Introduction To Vulnerability Assessment & Penetration Testing
Download as PPTX, PDF2 likes1,694 views
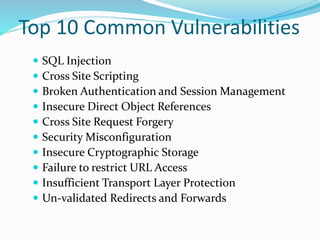
A vulnerability assessment identifies vulnerabilities in systems and networks to understand threats and risks. Penetration testing simulates cyber attacks to detect exploitable vulnerabilities. There are three types of penetration testing: black box with no system info; white box with full system info; and grey box with some system info. Common vulnerabilities include SQL injection, XSS, weak authentication, insecure storage, and unvalidated redirects. Tools like Nexpose, QualysGuard, and OpenVAS can automate vulnerability assessments.
1 of 13
Downloaded 79 times












Ad
Recommended
Vulnerability assessment and penetration testing



Vulnerability assessment and penetration testingAbu Sadat Mohammed Yasin This document discusses vulnerability assessment and penetration testing. It defines them as two types of vulnerability testing that search for known vulnerabilities and attempt to exploit vulnerabilities, respectively. Vulnerability assessment uses automated tools to detect known issues, while penetration testing employs hacking techniques to demonstrate how deeply vulnerabilities could be exploited like an actual attacker. Both are important security practices for identifying weaknesses and reducing risks, but require different skills and have different strengths, weaknesses, frequencies, and report outputs. Reasons for vulnerabilities include insecure coding, limited testing, and misconfigurations. The document outlines common vulnerability and attack types as well as how vulnerability assessment and penetration testing are typically conducted.
VAPT PRESENTATION full.pptx



VAPT PRESENTATION full.pptxDARSHANBHAVSAR14 The document provides information on vulnerability assessment and penetration testing. It defines vulnerability assessment as a systematic approach to finding security issues in a network or system through manual and automated scanning. Penetration testing involves exploring and exploiting any vulnerabilities that are found to confirm their existence and potential damage. The document outlines the types of testing as blackbox, graybox, and whitebox. It also lists some common tools used for testing like Nmap, ZAP, Nikto, WPScan, and HostedScan. Finally, it provides examples of specific vulnerabilities found and their solutions, such as outdated themes/plugins, backup files being accessible, and SQL injection issues.
Vulnerability assessment & Penetration testing Basics 



Vulnerability assessment & Penetration testing Basics Mohammed Adam In these days of widespread Internet usage, security is of prime importance. The almost universal use of mobile and Web applications makes systems vulnerable to cyber attacks. Vulnerability assessment can help identify the loopholes in a system while penetration testing is a proof-of-concept approach to actually explore and exploit a vulnerability.
Blockchain by Aman Thakur.pptx



Blockchain by Aman Thakur.pptxThe NorthCap University A simple interactive ppt on the basics of Blockchain.
What is Blockchain? Why we need it? How it works? Advantages & Disadvantages and many more topics like this.
Pen Testing Explained



Pen Testing ExplainedRand W. Hirt This document provides an overview of penetration testing, including its definition, purpose, types, methodology, tools, challenges, and takeaways. Penetration testing involves modeling real-world attacks to find vulnerabilities in a system and then attempting to exploit those vulnerabilities to determine security risks. It is important for identifying flaws that need remediation and assessing an organization's security posture and risk profile. The methodology generally involves planning, reconnaissance, scanning, exploitation, and reporting phases. Challenges include performing comprehensive testing within time and budget constraints and addressing business impact.
Cyber forensics ppt



Cyber forensics pptRoshiniVijayakumar1 This as the description for Cyber Forensics from which you can come to know more about Cyber/Computer Forensics.
Presentation sap



Presentation sapAayushi Bhandari SAP provides business software and related applications to help companies execute business strategies. Founded in 1972 in Germany, SAP now has over 51,000 employees worldwide serving over 82,000 customers across industries and countries. SAP's main products include ERP, CRM, SCM, and HANA, which allow companies to integrate and optimize business processes.
IOT PROTOCOLS.pptx



IOT PROTOCOLS.pptxDRREC This document discusses IoT protocols for data communication and connection models. It describes the key pillars of IoT protocols as being device, connectivity, data, and analytics. It also outlines various types of IoT data protocols like AMQP, DDS, XMPP, and WebSocket that establish end-to-end communication. Additionally, it covers IoT network protocols like Bluetooth, LPWANs, ZigBee, Z-Wave and others that facilitate secured communication between IoT devices over the internet.
Vulnerability and Assessment Penetration Testing



Vulnerability and Assessment Penetration TestingYvonne Marambanyika VAPT defines a wide range of security testing services to ascertain and address cyber security exposures. It includes vulnerability testing through perimeter scans for missing patches or custom exploits to bypass perimeters, as well as penetration testing by simulating real-world attacks to provide a point-in-time assessment of vulnerabilities and threats to a network infrastructure. Customers can inquire more about these security testing and analysis services by contacting the company.
Penetration Testing Tutorial | Penetration Testing Tools | Cyber Security Tra...



Penetration Testing Tutorial | Penetration Testing Tools | Cyber Security Tra...Edureka! ( ** Cyber Security Training: https://www.edureka.co/cybersecurity-certification-training ** )
This Edureka PPT on "Penetration Testing" will help you understand all about penetration testing, its methodologies, and tools. Below is the list of topics covered in this session:
What is Penetration Testing?
Phases of Penetration Testing
Penetration Testing Types
Penetration Testing Tools
How to perform Penetration Testing on Kali Linux?
Cyber Security Playlist: https://bit.ly/2N2jlNN
Cyber Security Blog Series: https://bit.ly/2AuULkP
Instagram: https://www.instagram.com/edureka_lea...
Facebook: https://www.facebook.com/edurekaIN/
Twitter: https://twitter.com/edurekain
LinkedIn: https://www.linkedin.com/company/edureka
Penetration testing & Ethical Hacking



Penetration testing & Ethical HackingS.E. CTS CERT-GOV-MD This document discusses penetration testing and ethical hacking. It provides an overview of penetration testing methodology and the services offered by Endava, including regular vulnerability scans, penetration tests, PCI assessments, security trainings, audits, and intrusion monitoring solutions. The presenter, Maxim Catanoi, is an IT security consultant at Endava with over 9 years of experience and multiple security certifications.
Ethical Hacking n VAPT presentation by Suvrat jain



