Reversing & Malware Analysis Training Part 4 - Assembly Programming Basics
- 2. Disclaimer The Content, Demonstration, Source Code and Programs presented here is "AS IS" without any warranty or conditions of any kind. Also the views/ideas/knowledge expressed here are solely of the trainer’s only and nothing to do with the company or the organization in which the trainer is currently working. However in no circumstances neither the trainer nor SecurityXploded is responsible for any damage or loss caused due to use or misuse of the information presented here. www.SecurityXploded.com
- 3. Acknowledgement Special thanks to null & Garage4Hackers community for their extended support and cooperation. Thanks to all the Trainers who have devoted their precious time and countless hours to make it happen. www.SecurityXploded.com
- 4. Reversing & Malware Analysis Training This presentation is part of our Reverse Engineering & Malware Analysis Training program. Currently it is delivered only during our local meet for FREE of cost. For complete details of this course, visit our Security Training page. www.SecurityXploded.com
- 5. Who am I #1 Amit Malik (sometimes DouBle_Zer0,DZZ) Member SecurityXploded & Garage4Hackers Security Researcher RE, Exploit Analysis/Development, Malware Analysis Email: [email protected] www.SecurityXploded.com
- 6. Who am I #2 Swapnil Pathak Member SecurityXploded Security Researcher RE, Malware Analysis, Network Security Email: [email protected] www.SecurityXploded.com
- 7. Presentation Outline Intro to x86-32 Assembly Language Instructions Stack Operations Calling conventions Demo www.SecurityXploded.com
- 8. x86-32 32 bit instruction set architectures based on Intel 8086 CPU Address a linear address space up to 4GB 8, 32 bit General Purpose Registers (GPR) 6,16 bit Segment Registers EFLAGS and EIP register Control Registers (CR0-CR4) (16 bits) Memory Management Registers Descriptor Table Registers (GDTR, IDTR, LDTR) Debug Registers ( DR0-DR7) www.SecurityXploded.com
- 9. Registers Usage - RE Register Storage Locations. Much faster access compare to memory locations. EAX: Accumulator , mostly stores return values from functions (APIs) EBX: Base index (for use with arrays) ECX: Counter EDX: Data/general ESI: Source index for string operations. www.SecurityXploded.com
- 10. Registers Usage – RE Cont. EDI: Destination index for string operations. ESP: Stack pointer for top address of the stack. EBP: Stack base pointer for holding the address of the current stack frame. EIP: Instruction pointer. Holds the program counter, the next instruction address. Segment registers: Used to address particular segments of memory ( code, data, stack ) !) CS: Code !!) SS: Stack !!!) ES: Extra !V) DS: Data V) FS, GS www.SecurityXploded.com
- 11. Registers – 32 bit (X86) www.SecurityXploded.com
- 12. (R/E)Flags Register Bit field of states Status Flags Carrry (CF) : set when an arithmetic carry/borrow has been generated out of the MSB. Zero (ZF) : set when an arithmetic operation result is zero and reset otherwise. Sign (SF) : set when an arithmetic operation set the MSB i.e. the result value was negative. Trap (TF ) : when set permits operation of processor in single-step. Mostly used by debuggers. Interrupt (IF) : determines whether the CPU should handle maskable hardware interrupts. Direction (DF) : determines the direction (left-to-right or right-to-left) of string processing. Overflow (OF) : indicates arithmetic overflow. www.SecurityXploded.com
- 13. Assembly Language Low level programming language Symbolic representation of machine codes, constants. Assembly language program consist of sequence of process instructions and meta statements Assembler translates them to executable instructions that are loaded into memory and executed. Basic Structure [label] : opcode operand1, operand2 opcode – mnemonic that symbolize instructions Example. MOV AL, 61h => 10110000 01100001 www.SecurityXploded.com
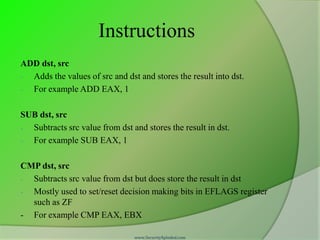
- 14. Instructions ADD dst, src - Adds the values of src and dst and stores the result into dst. - For example ADD EAX, 1 SUB dst, src - Subtracts src value from dst and stores the result in dst. - For example SUB EAX, 1 CMP dst, src - Subtracts src value from dst but does store the result in dst - Mostly used to set/reset decision making bits in EFLAGS register such as ZF - For example CMP EAX, EBX www.SecurityXploded.com
- 15. Instructions cont. MOV dst, src - Moves data from src (left operand) to destination (right operand) - For example mov EDI, ESI Note : - Both operands cannot be memory locations. - Both the operands must be of the same size LEA dst, src - Stands for Load Effective Address. - Computes the effective address of src operand and stores it in dst operand. - For example LEA ECX,[EBX + 5] Note: - Generally brackets denote value at memory locations. - In case of LEA it does simple arithmetic and stores it in dst www.SecurityXploded.com
