Cloud Infrastructure Mechanisms
- 1. Cloud Infrastructure Mechanisms Sartaj Fatima Lecturer, Place photo here “Reference: Cloud Computing Concepts, Technology & Architecture. Thomas Erl, Zaigham Mahmood and Richardo Puttini.” 1 Mohammed Sajjad Ali PMP, CCNP, E-commerce
- 2. Contents : 7.1 Logical Network Perimeter 7.2 Virtual Server 7.3 Cloud Storage Device 7.4 Cloud Usage Monitor 7.5 Resource Replication 7.6 Ready-Made Environment Cloud Infrastructure Mechanisms “Cloud infrastructure mechanisms are foundational building blocks of cloud environments that establish primary artifacts to form the basis of fundamental cloud technology architecture.” 2
- 3. Cloud Infrastructure Mechanisms The following cloud infrastructure mechanisms are described in this chapter: • Logical Network Perimeter • Virtual Server • Cloud Storage Device • Cloud Usage Monitor • Resource Replication • Ready-Made Environment Not all of these mechanisms are necessarily broad-reaching, nor does each establish an individual architectural layer. Instead, they should be viewed as core components that are common to cloud platforms. 3
- 4. 7.1. Logical Network Perimeter Cloud Infrastructure Mechanisms Defined as the isolation of a network environment from the rest of a communications network, thelogical network perimeter establishes a virtual network boundary that can encompass and isolate a group of related cloud-based IT resources that may be physically distributed. (Figure 7.1). Figure 7.1. The dashed line notation used to indicate the boundary of a logical network perimeter. This mechanism can be implemented to: • Isolate IT resources in a cloud from non-authorized users • Isolate IT resources in a cloud from non-users • Isolate IT resources in a cloud from cloud consumers • Control the bandwidth that is available to isolated IT resources Logical network perimeters are typically established via network devices that supply and control the connectivity of a data center and are commonly deployed as virtualized IT environments that include: • Virtual Firewall – An IT resource that actively filters network traffic to and from the isolated network while controlling its interactions with the Internet. 4
- 5. Cloud Infrastructure Mechanisms • Virtual Network – Usually acquired through VLANs, this IT resource isolates the network environment within the data center infrastructure. Figure 7.2 introduces the notation used to denote these two IT resources. Figure 7.3 depicts a scenario in which one logical network perimeter contains a cloud consumer’s on-premise environment, while another contains a cloud provider’s cloud-based environment. These perimeters are connected through a VPN that protects communications, since the VPN is typically implemented by point-to-point encryption of the data packets sent between the communicating endpoints. Figure 7.2. The symbols used to represent a virtual firewall (top) and a virtual network (bottom). 5
- 6. Cloud Infrastructure Mechanisms Figure 7.3. Two logical network perimeters surround the cloud consumer and cloud provider environments. 6
- 7. Cloud Infrastructure Mechanisms Figure 7.4. A logical network layout is established through a set of logical network perimeters using various firewalls and virtual networks. 7
- 8. Cloud Infrastructure Mechanisms A virtual server is a form of virtualization software that emulates a physical server. Virtual servers are used by cloud providers to share the same physical server with multiple cloud consumers by providing cloud consumers with individual virtual server instances. Figure 7.5 shows three virtual servers being hosted by two physical servers. The number of instances a given physical server can share is limited by its capacity. The virtual server represents the most foundational building block of cloud environments. Each virtual server can host numerous IT resources, cloud-based solutions, and various other cloud computing mechanisms. Cloud consumers that install or lease virtual servers can customize their environments independently from other cloud consumers that may be using virtual servers hosted by the same underlying physical server. Figure 7.6 depicts a virtual server that hosts a cloud service being accessed by Cloud Service Consumer B, while Cloud Service Consumer A accesses the virtual server directly to perform an administration task. 7.2. Virtual Server Figure 7.5. The first physical server hosts two virtual servers, while the second physical server hosts one virtual server. 8
- 9. Cloud Infrastructure Mechanisms Figure 7.7. Virtual servers are created via the physical servers’ hypervisors and a central VIM 9
- 10. Cloud Infrastructure Mechanisms Figure 7.6. A virtual server hosts an active cloud service and is further accessed by a cloud consumer for administrative purposes. 10
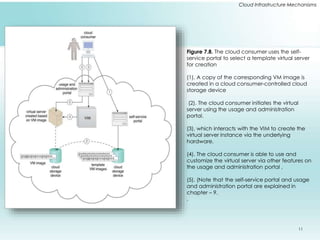
- 11. Cloud Infrastructure Mechanisms Figure 7.8. The cloud consumer uses the self-service portal to select a template virtual server for creation (1). A copy of the corresponding VM image is created in a cloud consumer-controlled cloud storage device (2). The cloud consumer initiates the virtual server using the usage and administration portal. (3), which interacts with the VIM to create the virtual server instance via the underlying hardware. (4). The cloud consumer is able to use and customize the virtual server via other features on the usage and administration portal . (5). (Note that the self-service portal and usage and administration portal are explained in chapter – 9. . 11