Ethical Hacking n VAPT presentation by Suvrat jainSuvrat Jain a perfect example of your 6 weeks summer training ppt. Course-Ethical Hacking , its info and VAPT- Vulnerability Assessment n Penetration testing. about how vulnerability scanning , tools used , cracking password , etc.
Introduction to Web Application Penetration Testing



Introduction to Web Application Penetration TestingNetsparker These slides give an introduction to all the different things and stages that make a complete web application penetration test. It starts from the very basics, including how to define a Scope of Engagement.
These slides are part of the course Introduction to Web Application Security and Penetration Testing with Netsparker, which can be found here: https://www.netsparker.com/blog/web-security/introduction-web-application-penetration-testing/
Penetration Testing 



Penetration Testing RomSoft SRL Penetration testing is used to test the security of a website by simulating real attacks from outside. It identifies potential vulnerabilities to prevent harmful attacks. By understanding how attacks work, the IT team can fix issues and prevent larger attacks in the future. The presentation will demonstrate a penetration testing tool that checks the login page for security issues like authentication, redirects, and hidden code. Contact information is provided for any additional questions.
Threat Modelling



Threat Modellingn|u - The Open Security Community This document discusses threat modeling for software applications. It covers the key stages of threat modeling including decomposing the application, determining and ranking threats using STRIDE, and determining countermeasures. Specific topics covered include threat modeling approaches, data flow diagrams, trust levels, the STRIDE framework for analyzing spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege threats. It also discusses mobile threat modeling and provides an example threat analysis of a student results portal application.
Penetration testing reporting and methodology



Penetration testing reporting and methodologyRashad Aliyev This paper covering information about Penetration testing methodology, standards reporting formats and comparing reports. Explained problem of Cyber Security experts when they making penetration tests. How they doing current presentations.
We will focus our work in penetration testing methodology reporting form and detailed information how to compare result and related work information.
Security testing



Security testingKhizra Sammad Security Testing is a process to determine that an information system protects data and maintains functionality as intended.
Web App Security Presentation by Ryan Holland - 05-31-2017



Web App Security Presentation by Ryan Holland - 05-31-2017TriNimbus Web App Security - A presentation by Ryan Holland, Sr. Director, Cloud Architecture at Alert Logic for the Vancouver AWS User Group Meetup on May 31, 2017.
Cybersecurity 1. intro to cybersecurity



Cybersecurity 1. intro to cybersecuritysommerville-videos Cybersecurity involves protecting individuals, businesses, and critical infrastructure from threats arising from computer and internet use. It addresses both external attacks by remote agents exploiting vulnerabilities, as well as insider threats from valid users. Cybersecurity deals with a range of technical and human factors, as vulnerabilities usually stem from a mix of these. Key concerns include malware, cyber attacks aiming to cause damage or steal data, and accidental incidents that can also lead to losses.
Vulnerability Management



Vulnerability Managementasherad Presentation I gave to a client on showing the importance of implementing a vulnerability management program life cycle.
Info Security - Vulnerability Assessment



Info Security - Vulnerability AssessmentMarcelo Silva Simple deck about Vulnerability Assessment and Penetration Test.
Please download it if you want to see the presentation notes as well. :-)
Different types of attacks in internet



Different types of attacks in internetRohan Bharadwaj Different types of attacks
Information security
cross site scripting
Denial of service attack
phishing
spoofing
Owasp top 10 vulnerabilities



Owasp top 10 vulnerabilitiesOWASP Delhi Session on OWASP Top 10 Vulnerabilities presented by Aarti Bala and Saman Fatima. The session covered the below 4 vulnerabilities -
Injection,
Sensitive Data Exposure
Cross Site Scripting
Insufficient Logging and Monitoring
Vulnerabilities in modern web applications



Vulnerabilities in modern web applicationsNiyas Nazar Microsoft powerpoint presentation for BTech academic seminar.This seminar discuses about penetration testing, penetration testing tools, web application vulnerabilities, impact of vulnerabilities and security recommendations.
MITRE ATT&CK framework



MITRE ATT&CK frameworkBhushan Gurav MITRE ATT&CK framework is about the framework that is followed by Threat Hunters, Threat Analysts for Threat Modelling purpose, which can be use for Adversary Emulation and Attack Defense. Cybersecurity Analyst widely use it for framing the attack through its various used Tactics and Techniques.
VAPT - Vulnerability Assessment & Penetration Testing 



VAPT - Vulnerability Assessment & Penetration Testing Netpluz Asia Pte Ltd VAPT (Vulnerability Assessment and Penetration Testing) involves evaluating systems and networks to identify vulnerabilities, configuration issues, and potential routes of unauthorized access. It is recommended for SMEs due to common security issues like phishing and ransomware attacks targeting them. The document outlines the types of VAPT testing, why SMEs need it, example data breaches, and estimated costs of common cyber attacks and security services.
Security testing fundamentals



Security testing fundamentalsCygnet Infotech Security Testing is deemed successful when the below attributes of an application are intact
- Authentication
- Authorization
- Availability
- Confidentiality
- Integrity
- Non-Repudiation
Testing must start early to minimize defects and cost of quality. Security testing must start right from the Requirements Gathering phase to make sure that the quality of end-product is high.
This is to ensure that any intentional/unintentional unforeseen action does not halt or delay the system.
Web Application Penetration Testing 



Web Application Penetration Testing Priyanka Aash Introduction of Ethical Hacking, Life cycle of Hacking, Introduction of Penetration testing, Steps in Penetration Testing, Foot printing Module, Scanning Module, Live Demos on Finding Vulnerabilities a) Bypass Authentication b) Sql Injection c) Cross site Scripting d) File upload Vulnerability (Web Server Hacking) Countermeasures of Securing Web applications
The Fundamentals of Penetration Testing.pptx (1).pdf



The Fundamentals of Penetration Testing.pptx (1).pdfapurvar399 Penetration testing, often referred to as ethical hacking, is a simulated cyber attack against your computer system to check for exploitable vulnerabilities.
Introduction to penetration testing



Introduction to penetration testingNezar Alazzabi this is a simple presentation that will give you a general overview and introduction to penetration testing.
Ad
More Related Content
What's hot (20)
Vulnerability and Assessment Penetration Testing



Vulnerability and Assessment Penetration TestingYvonne Marambanyika VAPT defines a wide range of security testing services to ascertain and address cyber security exposures. It includes vulnerability testing through perimeter scans for missing patches or custom exploits to bypass perimeters, as well as penetration testing by simulating real-world attacks to provide a point-in-time assessment of vulnerabilities and threats to a network infrastructure. Customers can inquire more about these security testing and analysis services by contacting the company.
Penetration Testing Tutorial | Penetration Testing Tools | Cyber Security Tra...