- 16. Instructions cont. XOR dst, src - Performs a bitwise exclusive OR operation on the dst and src and stores the result in dst. - Each bit of the result is 1 if the corresponding bits of the operands are different, 0 if the corresponding bit are same Note : - When used with same register clears the contents of the register - Optimized way to clear the register. Better than MOV EAX, 0 www.SecurityXploded.com
- 17. Instructions cont. REP - Used with string operations - Repeats a string instruction until ECX (counter register) value is equal to zero. - For example REP MOVS byte ptr DS:[EDI], DS:[ESI] LOOP - Similar to loops in high level languages - Used to execute sequence of instructions multiple times. - For example MOV ECX, 10 Test : INC EBX INC EAX LOOP Test www.SecurityXploded.com
- 18. Instructions cont. TEST dst, src - Performs bitwise logical and between dst and src - Updates the Zero flag bit of the EFLAGS register - Mostly used to check if the return value of the function is not zero - For example TEST EAX, EAX INT 3h - Breakpoint instruction - Used by debuggers to stop execution of the program at particular instruction www.SecurityXploded.com
- 19. Instructions cont. CALL address - Performs two functions - Push address of the next instruction on stack (return address) - Jump to the address specified by the instruction - For example CALL dword ptr [EAX+4] RET - Transfers the control to the address previously pushed on the stack by CALL instruction - Mostly denotes the end of the function www.SecurityXploded.com
- 20. Instructions cont. Jump instructions - Categorized as conditional and unconditional - Unconditional jump instructions - JMP (Far Jump) – E9 – (Cross segments) - JMP ( Short Jump ) – EB – (-127 to 128 bytes) - JMP ( Near Jump ) – E9 – (in a segment) - For example JMP EAX - Conditional jump instructions - Jumps according to bit flags set in the EFLAGS register - JC, JNC, JZ, JNZ, JS, JNS, JO, JNO - Unsigned comparisons JA, JAE, JB, JBE - Signed comparisons JG, JGE, JL, JLE - Usually followed by CMP instruction www.SecurityXploded.com
- 21. Instructions cont. PUSH operand - Pushes operand on the stack - Decrements the stack pointer register by operand size - For example PUSH EAX POP operand - Stores the value pointed by the stack pointer in operand - Increments the stack pointer register by operand size - For example POP EAX Note: POP/PUSH EIP is an invalid instruction PUSHF, POPF www.SecurityXploded.com
- 22. Calling Conventions Describes how the arguments are passed and values returned by functions. Steps performed when a function is called Arguments are passed to the called function Program execution is transferred to the address of the called function Called function starts with lines of code that prepare stack and registers for use within the function. Also known as function prologue. ○ For e.g. push ebp mov ebp, esp or with enter instruction Called function ends with lines of code that restore stack and registers set initially. Also known as function epilogue. ○ For e.g. mov esp, ebp pop ebp ret or with leave instruction Passed arguments are removed from the stack, known as stack cleanup. Can be performed by both calling function or called function depending on the calling convention used. www.SecurityXploded.com
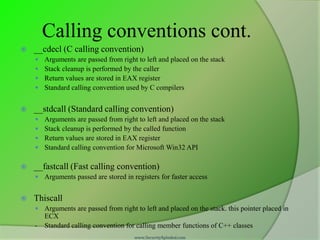
- 23. Calling conventions cont. __cdecl (C calling convention) Arguments are passed from right to left and placed on the stack Stack cleanup is performed by the caller Return values are stored in EAX register Standard calling convention used by C compilers __stdcall (Standard calling convention) Arguments are passed from right to left and placed on the stack Stack cleanup is performed by the called function Return values are stored in EAX register Standard calling convention for Microsoft Win32 API __fastcall (Fast calling convention) Arguments passed are stored in registers for faster access Thiscall Arguments are passed from right to left and placed on the stack. this pointer placed in ECX - Standard calling convention for calling member functions of C++ classes www.SecurityXploded.com
- 24. Stack operations Stack is a LIFO (Last In First Out) type data structure Stacks grows downward in memory, from higher memory address to lower memory address PUSH decrement the stack pointer i.e ESP POP Increment the stack pointer i.e ESP Each function has its own stack frame Function prologue setup the stack frame for each function Local variable of a function are stored into its stack frame www.SecurityXploded.com
- 25. Stack #1 www.SecurityXploded.com
- 26. Stack #2 www.SecurityXploded.com
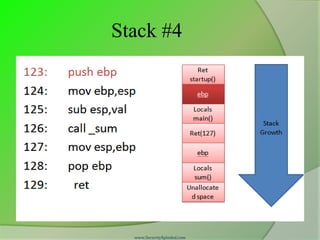
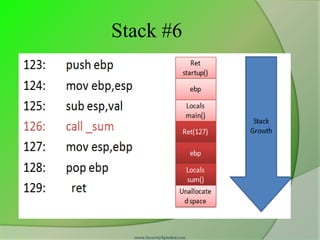
- 27. Stack #3 Each function creates its own stack. Caller function stack: known as parent stack. Called function stack: known as child stack. For e.g. main(){ ASM Pseudo: sum(); _main: } 123: push ebp 124: mov ebp,esp 125: sub esp,val 126: call _sum 127: mov esp,ebp 128: pop ebp 129: ret www.SecurityXploded.com
- 28. Stack #4 www.SecurityXploded.com
- 29. Stack #5 www.SecurityXploded.com
- 30. Stack #6 www.SecurityXploded.com
- 31. DEMO (Source Code) #include <stdio.h> /* Author: Amit Malik http://www.securityxploded.com - Compile in Dev C++ */ int mysum(int,int); int main() { int a,b,s; a = 5; b = 6; s = mysum(a,b); // call mysum function printf("sum is: %d",s); getchar(); } int mysum(int l, int m) // mysum function { int c; c = l + m; return c; } www.SecurityXploded.com
- 33. x86-64 Intro. 64 bit instruction set architectures based on Intel 8086 CPU Address a linear address space up to 16TB 16, 64 bit General Purpose Registers (GPR) 6, 16 bit Segment Registers RFLAGS and RIP register Control Registers (CR0-CR4) and CR8 (16 bits) Memory Management Registers Descriptor Table Registers (GDTR, IDTR, LDTR) size expanded to 10 bytes Debug Registers ( DR0-DR7) www.SecurityXploded.com
- 34. Reference Complete Reference Guide for Reversing & Malware Analysis Training www.SecurityXploded.com
Editor's Notes
- #29: Here main is preparing its stack. EBP (base pointer) register is used to track the variables. So we need to push parent function ebp on the stack so that when function return to parent function it can start normally.
- #30: The instruction mov ebp,esp setting the stack for main(or setting the ebp for main to track variables). And sub esp, val is creating the space for local variables of main function. Although in e.g. we have no local variable but this is for illustrative purpose. NOTE: As we can see in the above pic that stack grows downward (from higher memory address to lower memory address) means something [ebp+val] point to parameters for function (can be pass by value or pass by reference) and everything [ebp-val] point to the local variable for that function.*val- can be any value in hex..like 3,4,a,b etc. etc.Note: ret (startup) address is the address of next instruction in startup function. Explanation of startup function is beyond the scope of this presentation. But main function return 0 or 1 to startup function. Means process successfully completed or error.
- #31: Now main is calling sum. The first task is to push the address of next instruction means address 127 on stack. So that when function sum return it returns to 127 so that program execution continue in a normal way. Please note that no (another) instruction is required to push ret(127) on stack because call sum will do it for us.. Similar to like main, sum will creates its stack with similar instructions and also destroy its stack with similar instructions (127,128,129).Note: The instructions to create stack and destroy stack.. may vary with compiler to complier and are the issues of compiler optimization..for eg.Some compilers user push reg. instead of sub esp,val for integers.













![Assembly Language
Low level programming language
Symbolic representation of machine codes, constants.
Assembly language program consist of sequence of process instructions
and meta statements
Assembler translates them to executable instructions that are loaded into
memory and executed.
Basic Structure
[label] : opcode operand1, operand2
opcode – mnemonic that symbolize instructions
Example.
MOV AL, 61h => 10110000 01100001
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-120205040313-phpapp02/85/Reversing-Malware-Analysis-Training-Part-4-Assembly-Programming-Basics-13-320.jpg)
![Instructions cont.
MOV dst, src
- Moves data from src (left operand) to destination (right operand)
- For example mov EDI, ESI
Note :
- Both operands cannot be memory locations.
- Both the operands must be of the same size
LEA dst, src
- Stands for Load Effective Address.
- Computes the effective address of src operand and stores it in dst operand.
- For example LEA ECX,[EBX + 5]
Note:
- Generally brackets denote value at memory locations.
- In case of LEA it does simple arithmetic and stores it in dst
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-120205040313-phpapp02/85/Reversing-Malware-Analysis-Training-Part-4-Assembly-Programming-Basics-15-320.jpg)

![Instructions cont.
REP
- Used with string operations
- Repeats a string instruction until ECX (counter register) value is equal to
zero.
- For example REP MOVS byte ptr DS:[EDI], DS:[ESI]
LOOP
- Similar to loops in high level languages
- Used to execute sequence of instructions multiple times.
- For example
MOV ECX, 10
Test : INC EBX
INC EAX
LOOP Test
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-120205040313-phpapp02/85/Reversing-Malware-Analysis-Training-Part-4-Assembly-Programming-Basics-17-320.jpg)

![Instructions cont.
CALL address
- Performs two functions
- Push address of the next instruction on stack (return address)
- Jump to the address specified by the instruction
- For example CALL dword ptr [EAX+4]
RET
- Transfers the control to the address previously pushed on the stack
by CALL instruction
- Mostly denotes the end of the function
www.SecurityXploded.com](https://image.slidesharecdn.com/reversingmalwareanalysistrainingpart4-assemblyprogrammingbasics-120205040313-phpapp02/85/Reversing-Malware-Analysis-Training-Part-4-Assembly-Programming-Basics-19-320.jpg)