- 12. Cloud Infrastructure Mechanisms 7.3. Cloud Storage Device The cloud storage device mechanism represents storage devices that are designed specifically for cloud-based provisioning. Instances of these devices can be virtualized, similar to how physical servers can spawn virtual server images. Cloud storage devices are commonly able to provide fixed-increment capacity allocation in support of the pay-per-use mechanism. Cloud storage devices can be exposed for remote access via cloud storage services. A primary concern related to cloud storage is the security, integrity, and confidentiality of data, which becomes more prone to being compromised when entrusted to external cloud providers and other third parties. Cloud Storage Levels Cloud storage device mechanisms provide common logical units of data storage, such as: • Files – Collections of data are grouped into files that are located in folders. • Blocks – The lowest level of storage and the closest to the hardware, a block is the smallest unit of data that is still individually accessible. • Datasets – Sets of data are organized into a table-based, delimited, or record format. • Objects – Data and its associated metadata are organized as Web-based resources. 12
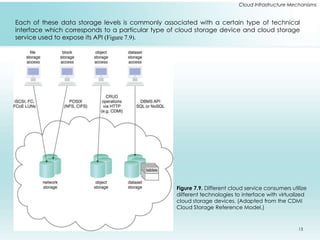
- 13. Cloud Infrastructure Mechanisms Each of these data storage levels is commonly associated with a certain type of technical interface which corresponds to a particular type of cloud storage device and cloud storage service used to expose its API (Figure 7.9). Figure 7.9. Different cloud service consumers utilize different technologies to interface with virtualized cloud storage devices. (Adapted from the CDMI Cloud Storage Reference Model.) 13
- 14. Cloud Infrastructure Mechanisms Network Storage Interfaces Legacy network storage most commonly falls under the category of network storage interfaces. It includes storage devices in compliance with industry standard protocols, such as SCSI for storage blocks and the server message block (SMB), common Internet file system (CIFS), and network file system (NFS) for file and network storage. File storage entails storing individual data in separate files that can be different sizes and formats and organized into folders and subfolders. Original files are often replaced by the new files that are created when data has been modified. Storage processing levels and thresholds for file allocation are usually determined by the file system itself. Block storage requires data to be in a fixed format (known as a data block), which is the smallest unit that can be stored and accessed and the storage format closest to hardware Object Storage Interfaces Various types of data can be referenced and stored as Web resources. This is referred to as object storage, which is based on technologies that can support a range of data and media types. The Storage Networking Industry Association’s Cloud Data Management Interface (SNIA’s CDMI) supports the use of object storage interfaces. 14
- 15. Cloud Infrastructure Mechanisms Database Storage Interfaces Cloud storage device mechanisms based on database storage interfaces typically support a query language in addition to basic storage operations. Storage management is carried out using a standard API or an administrative user-interface. This classification of storage interface is divided into two main categories according to storage structure, as follows : I. Relational Data Storage Relational databases (or relational storage devices) rely on tables to organize similar data into rows and columns. Tables can have relationships with each other to give the data increased structure, to protect data integrity, and to avoid data redundancy (which is referred to as data normalization). II. Non-Relational Data Storage Non-relational storage (also commonly referred to as NoSQL storage) moves away from the traditional relational database model in that it establishes a “looser” structure for stored data with less emphasis on defining relationships and realizing data normalization. 15
- 16. Cloud Infrastructure Mechanisms Figure 7.10. The cloud consumer interacts with the usage and administration portal to create a cloud storage device and define access control policies (1). The usage and administration portal interact with the cloud storage software to create the cloud storage device instance and apply the required access policy to its data objects (2). Each data object is assigned to a cloud storage device and all of the data objects are stored in the same virtual storage volume. The cloud consumer uses the proprietary cloud storage device UI to interact directly with the data objects (3). (Note that the usage and administration portal is explained in Chapter 9.) 16
- 17. Cloud Infrastructure Mechanisms Figure 7.11. The cloud consumer uses the usage and administration portal to create and assign a cloud storage device to an existing virtual server. (1). The usage and administration portal interacts with the VIM software. (2a), which creates and configures the appropriate LUN (2b). Each cloud storage device uses a separate LUN controlled by the virtualization platform. The cloud consumer remotely logs into the virtual server directly . (3a) to access the cloud storage device 3b). 17
