Iia 2012 Spring Conference Philly V Final
- 1. Emerging Technology Challenges and Solutions for Internal Audit and Compliance Danny Miller, CISA, CGEIT, CRISC, ITIL, QSA Principal & National Solutions Leader Cybersecurity & Privacy © Grant Thornton. All rights reserved.
- 2. Topics • Current Technology Landscape • Emerging Technology – Cloud computing – Mobile computing – Cybersecurity trends • Key fundamentals of Cloud security • Potential IA Complexities • Solutions • What’s Next? © Grant Thornton. All rights reserved.
- 3. Current Technology Landscape • On-premise hardware, software, and management • Support may be on-shore, near-shore or off-shore © Grant Thornton. All rights reserved.
- 4. Current Technology Landscape (continued) • Localized processes and controls • Prompt remediation when required • Clear data ownership • Straightforward compliance approach © Grant Thornton. All rights reserved.
- 5. Current Technology Landscape (continued) • Challenges/benefits – It's expensive and requires a lot of overhead – Difficult to scale and react quickly – Significant embedded cost structure – Inflexible to meet business need – Easier to maintain audit trail © Grant Thornton. All rights reserved.
- 6. Emerging Technology Trends Spending on public IT cloud services will grow at more than five times the rate of the IT industry in 2011-2012 Enterprise IT planners begin to include cloud-computing expertise in some of their job searches to be prepared for the projects of the short-term and mid-term future Hosted private clouds will outnumber internal clouds 3:1… But service providers have been incrementally ready. Cloud management and monitoring will fuel enterprise cloud adoption 32% of CIOs expected virtualization to be their top investment in 2011 - it is accelerating faster in 2012 © Grant Thornton. All rights reserved.
- 7. Emerging Technology • Cloud computing – Saas, PaaS, IaaS, DaaS • Mobile computing – Mobile platforms that are blurring the line between a hand-held and complex computing • Data analytics – Master Data Management • Cybersecurity – Trends © Grant Thornton. All rights reserved.
- 8. Emerging Technology Platforms (continued) Types of Clouds Models of Cloud: • Public • Software as a Service (SaaS) - Shared computer resources - Software applications delivered provided by an off-site third-party over the Internet provider • Platform as a Service (PaaS) • Private - Full or partial operating - Dedicated computer resources system/development environment provided by an off-site third-party delivered over the Internet or use of Cloud technologies on a • Infrastructure as a Service private internal network (IaaS) • Hybrid - Computer infrastructure delivered - Consisting of multiple public and over the Internet private Clouds • Platform as a Service (PaaS) - Virtualization of desktop systems serving thin clients, delivered over the Internet or a private Cloud © Grant Thornton. All rights reserved.
- 9. Emerging Technology Platforms (continued) Public Cloud Private Cloud © Grant Thornton. All rights reserved.
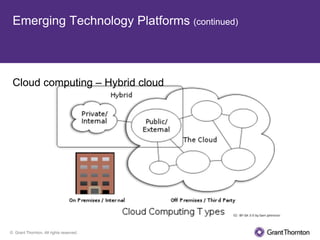
- 10. Emerging Technology Platforms (continued) Cloud computing – Hybrid cloud © Grant Thornton. All rights reserved.
- 11. Emerging Technology Platforms (continued) • Mobile computing is: – Wireless – Utilizes tablet platforms and smartphones – Internet-based – Communication via 4G and WiFi – Scaled applications © Grant Thornton. All rights reserved.
- 12. Potential New IA Complexity • Cloud computing – Availability & performance – Business continuity – Data protection – Data encryption – Privacy (especially in Healthcare & Life Sciences) © Grant Thornton. All rights reserved.
- 13. Potential New IA Complexity (continued) Cloud computing (continued) – Compliance • FISMA • HIPAA • SOX • PCI DSS (card payments) • EU Data Protection Directive, et al. © Grant Thornton. All rights reserved.
- 14. Key Fundamentals of Cloud Security • Focus on foundational controls that protects information and ensures availability. Is the security on your cloud service at least as high as applications used internally? • Match work processes to security needs (if the process is regulatory in nature, or has high security need, then ensure security threshold meets that). • When building or selecting a cloud service, ensure integration and usability are considered in the enterprise. Because of the integrated nature of services these days, need to consider • Adopt a risk mitigation plan when adopting cloud technology. This would include responses to risk events. • Consider how storage with your organization's information is handled, including backup, recovery and "immediate availability". There have been instances of incorrect image recoveries. Make the decision on "co-mingled" data with other clients of vendors. • Ensure evaluations of security are performed and that they are robust. Never take a vendor's word that they are audited and are secure on their own. © Grant Thornton. All rights reserved.