Penetration Testing Tutorial | Penetration Testing Tools | Cyber Security Tra...Edureka! ( ** Cyber Security Training: https://www.edureka.co/cybersecurity-certification-training ** )
This Edureka PPT on "Penetration Testing" will help you understand all about penetration testing, its methodologies, and tools. Below is the list of topics covered in this session:
What is Penetration Testing?
Phases of Penetration Testing
Penetration Testing Types
Penetration Testing Tools
How to perform Penetration Testing on Kali Linux?
Cyber Security Playlist: https://bit.ly/2N2jlNN
Cyber Security Blog Series: https://bit.ly/2AuULkP
Instagram: https://www.instagram.com/edureka_lea...
Facebook: https://www.facebook.com/edurekaIN/
Twitter: https://twitter.com/edurekain
LinkedIn: https://www.linkedin.com/company/edureka
Penetration testing & Ethical Hacking



Penetration testing & Ethical HackingS.E. CTS CERT-GOV-MD This document discusses penetration testing and ethical hacking. It provides an overview of penetration testing methodology and the services offered by Endava, including regular vulnerability scans, penetration tests, PCI assessments, security trainings, audits, and intrusion monitoring solutions. The presenter, Maxim Catanoi, is an IT security consultant at Endava with over 9 years of experience and multiple security certifications.
Ethical Hacking n VAPT presentation by Suvrat jain



Ethical Hacking n VAPT presentation by Suvrat jainSuvrat Jain a perfect example of your 6 weeks summer training ppt. Course-Ethical Hacking , its info and VAPT- Vulnerability Assessment n Penetration testing. about how vulnerability scanning , tools used , cracking password , etc.
Introduction to Web Application Penetration Testing



Introduction to Web Application Penetration TestingNetsparker These slides give an introduction to all the different things and stages that make a complete web application penetration test. It starts from the very basics, including how to define a Scope of Engagement.
These slides are part of the course Introduction to Web Application Security and Penetration Testing with Netsparker, which can be found here: https://www.netsparker.com/blog/web-security/introduction-web-application-penetration-testing/
Penetration Testing 



Penetration Testing RomSoft SRL Penetration testing is used to test the security of a website by simulating real attacks from outside. It identifies potential vulnerabilities to prevent harmful attacks. By understanding how attacks work, the IT team can fix issues and prevent larger attacks in the future. The presentation will demonstrate a penetration testing tool that checks the login page for security issues like authentication, redirects, and hidden code. Contact information is provided for any additional questions.
Threat Modelling



Threat Modellingn|u - The Open Security Community This document discusses threat modeling for software applications. It covers the key stages of threat modeling including decomposing the application, determining and ranking threats using STRIDE, and determining countermeasures. Specific topics covered include threat modeling approaches, data flow diagrams, trust levels, the STRIDE framework for analyzing spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege threats. It also discusses mobile threat modeling and provides an example threat analysis of a student results portal application.
Penetration testing reporting and methodology



Penetration testing reporting and methodologyRashad Aliyev This paper covering information about Penetration testing methodology, standards reporting formats and comparing reports. Explained problem of Cyber Security experts when they making penetration tests. How they doing current presentations.
We will focus our work in penetration testing methodology reporting form and detailed information how to compare result and related work information.
Security testing



Security testingKhizra Sammad Security Testing is a process to determine that an information system protects data and maintains functionality as intended.
Web App Security Presentation by Ryan Holland - 05-31-2017



Web App Security Presentation by Ryan Holland - 05-31-2017TriNimbus Web App Security - A presentation by Ryan Holland, Sr. Director, Cloud Architecture at Alert Logic for the Vancouver AWS User Group Meetup on May 31, 2017.
Cybersecurity 1. intro to cybersecurity



Cybersecurity 1. intro to cybersecuritysommerville-videos Cybersecurity involves protecting individuals, businesses, and critical infrastructure from threats arising from computer and internet use. It addresses both external attacks by remote agents exploiting vulnerabilities, as well as insider threats from valid users. Cybersecurity deals with a range of technical and human factors, as vulnerabilities usually stem from a mix of these. Key concerns include malware, cyber attacks aiming to cause damage or steal data, and accidental incidents that can also lead to losses.
Vulnerability Management



Vulnerability Managementasherad Presentation I gave to a client on showing the importance of implementing a vulnerability management program life cycle.
Info Security - Vulnerability Assessment



Info Security - Vulnerability AssessmentMarcelo Silva Simple deck about Vulnerability Assessment and Penetration Test.
Please download it if you want to see the presentation notes as well. :-)
Different types of attacks in internet



Different types of attacks in internetRohan Bharadwaj Different types of attacks
Information security
cross site scripting
Denial of service attack
phishing
spoofing
Owasp top 10 vulnerabilities



Owasp top 10 vulnerabilitiesOWASP Delhi Session on OWASP Top 10 Vulnerabilities presented by Aarti Bala and Saman Fatima. The session covered the below 4 vulnerabilities -
Injection,
Sensitive Data Exposure
Cross Site Scripting
Insufficient Logging and Monitoring
Vulnerabilities in modern web applications



Vulnerabilities in modern web applicationsNiyas Nazar Microsoft powerpoint presentation for BTech academic seminar.This seminar discuses about penetration testing, penetration testing tools, web application vulnerabilities, impact of vulnerabilities and security recommendations.
MITRE ATT&CK framework



MITRE ATT&CK frameworkBhushan Gurav MITRE ATT&CK framework is about the framework that is followed by Threat Hunters, Threat Analysts for Threat Modelling purpose, which can be use for Adversary Emulation and Attack Defense. Cybersecurity Analyst widely use it for framing the attack through its various used Tactics and Techniques.
VAPT - Vulnerability Assessment & Penetration Testing 



VAPT - Vulnerability Assessment & Penetration Testing Netpluz Asia Pte Ltd VAPT (Vulnerability Assessment and Penetration Testing) involves evaluating systems and networks to identify vulnerabilities, configuration issues, and potential routes of unauthorized access. It is recommended for SMEs due to common security issues like phishing and ransomware attacks targeting them. The document outlines the types of VAPT testing, why SMEs need it, example data breaches, and estimated costs of common cyber attacks and security services.
Security testing fundamentals



Security testing fundamentalsCygnet Infotech Security Testing is deemed successful when the below attributes of an application are intact
- Authentication
- Authorization
- Availability
- Confidentiality
- Integrity
- Non-Repudiation
Testing must start early to minimize defects and cost of quality. Security testing must start right from the Requirements Gathering phase to make sure that the quality of end-product is high.
This is to ensure that any intentional/unintentional unforeseen action does not halt or delay the system.
Web Application Penetration Testing 



Web Application Penetration Testing Priyanka Aash Introduction of Ethical Hacking, Life cycle of Hacking, Introduction of Penetration testing, Steps in Penetration Testing, Foot printing Module, Scanning Module, Live Demos on Finding Vulnerabilities a) Bypass Authentication b) Sql Injection c) Cross site Scripting d) File upload Vulnerability (Web Server Hacking) Countermeasures of Securing Web applications
Similar to Introduction To Vulnerability Assessment & Penetration Testing (20)
The Fundamentals of Penetration Testing.pptx (1).pdf



The Fundamentals of Penetration Testing.pptx (1).pdfapurvar399 Penetration testing, often referred to as ethical hacking, is a simulated cyber attack against your computer system to check for exploitable vulnerabilities.
Introduction to penetration testing



Introduction to penetration testingNezar Alazzabi this is a simple presentation that will give you a general overview and introduction to penetration testing.
M.Tech. IDS Lecture-Mid Term.pptx



M.Tech. IDS Lecture-Mid Term.pptxpawandeoli1 This document provides an outline for a course on intrusion detection systems. It begins with basic definitions of intrusions, intruders, and intrusion detection systems. It then outlines the major topics to be covered in the course, including intrusion detection approaches, theoretical foundations, implementation and deployment of IDS and IPS, and security management case studies. Questions are also provided on topics like security testing, vulnerabilities, and penetration testing. Common hacking tools like Metasploit and Wireshark are also mentioned.
M.Tech. IDS Lecture by graphic era university



M.Tech. IDS Lecture by graphic era universitypheonix4 This document provides an outline for a course on intrusion detection systems. It begins with basic definitions of intrusions, intruders, and intrusion detection systems. It then covers theoretical foundations and approaches to intrusion detection as well as the internals and deployment of IDS and IPS systems. Case studies and questions on topics like SQL injection, penetration testing, and ethical hacking are also included.
Black Box Pentest Uncovering Vulnerabilities in Internal Pen Tests.docx



Black Box Pentest Uncovering Vulnerabilities in Internal Pen Tests.docxyogitathakurrr3 Organizations often face unique challenges that require tailored security assessments. By understanding the differences—what each type of pentest entails and the specific scenarios in which they are most effective—companies can enhance their security posture. Implementing both methods provides a comprehensive view of their defenses, allowing for a more robust cybersecurity strategy.
Infrastructure & Network Vulnerability Assessment and Penetration Testing



Infrastructure & Network Vulnerability Assessment and Penetration TestingElanusTechnologies A network vulnerability assessment identifies security flaws in a network without exploiting them, providing a cost-effective overview of vulnerabilities. Network penetration testing then actively tests for vulnerabilities by simulating hacking attacks. The procedures for penetration testing include reconnaissance of the network for open ports or software flaws, discovery of vulnerabilities through scanning and testing, and exploitation of identified vulnerabilities to determine if unauthorized access is possible. Infrastructure penetration testing specifically targets a company's internal systems and externally exposed systems and networks.
Introduction To Ethical Hacking



Introduction To Ethical HackingRaghav Bisht Hacking involves exploiting vulnerabilities in computer systems or networks to gain unauthorized access. There are different types of hackers, including white hat hackers who perform ethical hacking to test security, black hat hackers who perform hacking with malicious intent, and grey hat hackers who may sometimes hack ethically and sometimes not. Ethical hacking involves testing one's own systems for vulnerabilities without causing harm. Vulnerability assessments and penetration tests are common ethical hacking techniques that involve scanning for vulnerabilities and attempting to exploit them in a controlled way. Popular tools used for ethical hacking include Kali Linux, Nmap, Metasploit, and John the Ripper.
Cyber warfare introduction



Cyber warfare introductionjagadeesh katla This document discusses various aspects of cyber warfare and security. It introduces cyber deterrence and its challenges. It then describes components of a reference model for cyber security including surveillance, penetration testing, honey nets, forensics, attribution, monitoring, reconnaissance, scanning, vulnerability analysis and exploitation. For each component, it provides details on the concept and relevant tools. The document aims to provide an overview of the cyber warfare landscape and approaches.
Vulnerability Assessment and Penetration Testing Framework by Falgun Rathod



Vulnerability Assessment and Penetration Testing Framework by Falgun RathodFalgun Rathod Vulnerability Assessment, Penetration testing or Ethical Hacking?
- What's the difference?
Penetration - Testing vs. Vulnerability Assessment
Penetration Testing Framework
External Penetration Testing What You Need to Know.pdf



External Penetration Testing What You Need to Know.pdfTeceze Ltd External penetration testing involves a simulated attack by ethical hackers or security professionals who attempt to exploit vulnerabilities in the organization's internet-facing assets, such as web applications, servers, firewalls, and network devices. The goal is to uncover weaknesses that could be exploited by hackers to gain unauthorized access, steal sensitive information, or disrupt business operations.
(VAPT) Vulnerability Assessment And Penetration Testing



(VAPT) Vulnerability Assessment And Penetration TestingBluechip Gulf IT Services Vulnerability Assessment & Penetration Testing (VAPT) identifies system weaknesses through assessments and simulates real-world attacks to bolster cybersecurity measures.
Network Penetration Testing Service



