Security on Rails
Download as ODP, PDF1 like844 views
This document discusses various security vulnerabilities in Ruby on Rails applications including session hijacking, CSRF, mass assignment, and SQL injection. It provides recommendations to address these issues such as using SSL, adding session expiration, sanitizing user input, and using parameterized queries. The key takeaway is that security must be an ongoing process as new vulnerabilities emerge, and failing to address issues can enable catastrophic attacks on applications and user data.
1 of 23
Downloaded 13 times













![Header Injection
redirect_to params[:referer]
http://www.yourapplication.com/controller/action?
referer=http://www.malicious.tld
Make sure you do it yourself when you
build other header fields with user input.](https://image.slidesharecdn.com/securityonrails-121007203413-phpapp01/85/Security-on-Rails-14-320.jpg)




![SQL Injection
● Project.where("name = '#{params[:name]}'")
SELECT * FROM projects WHERE name = '' OR 1'
● User.first("login = '#{params[:name]}' AND
password = '#{params[:password]}'")
SELECT * FROM users WHERE login = '' OR '1'='1' AND
password = '' OR '2'>'1' LIMIT 1](https://image.slidesharecdn.com/securityonrails-121007203413-phpapp01/85/Security-on-Rails-20-320.jpg)



Ad
Recommended
The Next Five Years of Rails



The Next Five Years of RailsAlex Mercer The document discusses the benefits of conventions in Rails and the need for conventions in building APIs and client-side frameworks. It argues that conventions save developers from having to make trivial decisions and push problems into shared solutions. While Rails has benefited from conventions like REST, there is still room to improve APIs and make them as transparent as ActiveRecord. ActiveModel::Serializers is presented as one approach to provide conventions for serialization. The document also discusses how conventions could improve browser frameworks and application structure beyond just code organization.
Java Web Application Security with Java EE, Spring Security and Apache Shiro ...



Java Web Application Security with Java EE, Spring Security and Apache Shiro ...Matt Raible This document provides an overview of options for implementing security in Java web applications, including Java EE, Spring Security, and Apache Shiro. It discusses developing secure applications, common vulnerabilities, and tools for testing security like OWASP Zed Attack Proxy. The document emphasizes that security should be built into applications from the start through following best practices and using security frameworks.
Scalable CSS You and Your Back-End Coders Can Love - @CSSConf Asia 2014



Scalable CSS You and Your Back-End Coders Can Love - @CSSConf Asia 2014Christian Lilley This document discusses strategies for making CSS more scalable and maintainable. It recommends automating CSS with preprocessors, using clear and descriptive class names, avoiding descendant selectors when possible, and minimizing unnecessary nesting and complexity. Pseudoselectors should only be used when other options aren't available. Overall, the document emphasizes writing CSS according to first principles of maintainability, predictability and avoiding premature optimization.
The Complementarity of React and Web Components



The Complementarity of React and Web ComponentsAndrew Rota On Github: http://andrewrota.github.io/complementarity-of-react-and-web-components-presentation/index.html
The component driven, performance focused approach of React is a perfect complement to the modularity and portability of native HTML Web Components. At first glance, React and Web Components might seem like two radically different solutions to the same problem. But when combined properly they complement each other to create an extremely powerful, expressive framework for developing complex web applications.
Esri Dev Summit 2009 Rest and Mvc Final



Esri Dev Summit 2009 Rest and Mvc Finalguestcd4688 This document discusses building RESTful applications and services with ASP.NET MVC. It promotes using standards like JSON and HTTP verbs to build clean, intuitive REST APIs. It also advocates for unit testing at multiple levels (views, controllers, repositories, data access layers) to catch errors early and ensure quality. Architecting applications with separate models, views, controllers, repositories and data access layers is recommended to keep code organized and flexible.
Introduction to Backbone.js & Marionette.js



Introduction to Backbone.js & Marionette.jsReturn on Intelligence The document discusses frontend application development using jQuery and improvements that can be made. It notes that while jQuery is easy for small amounts of code, complexity grows quickly without proper architecture. It recommends separating view logic from business logic, using proven patterns like MVC/MVVM, creating a custom solution, or leveraging an existing framework. Backbone.js and Marionette.js are introduced as frameworks that can provide structure and simplify code. Key concepts like models, collections, views, and templating are explained for building maintainable single page applications.
SenchaCon 2016: Expect the Unexpected - Dealing with Errors in Web Apps



SenchaCon 2016: Expect the Unexpected - Dealing with Errors in Web AppsSencha This document discusses handling errors in web applications. It begins by explaining what JavaScript errors are and how they are typically invisible to users. It then discusses how to catch errors using window.onerror or addEventListener and logging errors to help debug issues. Ideal error handling involves logging detailed error information to a database and notifying developers. The document wishes for more context around errors, like function arguments or AJAX requests. It introduces a new error logging and monitoring tool that provides detailed user environment data, function arguments, screenshots, and a timeline to help developers debug issues more easily.
Top Ten Web Application Defenses v12



Top Ten Web Application Defenses v12Jim Manico We cannot “firewall” or “patch” our way to secure websites. In the past, security professionals thought firewalls, Secure Sockets Layer (SSL), patching, and privacy policies were enough. Today, however, these methods are outdated and ineffective, as attacks on prominent, well-protected websites are occurring every day. Most every organization in the world have something in common – they have had websites compromised in some way. No company or industry is immune. Programmers need to learn to build websites differently. This talk will review the top coding techniques developers need to master in order to build a low-risk, high-security web application.
Javaland 2017: "You´ll do microservices now". Now what?