- 18. Cloud Infrastructure Mechanisms 7.4. Cloud Usage Monitor The cloud usage monitor mechanism is a lightweight and autonomous software program responsible for collecting and processing IT resource usage data. Cloud usage monitors can exist in different formats. The upcoming sections describe three common agent-based implementation formats. Each can be designed to forward collect usage data to a log database for post-processing and reporting purposes. Monitoring Agent A monitoring agent is an intermediary, event-driven program that exists as a service agent and resides along existing communication paths to transparently monitor and analyze data flows (Figure 7.12). This type of cloud usage monitor is commonly used to measure network traffic and message metrics. 18
- 19. Cloud Infrastructure Mechanisms Figure 7.12. A cloud service consumer sends a request message to a cloud service (1). The monitoring agent intercepts the message to collect relevant usage data (2) before allowing it to continue to the cloud service (3a). The monitoring agent stores the collected usage data in a log database (3b). The cloud service replies with a response message (4) that is sent back to the cloud service consumer without being intercepted by the monitoring agent (5). 19
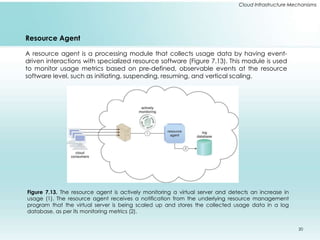
- 20. Cloud Infrastructure Mechanisms Resource Agent A resource agent is a processing module that collects usage data by having event-driven interactions with specialized resource software (Figure 7.13). This module is used to monitor usage metrics based on pre-defined, observable events at the resource software level, such as initiating, suspending, resuming, and vertical scaling. Figure 7.13. The resource agent is actively monitoring a virtual server and detects an increase in usage (1). The resource agent receives a notification from the underlying resource management program that the virtual server is being scaled up and stores the collected usage data in a log database, as per its monitoring metrics (2). 20
- 21. Cloud Infrastructure Mechanisms Polling Agent A polling agent is a processing module that collects cloud service usage data by polling IT resources. This type of cloud service monitor is commonly used to periodically monitor IT resource status, such as uptime and downtime (Figure 7.14). Figure 7.14. A polling agent monitors the status of a cloud service hosted by a virtual server by sending periodic polling request messages and receiving polling response messages that report usage status “A” after a number of polling cycles, until it receives a usage status of “B” (1), upon which the polling agent records the new usage status in the log database (2). 21
- 22. 7.5. Resource Replication Defined as the creation of multiple instances of the same IT resource, replication is typically performed when an IT resource’s availability and performance need to be enhanced. Virtualization technology is used to implement the resource replication mechanism to replicate cloud-based IT resources (Figure 7.16). Figure 7.16. The hypervisor replicates several instances of a virtual server, using a stored virtual server image. 22
- 23. Cloud Infrastructure Mechanisms Figure 7.17. A high-availability virtual server is running in Data Center A. VIM instances in Data Centers A and B are executing a coordination function that allows detection of failure conditions. Stored VM images are replicated between data centers as a result of the high-availability architecture 23
- 24. Cloud Infrastructure Mechanisms 7.6. Ready-Made Environment The ready-made environment mechanism (Figure 7.20) is a defining component of the PaaS cloud delivery model that represents a pre-defined, cloud-based platform comprised of a set of already installed IT resources, ready to be used and customized by a cloud consumer. These environments are utilized by cloud consumers to remotely develop and deploy their own services and applications within a cloud. Typical ready-made environments include pre-installed IT resources, such as databases, middleware, development tools, and governance tools. Figure 7.20. A cloud consumer accesses a ready-made environment hosted on a virtual server. A ready-made environment is generally equipped with a complete software development kit (SDK) that provides cloud consumers with programmatic access to the development technologies that comprise their preferred programming stacks. 24
- 25. Cloud Infrastructure Mechanisms Figure 7.21. The developer uses the provided SDK to develop the Part Number Catalog Web application (1). The application software is deployed on a Web platform that was established by two ready-made environments called the front-end instance (2a) and the back-end instance (2b). The application is made available for usage and one end-user accesses its front-end instance (3). The software running in the front-end instance invokes a long-running task at the back-end instance that corresponds to the processing required by the end-user (4). The application software deployed at both the front-end and back-end instances is backed by a cloud storage device that provides persistent storage of the application data (5). 25
- 26. Hope this is been informative and I would like to thank you for viewing.