Network Penetration Testing ServiceSense Learner Technologies Pvt Ltd Network Penetration Testing Services in India | Senselearner
Senselearner offers top-notch Network penetration testing, also known as ethical hacking, it is the process of identifying and exploiting vulnerabilities in a computer network to assess its security posture. The aim of this type of testing is to simulate a real-world attack on a network to identify weaknesses that could be exploited by malicious hackers. The process typically involves several stages, including reconnaissance, vulnerability scanning, exploitation, and reporting. During the reconnaissance phase, Senselearner helps the tester gather information about the target network, including IP addresses, open ports, and other system information. This information is then used to identify potential vulnerabilities in the network. For more information visit our website: https://senselearner.com/network-vapt/
Penetration testing 



Penetration testing PTC This document provides an overview of penetration testing, including:
- Defining penetration testing as discovering and documenting security flaws in a system.
- The steps involved: footprinting, scanning, enumeration, gaining access, escalating privileges, covering tracks, and creating backdoors.
- Common tools used like Nessus, an integrated security scanning tool.
- The goal is to simulate an attack to evaluate security by finding vulnerabilities from misconfigurations, flaws, or process weaknesses.
NetWitness



NetWitnessTechBiz Forense Digital As soluções da NetWitness capturam todos os dados que circulam na rede e os contextualizam, filtrando o que pode ser crítico ou não. O usuario pode ver quem está indo aonde e vendo o quê.
Top 20 certified ethical hacker interview questions and answer



Top 20 certified ethical hacker interview questions and answerShivamSharma909 The technique of discovering vulnerabilities in a software, website, or agency’s structure that a hacker might exploit is known as ethical hacking. They employ this method to avoid cyberattacks and security breaches by legitimately hacking into systems and looking for flaws. CEH was designed to include a hands-on environment and a logical procedure across each ethical hacking area and technique. This is to provide you the opportunity to work towards proving the knowledge and skills to earn the CEH certificate and perform the tasks of an ethical hacker.
Read more: https://www.infosectrain.com/blog/top-20-certified-ethical-hacker-interview-questions-and-answer/
Types of Penetration Testing - presentation.pdf



Types of Penetration Testing - presentation.pdfapurvar399 Penetration testing can be categorized into several types, including black-box, white-box, and gray-box testing. Each type varies in terms of the tester's knowledge of the system, allowing for different approaches to identify vulnerabilities and security weaknesses.
Overview of Vulnerability Scanning.pptx



Overview of Vulnerability Scanning.pptxAjayKumar73315 The document discusses vulnerability scanning and OpenVAS. Vulnerability scanning involves using a scanner to identify security weaknesses. OpenVAS is an open source vulnerability scanning framework that consists of several services and tools for vulnerability scanning and management. At the center is the OpenVAS scanner which executes Network Vulnerability Tests (NVTs) from an NVT database that is regularly updated. The OpenVAS Manager receives tasks from the administrator and keeps a history of past scans.
Running Head Security Assessment Repot (SAR) .docx



Running Head Security Assessment Repot (SAR) .docxSUBHI7 Running Head: Security Assessment Repot (SAR) 1
Security Assessment Report (SAR) 27
Intentionally left blank
Security Assessment Report (SAR)
CHOICE OF ORGANIZATION IS UNIVERSITY OF MARYLAND MEDICAL CENTER (UMMC) OR A FICTITIUOS ORGANIZATION (BE CREATIVE)
Introduction
· Research into OPM security breach.
· What prompts this assessment exercise in our choice of organization? “but we have a bit of an emergency. There's been a security breach at the Office of Personnel Management. need to make sure it doesn't happen again.
· What were the hackers able to do? OPM OIG report and found that the hackers were able to gain access through compromised credentials
· How could it have been averted? A) security breach could have been prevented, if the Office of Personnel Management, or OPM, had abided by previous auditing reports and security findings.b) access to the databases could have been prevented by implementing various encryption schemas and c) could have been identified after running regularly scheduled scans of the systems.
Organization
· Describe the background of your organization, including the purpose, organizational structure,
· Diagram of the network system that includes LAN, WAN, and systems (use the OPM systems model of LAN side networks), the intra-network, and WAN side networks, the inter-net.
· Identify the boundaries that separate the inner networks from the outside networks.
· include a description of how these platforms are implemented in your organization: common computing platforms, cloud computing, distributed computing, centralized computing, secure programming fundamentals (cite references)
Threats Identification
Start Reading: Impact of Threats
The main threats to information system (IS) security are physical events such as natural disasters, employees and consultants, suppliers and vendors, e-mail attachments and viruses, and intruders.
Physical events such as fires, earthquakes, and hurricanes can cause damage to IT systems. The cost of this damage is not restricted to the costs of repairs or new hardware and software. Even a seemingly simple incident such as a short circuit can have a ripple effect and cost thousands of dollars in lost earnings.
Employees and consultants; In terms of severity of impact, employees and consultants working within the organization can cause the worst damage. Insiders have the most detailed knowledge of how the information systems are being used. They know what data is valuable and how to get it without creating tracks.
Suppliers and vendors; Organizations cannot avoid exchanging information with vendors, suppliers, business partners, and customers. However, the granting of access rights to any IS or network, if not done at the proper level—that is, at the least level of privilege—can leave the IS or ne ...
Whitepaper: Network Penetration Testing - Happiest Minds



Whitepaper: Network Penetration Testing - Happiest MindsHappiest Minds Technologies A Network Penetration Testing is crucial to demystify identify the security exposures that are used to surface when launch a cyber-attacks are launched from internet and intranet.
More insights on Penetration Testing:
http://www.happiestminds.com/Insights/penetration-testing/
What is Penetration Testing?