Javaland 2017: "You´ll do microservices now". Now what?André Goliath The slides for my talk at JavaLand 2017. Note: The slides are in english, only the title is german. The talk is all about do's and dont's in microservice landscapes.
Von JavaEE auf Microservice in 6 Monaten - The Good, the Bad, and the wtfs...



Von JavaEE auf Microservice in 6 Monaten - The Good, the Bad, and the wtfs...André Goliath This document summarizes a talk about transitioning from JavaEE monoliths to microservices architecture in 6 months. It discusses the reasons for moving to microservices (faster development and deployment, lower costs), and the challenges including organizing configuration, communication between services, and deployment. It then outlines the steps taken to implement microservices at a company, including setting up continuous integration, using Spring Boot and Cloud, and establishing vertical feature teams to overcome organizational barriers. The key lessons are that the transition does not require a "big bang", can start with a single service, and works best by automating the development and deployment process from development to production.
Das kannste schon so machen



Das kannste schon so machenAndré Goliath me ranting about the downsides of Spring Boot / Netflix OSS. Sorry that the slides are a little rare on text, so most likely hard to understand without the actual talk. feel free to send me any questions, though!
Getting started with angular js



Getting started with angular jsMaurice De Beijer [MVP] There are lots of libraries and frameworks you can use when building browser based JavaScript applications. Probably the most popular library is jQuery. But while jQuery makes it easy to write cross browser user interface code that manipulates the DOM it’s UI focus makes it less then perfect for large business applications. One of the JavaScript based MVC frameworks that has been gaining a lot of popularity for creating business applications is AngularJS. Wen using AngularJS you get the benefit of a powerful data-binding framework that guides you towards a proper application model with a proper separation between the UI layer and the business layer. It also contains a powerful dependency injection framework making code much more testable than before.
In this session Maurice de Beijer will show you how to get started with AngularJS and how productive you can be when creating line of business applications.
webcomponents (Jfokus 2015)



webcomponents (Jfokus 2015)Hendrik Ebbers This document provides an overview and introduction to web components. It discusses the key aspects of web components including custom elements, HTML imports, shadow DOM, and templates. It also shows how web components allow building reusable custom elements that encapsulate their styles and functionality independently of the page they are used in. The document demonstrates how to define and register a custom element for displaying activity cards and use templates and shadow DOM to encapsulate its implementation.
Our application got popular and now it breaks



Our application got popular and now it breaksColdFusionConference Our application got popular and now breaks under load. The document discusses common issues that cause applications to break as user load increases, such as overuse of shared scopes, inefficient database queries, and slow client-side performance. It provides examples of better approaches and techniques to optimize performance, such as using distributed caching, improving query efficiency through joins, compressing assets, and prioritizing critical CSS and JavaScript.
Authenticating and Securing Node.js APIs



Authenticating and Securing Node.js APIsJimmy Guerrero The document discusses various topics related to implementing authentication and authorization in LoopBack applications. It covers setting up SSL, configuring OAuth2, adding third-party login support using Passport strategies, defining roles and ACLs, and deploying LoopBack apps for microservices and hyper-scale.
Building Layers of Defense with Spring Security



Building Layers of Defense with Spring SecurityJoris Kuipers It's not enough to secure your applications by simply locking the front door, expecting that that will keep attackers out. Modern web applications require security at many different levels: using appropriate HTTP headers, preventing CSRF and CORS attacks, matching URLs, securing method invocations, performing multi-tenancy and other ownership-based checks, etc.
In this presentation, Joris shows how to address these concerns with Spring Security, an OSS framework for securing Java-based web applications. He covers the built-in features, but also demonstrates how to extend those with custom functionality to meet the security needs that many applications have.
OWASP SF - Reviewing Modern JavaScript Applications



OWASP SF - Reviewing Modern JavaScript ApplicationsLewis Ardern The document provides an overview of reviewing modern JavaScript applications for security. It discusses how JavaScript is used widely, common frameworks like React and Angular, and tools for analyzing JavaScript like ESLint. It also covers real-world examples of vulnerabilities like cross-site scripting and remote code execution. The talk emphasizes embracing developer tools and best practices like code reviews and linting to identify security issues in JavaScript applications.
Cross Site Scripting (XSS) