Log Monitoring and File Integrity Monitoring
- 1. Log Monitoring, FIM– PCI DSS, ISO 27001, HIPAA, FISMA and EI3PA By Kishor Vaswani, CEO - ControlCase
- 2. Agenda • ControlCase Overview • About PCI DSS, ISO 27001, HIPAA, FISMA and EI3PA • Components of a scalable solution • Challenges • Q&A
- 3. ControlCase™ Corporate Overview Products/Services include ‘Compliance as a Service (CaaS) – PCI, ISO, EI3PA, HIPAA’, ‘Data Discovery Product’ and ‘Certifications/Audits – PCI, ISO 27001, EI3PA, SIG/AUP, HIPAA, HITRUST, FISMA, FedRAMP, SOC1, SOC2 and SOC3’ Over 500 clients IN 40 COUNTRIES across US, CEMEA, Europe and Asia/Pacific regions Headquartered out of Fairfax, VA - USA Offices & Personnel in Canada, Columbia, India, UK, Belgium, Indonesia, Philippines and Dubai
- 4. Other PCI DSS Qualified Security Assessor (QSA) Company ISO 27001 & 27002 International Organization for Standardization SOC 1, SOC 2 & SOC 3 Service Organization Controls (AICPA) HITRUST CSF Health Information Trust Alliance Common Security Framework (CSF) HIPAA Health Insurance Portability and Accountability Act MARS-E Minimum Acceptable Risk Standards for Exchanges Privacy Shield EU-U.S. and Swiss-U.S. Privacy Shield Frameworks NIST 800-53 National Institute of Standards and Technology EI3PA Experian Independent Third Party Assessment PA-DSS Payment Application Qualified Security Assessor (QSA) Third Party Risk Assessor Licensed by the Shared Assessments Program Shared Assessments Program Certified product licensee for SIG and AUP
- 5. About PCI DSS, ISO 27001, HIPAA, FISMA and EI3PA
- 6. What is PCI DSS? Payment Card Industry Data Security Standard: • Guidelines for securely processing, storing, or transmitting payment card account data • Established by leading payment card issuers • Maintained by the PCI Security Standards Council (PCI SSC)
- 7. What is FISMA • Federal Information Security Management Act (FISMA) of 2002 › Requires federal agencies to implement a mandatory set of processes, security controls and information security governance • FISMA objectives: › Align security protections with risk and impact › Establish accountability and performance measures › Empower executives to make informed risk decisions
- 8. What is EI3PA? Experian Security Audit Requirements: • Experian is one of the three major consumer credit bureaus in the United States • Guidelines for securely processing, storing, or transmitting Experian Provided Data • Established by Experian to protect consumer data/credit history data provided by them
- 9. What is HIPAA • HIPAA is the acronym for the Health Insurance Portability and Accountability Act that was passed by Congress in 1996. HIPAA does the following: › Provides the ability to transfer and continue health insurance coverage for millions of American workers and their families when they change or lose their jobs; › Reduces health care fraud and abuse; › Mandates industry-wide standards for health care information on electronic billing and other processes; and › Requires the protection and confidential handling of protected health information
- 10. What is ISO 27001/ISO 27002 ISO Standard: • ISO 27001 is the management framework for implementing information security within an organization • ISO 27002 are the detailed controls from an implementation perspective
- 11. Components of a solution
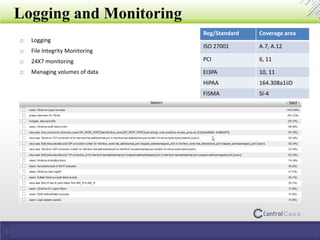
- 12. Logging and Monitoring Reg/Standard Coverage area ISO 27001 A.7, A.12 PCI 6, 11 EI3PA 10, 11 HIPAA 164.308a1iiD FISMA SI-4 Logging File Integrity Monitoring 24X7 monitoring Managing volumes of data
- 13. Components of a Logging/FIM/Monitoring solution List of Assets Log Generation FIM Alerts Correlation using SIEM Centralized Dashboard 24X7x365 monitoring Change Management Incident Management
- 14. Assets • Comprehensive asset list during deployment • Continuous monitoring for new assets and assets dropping off • Correlation with other sources such as scanning and asset management repositories • Alerts in case of new assets and assets dropping off
- 15. Log Generation • Servers – syslog, Windows logs • Network devices – syslog, SNMP, SDEE • Security devices – syslog, SNMP, SDEE • Mainframes – SFTP, flat files • Databases – Localized logging, database logging software in case local logging is resource intensive • Applications – Database lookup, SFTP, custom plugins
- 16. FIM Alerts • Agents such as ossec • Software such as ControlCase HIDS, Tripwire etc. • Integration with log alerts • Monitoring vs. expected changes
- 17. Security Information and Event Management • Consolidated alerts from › Syslog › Custom sources › FIM alerts › SFTP • Correlation of data based on › Source/Destination IP addresses › Source of alerts › Vulnerabilities › Past history › User performing action
- 19. Example of 24X7X365 Monitoring
- 20. Change Management and Monitoring Escalation to incident for unexpected logs/alerts Response/Resolution process for expected logs/alerts Correlation of logs/alerts to change requests Change Management ticketing System Logging and Monitoring (SIEM/FIM etc.) Reg/Standard Coverage area ISO 27001 A.10 PCI 1, 6, 10 EI3PA 1, 9, 10 FISMA SA-3
- 21. Incident and Problem Management Monitoring Detection Reporting Responding Approving Lost Laptop Changes to firewall rulesets Upgrades to applications Intrusion Alerting Reg/Standard Coverage area ISO 27001 A.13 PCI 12 EI3PA 12 HIPAA 164.308a6i FISMA IR Series
- 22. Challenges in Logging and Monitoring Space
- 23. Challenges • Long deployment cycles • Skills to manage the product(s) • Management of infrastructure • Disparate components – FIM, syslog etc. • 24X7X365 monitoring • Increased regulations • Reducing budgets (Do more with less)
- 25. ControlCase Log Management Solution •Agents are installed on each Workstation •Agents monitor File changes for the File Integrity Monitoring (FIM) requirement and also gather and transmit all logs relevant from a compliance perspective to the Log Collector/Sensor on our Appliance • ControlCase appliance registers and tracks all agents in the field •The sensor/collector collects and compresses logs coming in from the various agents •The logs are finally transported securely to our SIEM console in our Security Operations Center (SOC) •The SIEM console gathers all the logs, correlates them and identifies threats and anomalies as required by compliance regulations •SOC personnel monitor the SIEM console 24x7x365 and alert our clients and our Analyst teams about any potential issues related to compliance reporting Customer Location Service Provider ControlCase SOC
- 26. Why Choose ControlCase? • Global Reach › Serving more than 400 clients in 40 countries and rapidly growing • Certified Resources › PCI DSS Qualified Security Assessor (QSA) › QSA for Point-to-Point Encryption (QSA P2PE) › Certified ASV vendor › Certified ISO 27001 Assessment Department › EI3PA Assessor › HIPAA Assessor
- 27. To Learn More About PCI Compliance or Data Discovery… • Visit www.ControlCase.com • Call +1.703.483.6383 (US) • Call +91.9820293399 (India) • Kishor Vaswani (CEO) – [email protected]
- 28. Thank You for Your Time