What is Penetration Testing?Rapid7 A penetration test is often a key requirement for compliance with key regulations. But while many organizations know they need penetration testing, it can be hard to know how to fit them in to a larger security program, or even how to get started. Our whitepaper, "What is Penetration Testing? An Introduction for IT Managers," is a clear and succinct introduction to the core principles and best practices of penetration testing.
Ad
More from Raghav Bisht (19)
OSINT - Yandex Search



OSINT - Yandex SearchRaghav Bisht The document discusses search operators for Yandex, a Russian search engine. It provides examples of over 20 different Yandex boolean operators like +, -, &&, ||, and others. It explains what each operator does and provides examples of queries using the various operators to refine searches on Yandex. The boolean operators allow users to search for exact phrases, exclude terms, define word proximity, search specific fields, and more.
OSINT - Twitter Searches



OSINT - Twitter SearchesRaghav Bisht This document discusses social media intelligence and Twitter advanced search capabilities. It introduces Twitter, explaining that it is a microblogging platform and the 8th most popular website globally. The document also outlines different advanced search operators for Twitter including searching by words, phrases, hashtags, accounts, locations, dates, and tweet properties like whether they are positive, negative, questions, or retweets. It notes that advanced search allows more precise searching than basic search to collect social mentions for social media intelligence purposes.
OSINT Tool - Reconnaissance with Recon-ng



OSINT Tool - Reconnaissance with Recon-ngRaghav Bisht Recon-ng is a Python-based web reconnaissance framework that allows automated reconnaissance. It focuses on open-source intelligence gathering from web-based sources. The tool downloads from Bitbucket and has usage guides there. Recon-ng demonstrations show searching reverse domains, using the Builtwith and Punkspider modules to gather technical information, and using the LinkedIn module to find people at a specific company.
OSINT Tool - Reconnaissance with Maltego



OSINT Tool - Reconnaissance with MaltegoRaghav Bisht This document provides an overview of the open source intelligence (OSINT) tool Maltego. It describes what Maltego is, how it works, and how to install it. Maltego allows users to map relationships between entities like people, organizations, websites, domains, and IP addresses through the use of transforms. It gathers information from online sources and users can write their own transforms and machines. The document provides details on features of Maltego and how to download the commercial or community editions.
OSINT - Linkedin Search Slides



OSINT - Linkedin Search SlidesRaghav Bisht This document discusses search and advanced search features on LinkedIn. It introduces LinkedIn as a professional networking site and explains why it is useful for social media intelligence. It then describes LinkedIn's advanced search page and the various filters that can be used to refine searches, such as keywords, name, title, location, relationship filters, current/past companies, school, languages, interests, and premium member filters. Finally, it explains how Boolean operators like AND, OR, NOT, parentheses, and quotation marks can be used to perform more complex searches on LinkedIn.
OSINT - Facebook Searches



OSINT - Facebook SearchesRaghav Bisht The document discusses social media intelligence (SOCMINT) and how to use Facebook's graph search and search functions to find information about people. It provides examples of different types of queries that can be used to search for people by name, age, location, school, likes, photos, posts, and more. The case study demonstrates how to use these search functions to find information about a black hat hacker named Shadow Walker.
Osint - Dark side of Internet



Osint - Dark side of InternetRaghav Bisht The document discusses the different layers of the internet, including the clearweb which is accessible via search engines, the dark web which search engines don't index, and the deep web which requires special software like Tor or I2P to access. It provides an overview of Tor and I2P anonymity networks, and how to configure them to access the deep web through URLs ending in .onion rather than standard top-level domains. The document also gives an example of a hidden wiki URL that can only be accessed through the Tor browser, not a regular browser.
Intrusion Detection System Project Report



Intrusion Detection System Project ReportRaghav Bisht The following project " Intrusion Detection System " Modules Are :-
1. Firewall
2. Honeypot
3. Dos / Ddos Attack Detection Programs
4. Log Management
Ethical Hacking (CEH) - Industrial Training Report



Ethical Hacking (CEH) - Industrial Training ReportRaghav Bisht This document is Raghav Bisht's report on his 6-week summer training at Bytec0de Securities PVT. LTD from May 25th to July 25th 2013 under the guidance of Mr. Mohit Yadav. The report provides an overview of the training organization, outlines the training objectives and course topics covered, and thanks those who supported his training experience. Key topics covered in the training included introduction to hacking and security, ethical hacking, technology aspects of IT security, hacking steps and techniques like DDoS attacks, wireless hacking, SQL injection, and penetration testing.
Sql injection attack



Sql injection attackRaghav Bisht SQL injection is a code injection technique where malicious SQL statements are inserted into an entry field for execution, allowing a hacker to interfere with a database-driven application's interaction with backend databases. There are different types of SQL injections, including union-based, error-based, and blind SQL injections. Authentication can also be bypassed through SQL injection by making logical conditions like 1=1 or ""="" always true. The document provides examples of SQL injection payloads and demo websites to practice SQL injection techniques.
Os Command Injection Attack



Os Command Injection AttackRaghav Bisht OS command injection vulnerabilities occur when user input is not sanitized before being passed to a shell command interpreter. This allows attackers to inject arbitrary commands that will be executed by the server, potentially compromising the server or application data. Command injection vulnerabilities are serious because they may enable attackers to use the server as a platform for launching attacks against other systems. Commix is an open source tool that can detect and exploit command injection vulnerabilities.
Introduction To Exploitation & Metasploit



Introduction To Exploitation & MetasploitRaghav Bisht Penetration testing involves evaluating systems or networks using malicious techniques to identify security vulnerabilities. It is done by exploiting vulnerabilities to gain unauthorized access to sensitive information. Common vulnerabilities arise from design errors, poor configuration, and human error. Penetration testing is conducted to secure government data transfers, protect brands, and find vulnerabilities in applications, operating systems, databases, and network equipment. Metasploit is an open-source framework used for hacking applications and operating systems that contains exploits, payloads, and modules. Msfconsole is an interface used to launch attacks and create listeners in Metasploit.
Directory Traversal & File Inclusion Attacks



Directory Traversal & File Inclusion AttacksRaghav Bisht Directory traversal, also known as path traversal, allows attackers to access files and directories outside of the web server's designated root folder. This can lead to attacks like file inclusion, where malicious code is executed on the server, and source code disclosure, where sensitive application code is revealed. Local file inclusion allows attackers to include files from the local web server, while remote file inclusion includes files from external websites, potentially allowing remote code execution on the vulnerable server.
Antivirus Bypass Techniques - 2016



Antivirus Bypass Techniques - 2016Raghav Bisht This document discusses techniques for evading antivirus and firewalls, including generating executable files with embedded PowerShell commands to execute backdoors, generating macro-enabled Excel files with encoded payloads to act as Trojans, and using the Shellter tool to dynamically inject shellcode into Windows applications. Figures are provided showing the use of tools like Metasploit and Unicorn to generate payloads and backdoors, embedding them in files, bypassing antivirus detection, and attackers gaining sessions on victim machines.
ccna practical notes



ccna practical notesRaghav Bisht This document contains notes on networking concepts including network requirements, communication media, networking devices, Ethernet cabling, OSI model, TCP/IP protocols, IP addressing, and classes of networks. It defines networking as the method of establishing a connection between two or more computers for data communication and sharing resources. Basic requirements for establishing a network include networking cards and communication media such as wired (coaxial cable, fiber optics, twisted pair) and wireless. Common networking devices are hubs, switches, routers, and bridges.
Hacking in shadows By - Raghav Bisht