- 15. Key Fundamentals of Cloud Security (cont'd) • Whether you are deploying or you are subscribing to a vendor, you should ensure that intrusion prevention, monitoring, access and identity management are adequate for the service. • Consider strategic elements, such as the domicile of the data, Legal and e- Discovery rules for your state • What are your responsibilities in the event of a breach of your information? • Ensure that there is a strong continuity program in place and that if you are a subscriber to a service, that you include that in the BCP. Test at least annually. • On at least an annual basis, revisit the security model on all cloud services. © Grant Thornton. All rights reserved.
- 16. Key Fundamentals of Cloud Security (cont'd) Attribution: Cloud Security Alliance (CSA) © Grant Thornton. All rights reserved.
- 17. Key Fundamentals of Cloud Security (cont'd) Attribution: Cloud Security Alliance (CSA) © Grant Thornton. All rights reserved.
- 18. Potential New IA Complexity Mobile computing – Security (physical and virtual) – Data ownership – Service interruption and recovery – Data archiving – Availability © Grant Thornton. All rights reserved.
- 19. Potential New IA Complexity (continued) Mobile computing – WiFi/4G security – Surveillance and access control – Availability – Data ownership and recovery – Auditability – Bluetooth “hijacking” – AIDC © Grant Thornton. All rights reserved.
- 20. Solutions Cloud computing – Demand good security in the contract with provider – Have a "return of data" plan at end of contract – Know where the data is and who has access – Deploy a layered security architecture – Assess and inventory risks – Conduct annual security policy audits – Deploy and authenticate user credentials – Encrypt all stored data (P2P encryption) – Actively manage passwords and segregation of duties – Implement layered firewalls © Grant Thornton. All rights reserved.
- 21. Solutions (continued) Mobile computing – Encrypt all WiFi access – Clarify data ownership – Classify information going across – Implement service interruption plan – Disable Bluetooth communications – Deploy device-specific security software – Encrypt all communications – If it's lost or stolen, ensure that you can do a remote "wipe" of information © Grant Thornton. All rights reserved.
- 22. What’s Next? • Distributed computing (the Cloud) • Cybersecurity & Privacy focus • Virtualization • Advanced IA tools – Analytics – Provenance engines – Enhanced hardware firewalls – Advanced encryption technology – New data segregation and security standards – Secure digital communications • Standards such as ITIL, COBIT and PCI are integrating and are now complimentary towards each other © Grant Thornton. All rights reserved.
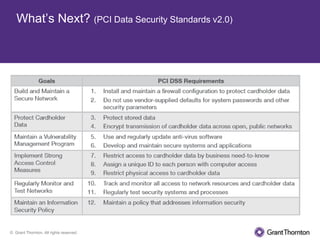
- 23. What’s Next? (PCI Data Security Standards v2.0) © Grant Thornton. All rights reserved.
- 24. What’s Next? (PCI Data Security Standards v2.0) © Grant Thornton. All rights reserved.
- 25. What’s Next? (PCI Data Security Standards v2.0) © Grant Thornton. All rights reserved.
- 26. What’s Next? (Enterprise Master Data Management) • Companies are awash in data, but which data is the right data to use? Data grows by 50%+ each year. • Company leadership needs "one version of the truth" on dashboards, reports and in analytical datasets. • Internal Audit and Compliance departments should be concerned about controls, availability, integrity and quality of data. • Conceptually: – Data and information are valuable corporate assets and should be treated as such – Data must be managed carefully and should have quality, integrity, security and availability addressed. © Grant Thornton. All rights reserved.
- 27. What’s Next? (Enterprise Master Data Management) MDM is the management of an institution’s fundamental data that is shared across multiple business units, everything from project budgets to donor contacts to employee contact information. You can think of master data as all of the enterprise data (people, places, things and activities) that the institution needs to conduct its business. The goal of MDM, consequently, is to ensure the accuracy, consistency and availability of this data to the various business users. We believe that all organizations would benefit greatly from creating a strategy for MDM and implementing an MDM program in light of its current state and an organization's future data and information needs. © Grant Thornton. All rights reserved.
- 28. What’s Next? (Enterprise Master Data Management) Data and Information Management Data Governance Data Architecture Management Data Development Data Operations Management Data Security Management Data Quality Management Reference and Master Data Data Warehouse /Business Management Intelligence Management Document and Content Management Metadata Management Table 1: Scope of Data Management © Grant Thornton. All rights reserved.
- 29. What’s Next? (Data Governance Activities) • Establish institutional data standards • Identify and resolve data disputes • Implement necessary changes to data standards and policies • Communicate actions to the organization as appropriate • Ensure accountability of institutional data policies and standards • Escalate issues to Governance Team as necessary © Grant Thornton. All rights reserved.
- 30. Questions? © Grant Thornton. All rights reserved.
- 31. Emerging Technology Challenges for Internal Audit and Compliance Danny Miller, CISA, CGEIT, CRISC, ITIL, QSA National Solutions Lead – Cybersecurity Regional Solutions Lead – Business Consulting Principal, Grant Thornton LLP [email protected] http://grantthornton.com/ © Grant Thornton. All rights reserved.