public and private cloud models. They can help to provide on-demand, externally provisioned scale. The ability to augment a private cloud with the resources of a public cloud can be used to maintain service levels in the face of rapid workload fluctuations.
- #11: Now I will talk about architectural layers of cloud computing. There are also 3 types SaaS, PaaS and IaaS.
- #12: Software as a service features a complete application offered as a service on demand. A single instance of the software runs on the cloud and services multiple end users or client organizations.
- #13: Platform as a service encapsulates a layer of software and provides it as a service that can be used to build higher-level services.Someone producing PaaS might produce a platform by integrating an OS,middleware, application software, and even a development environment that is then provided to a customer as a serviceSomeone using PaaS would see an encapsulated service that is presented to them through an API. The customer interacts with the platform through the API, and the platform does what is necessary to manage and scale itself to provide a given level of service.
- #14: Infrastructure as a service delivers basic storage and compute capabilities as standardized services over the network. Servers, storage systems, switches, routers, and other systems are pooled and made available to handle workloads that range from application components to high-performance computing applications.
- #15: To summarize, here is a diagram cover relationships among SaaS, PaaS, IaaS.
- #16: To clarify, I will talk about characteristics of cloud computing including of some comparisons, benefits – disadvantages and goal of cloud computing.
- #17: Grid computing has been used in environments where users make few but large allocation requestsCloud computing really is about lots of small allocation requests.
- #18: Diagram showing economics of cloud computing versus traditional IT, including capital expenditure (CapEx) and operational expenditure (OpEx)Cloud computing users can avoid capital expenditure (CapEx) on hardware, software, and services when they pay a provider only for what they use. Consumption is usually billed on a utility (e.g. resources consumed, like electricity) or subscription (e.g. time based, like a newspaper) basis with little or no upfront cost.
- #19: And now I can sum up pros and cons of cloud computing. One of cons is Security which I will talk about right now.
- #20: Now this is the second part of my talk: cloud computing security.
- #21: First of all, I will describe an overview about a cloud technology reference model. You never can control everything with cloud computing. There are always two problems, yours and theirs.
- #22: In SaaS, it’s your data.
- #23: In PaaS, it’s your whole application.
- #24: With IaaS, it’s a lot of things.
- #25: Now I will list here some security issues in cloud computing.
- #26: There’re two broad categories of issues: governing in the cloud and operating in the cloud.
- #27: Due to limit of time, I only choose 1 selected issue which has relations with my course: cryptography to present today. It’s encryption and Key Management.
- #28: Cloud computing changes the way we think about computing by removing the specifics of location from its resources. In other word, it abstracts all computing and networking resources. However, in divorcing components from location, this creates security issues that result from this lack of any perimeter. In such a world, there is only one way to secure the computing resources: strong encryption and scalable key management.From a risk management perspective, unencrypted data existent in the cloud may be considered “lost” by the customer. Application providers who are not controlling backend systems should assure that data is encrypted when being stored on the backend. Use encryption to separate data holding from data usage. Segregate the key management from the cloud provider hosting the data, creating a chain of separation. This protects both the cloud provider and customer from conflict when being compelled to provide data due to a legal mandate and can potentially solve some problems.When stipulating encryption in contract language, assure that the encryption is adhering to existing industry or government standards, as applicable.
- #29: Now I will talk about a case-study: Amazon Web Service or AWS. Amazon provides 2 kinds of service: Cloud Computing Service and Support Services.Amazon Simple Storage Service (S3)Amazon Elastic Compute Cloud (EC2)Amazon SimpleDBAmazon CloudFrontAmazon Simple Queue Service (SQS)Amazon Flexible Payments Service (FPS)Amazon Mechanical Turk
- #31: An X.509 Certificate consists of Public Key and a Private Key. The file containing the public key, the certificate file, must contain a base64-encoded DER certificate body. The file containing the private key, the Private Key file, must contain a base64-encoded PKCS#8 private key. The Private Key is used to authenticate requests to AWS.AWS accepts any syntactically and cryptographically valid X.509 certificates. They do not need to be from a formal Certificate Authority (CA).
- #35: Here is a diagram of SHA-1 HMAC Generation.In cryptography, a keyed-Hash Message Authentication Code (HMAC or KHMAC), is a type of message authentication code (MAC) calculated using a specific algorithm involving a cryptographic hash function in combination with a secret key. Any iterative cryptographic hash function, such as MD5 or SHA-1, may be used in the calculation of an HMAC.The SHA hash functions are a set of cryptographic hash functions designed by the National Security Agency (NSA) and published by the NIST as a U.S. Federal Information Processing Standard. SHA stands for Secure Hash Algorithm.SHA-1 (as well as SHA-0) produces a 160-bit digest from a message with a maximum length of (264 − 1) bits. SHA-1 is based on principles similar to those used by Ronald L. Rivest of MIT in the design of the MD4 and MD5 message digest algorithms, but has a more conservative design.
- #36: To summary and predict, I take some quote here:Cloud Computing is more and more popular but Cloud Computing Security is a very important problem everybody or company going to use CC should be concern.