Hacking in shadows By - Raghav BishtRaghav Bisht This is my personal CEH Training Notes that have been modified edited and converted into a practical Handbook.
Web-servers & Application Hacking



Web-servers & Application HackingRaghav Bisht This document provides instructions for exploiting various web application vulnerabilities, including remote file inclusion (RFI), local file inclusion (LFI), SQL injection, and more. It begins by explaining RFI and how to exploit it, including using a null byte bypass. It then covers LFI and how to escalate it to remote code execution (RCE). Other sections discuss uploading shells via LFI and Firefox, exploiting vulnerabilities to download local files, full path disclosure, SQL injection techniques, and automatically uploading a shell via a phpThumb() command injection vulnerability. The document aims to serve as a tutorial for hackers to learn various web hacking methods.
Introduction To Hacking



Introduction To HackingRaghav Bisht This document provides an introduction to hacking and security, defining key terms. It explains that hacking involves exploiting vulnerabilities to achieve unauthorized access. Hackers are classified as white hats (ethical), black hats (crackers), or grey hats. The document outlines the importance of understanding systems to secure them through ethical hacking and penetration testing. It lists certifications in security and provides keywords and terms for hackers to be familiar with.
Windows Registry Tips & Tricks



Windows Registry Tips & TricksRaghav Bisht This document provides instructions for making various configuration changes and restrictions in the Windows registry related to system, networking, and application settings. It includes over 50 entries organized by topic that describe how to modify registry keys and values to disable features, restrict access, and modify default behaviors. Examples include disabling the right click context menu, hiding drives, locking file associations, and restricting changes to the start menu and control panel options.
Ad
Recently uploaded (20)
#AdminHour presents: Hour of Code2018 slide deck from 12/6/2018



#AdminHour presents: Hour of Code2018 slide deck from 12/6/2018Lynda Kane Slide Deck from the #AdminHour's Hour of Code session on 12/6/2018 that features learning to code using the Python Turtle library to create snowflakes
Special Meetup Edition - TDX Bengaluru Meetup #52.pptx



Special Meetup Edition - TDX Bengaluru Meetup #52.pptxshyamraj55 We’re bringing the TDX energy to our community with 2 power-packed sessions:
🛠️ Workshop: MuleSoft for Agentforce
Explore the new version of our hands-on workshop featuring the latest Topic Center and API Catalog updates.
📄 Talk: Power Up Document Processing
Dive into smart automation with MuleSoft IDP, NLP, and Einstein AI for intelligent document workflows.
UiPath Community Berlin: Orchestrator API, Swagger, and Test Manager API



UiPath Community Berlin: Orchestrator API, Swagger, and Test Manager APIUiPathCommunity Join this UiPath Community Berlin meetup to explore the Orchestrator API, Swagger interface, and the Test Manager API. Learn how to leverage these tools to streamline automation, enhance testing, and integrate more efficiently with UiPath. Perfect for developers, testers, and automation enthusiasts!
📕 Agenda
Welcome & Introductions
Orchestrator API Overview
Exploring the Swagger Interface
Test Manager API Highlights
Streamlining Automation & Testing with APIs (Demo)
Q&A and Open Discussion
Perfect for developers, testers, and automation enthusiasts!
👉 Join our UiPath Community Berlin chapter: https://community.uipath.com/berlin/
This session streamed live on April 29, 2025, 18:00 CET.
Check out all our upcoming UiPath Community sessions at https://community.uipath.com/events/.
Drupalcamp Finland – Measuring Front-end Energy Consumption



Drupalcamp Finland – Measuring Front-end Energy ConsumptionExove How to measure web front-end energy consumption using Firefox Profiler. Presented in DrupalCamp Finland on April 25th, 2025.
Hands On: Create a Lightning Aura Component with force:RecordData



Hands On: Create a Lightning Aura Component with force:RecordDataLynda Kane Slide Deck from the 3/26/2020 virtual meeting of the Cleveland Developer Group presentation on creating a Lightning Aura Component using force:RecordData.
AI Changes Everything – Talk at Cardiff Metropolitan University, 29th April 2...



AI Changes Everything – Talk at Cardiff Metropolitan University, 29th April 2...Alan Dix Talk at the final event of Data Fusion Dynamics: A Collaborative UK-Saudi Initiative in Cybersecurity and Artificial Intelligence funded by the British Council UK-Saudi Challenge Fund 2024, Cardiff Metropolitan University, 29th April 2025
https://alandix.com/academic/talks/CMet2025-AI-Changes-Everything/
Is AI just another technology, or does it fundamentally change the way we live and think?
Every technology has a direct impact with micro-ethical consequences, some good, some bad. However more profound are the ways in which some technologies reshape the very fabric of society with macro-ethical impacts. The invention of the stirrup revolutionised mounted combat, but as a side effect gave rise to the feudal system, which still shapes politics today. The internal combustion engine offers personal freedom and creates pollution, but has also transformed the nature of urban planning and international trade. When we look at AI the micro-ethical issues, such as bias, are most obvious, but the macro-ethical challenges may be greater.
At a micro-ethical level AI has the potential to deepen social, ethnic and gender bias, issues I have warned about since the early 1990s! It is also being used increasingly on the battlefield. However, it also offers amazing opportunities in health and educations, as the recent Nobel prizes for the developers of AlphaFold illustrate. More radically, the need to encode ethics acts as a mirror to surface essential ethical problems and conflicts.
At the macro-ethical level, by the early 2000s digital technology had already begun to undermine sovereignty (e.g. gambling), market economics (through network effects and emergent monopolies), and the very meaning of money. Modern AI is the child of big data, big computation and ultimately big business, intensifying the inherent tendency of digital technology to concentrate power. AI is already unravelling the fundamentals of the social, political and economic world around us, but this is a world that needs radical reimagining to overcome the global environmental and human challenges that confront us. Our challenge is whether to let the threads fall as they may, or to use them to weave a better future.
2025-05-Q4-2024-Investor-Presentation.pptx



2025-05-Q4-2024-Investor-Presentation.pptxSamuele Fogagnolo Cloudflare Q4 Financial Results Presentation
Cyber Awareness overview for 2025 month of security



Cyber Awareness overview for 2025 month of securityriccardosl1 Cyber awareness training educates employees on risk associated with internet and malicious emails
What is Model Context Protocol(MCP) - The new technology for communication bw...



What is Model Context Protocol(MCP) - The new technology for communication bw...Vishnu Singh Chundawat The MCP (Model Context Protocol) is a framework designed to manage context and interaction within complex systems. This SlideShare presentation will provide a detailed overview of the MCP Model, its applications, and how it plays a crucial role in improving communication and decision-making in distributed systems. We will explore the key concepts behind the protocol, including the importance of context, data management, and how this model enhances system adaptability and responsiveness. Ideal for software developers, system architects, and IT professionals, this presentation will offer valuable insights into how the MCP Model can streamline workflows, improve efficiency, and create more intuitive systems for a wide range of use cases.
AI and Data Privacy in 2025: Global Trends



AI and Data Privacy in 2025: Global TrendsInData Labs In this infographic, we explore how businesses can implement effective governance frameworks to address AI data privacy. Understanding it is crucial for developing effective strategies that ensure compliance, safeguard customer trust, and leverage AI responsibly. Equip yourself with insights that can drive informed decision-making and position your organization for success in the future of data privacy.
This infographic contains:
-AI and data privacy: Key findings
-Statistics on AI data privacy in the today’s world
-Tips on how to overcome data privacy challenges
-Benefits of AI data security investments.
Keep up-to-date on how AI is reshaping privacy standards and what this entails for both individuals and organizations.
Manifest Pre-Seed Update | A Humanoid OEM Deeptech In France



Manifest Pre-Seed Update | A Humanoid OEM Deeptech In Francechb3 The latest updates on Manifest's pre-seed stage progress.
Buckeye Dreamin' 2023: De-fogging Debug Logs



Buckeye Dreamin' 2023: De-fogging Debug LogsLynda Kane Slide Deck from Buckeye Dreamin' 2023: De-fogging Debug Logs which went over how to capture and read Salesforce Debug Logs
Automation Dreamin': Capture User Feedback From Anywhere



Automation Dreamin': Capture User Feedback From AnywhereLynda Kane Slide Deck from Automation Dreamin' 2022 presentation Capture User Feedback from Anywhere
Into The Box Conference Keynote Day 1 (ITB2025)



Into The Box Conference Keynote Day 1 (ITB2025)Ortus Solutions, Corp This is the keynote of the Into the Box conference, highlighting the release of the BoxLang JVM language, its key enhancements, and its vision for the future.
"PHP and MySQL CRUD Operations for Student Management System"



"PHP and MySQL CRUD Operations for Student Management System"Jainul Musani Php with MySQL database Connectivity - CRUD Operations
How Can I use the AI Hype in my Business Context?



How Can I use the AI Hype in my Business Context?Daniel Lehner 𝙄𝙨 𝘼𝙄 𝙟𝙪𝙨𝙩 𝙝𝙮𝙥𝙚? 𝙊𝙧 𝙞𝙨 𝙞𝙩 𝙩𝙝𝙚 𝙜𝙖𝙢𝙚 𝙘𝙝𝙖𝙣𝙜𝙚𝙧 𝙮𝙤𝙪𝙧 𝙗𝙪𝙨𝙞𝙣𝙚𝙨𝙨 𝙣𝙚𝙚𝙙𝙨?
Everyone’s talking about AI but is anyone really using it to create real value?
Most companies want to leverage AI. Few know 𝗵𝗼𝘄.
✅ What exactly should you ask to find real AI opportunities?
✅ Which AI techniques actually fit your business?
✅ Is your data even ready for AI?
If you’re not sure, you’re not alone. This is a condensed version of the slides I presented at a Linkedin webinar for Tecnovy on 28.04.2025.
Linux Professional Institute LPIC-1 Exam.pdf



Linux Professional Institute LPIC-1 Exam.pdfRHCSA Guru Introduction to LPIC-1 Exam - overview, exam details, price and job opportunities
What is Model Context Protocol(MCP) - The new technology for communication bw...



What is Model Context Protocol(MCP) - The new technology for communication bw...Vishnu Singh Chundawat
Introduction To Vulnerability Assessment & Penetration Testing
- 2. Vulnerability Assessment A vulnerability assessment is the process of defining, identifying, classifying and prioritizing vulnerabilities in computer systems, applications and network infrastructures and providing the organization doing the assessment with the necessary knowledge, awareness and risk background to understand the threats to its environment and react appropriately.
- 3. What is Penetration Testing A penetration test, also known as a pen test, is a simulated cyber attack against your network, infrastructure, devices, computer system or any other environment to check for exploitable vulnerabilities.
- 4. Types of Penetration Tests Black Box Penetration Testing White Box Penetration Testing Grey Box Penetration Testing
- 5. Black Box Penetration Testing In black box penetration testing, tester has no idea about the systems that he is going to test. He is interested to gather information about the target network or system. For example, in this testing, a tester only knows what should be the expected outcome and he does not know how the outcomes arrives. He does not examine any programming codes.
- 6. White Box Penetration Testing This is a comprehensive testing, as tester has been provided with whole range of information about the systems and/or network such as Schema, Source code, OS details, IP address, etc. It is normally considered as a simulation of an attack by an internal source. It is also known as structural, glass box, clear box, and open box testing. White box penetration testing examines the code coverage and does data flow testing, path testing, loop testing, etc.
- 7. Grey Box Penetration Testing In this type of testing, a tester usually provides partial or limited information about the internal details of the program of a system. It can be considered as an attack by an external hacker who had gained illegitimate access to an organization's network infrastructure documents.
- 9. Top 10 Common Vulnerabilities SQL Injection Cross Site Scripting Broken Authentication and Session Management Insecure Direct Object References Cross Site Request Forgery Security Misconfiguration Insecure Cryptographic Storage Failure to restrict URL Access Insufficient Transport Layer Protection Un-validated Redirects and Forwards
- 10. Vulnerability Assessment Tools Nexpose Community QualysGuard OpenVAS Nikto Nmap Nessus Professional Acunetix Netsparker IBM AppScan Burp Suite
- 11. Demo Website and VMs https://demo.testfire.net http://testphp.vulnweb.com OWASP Mutillidae II Attack-defense online lab



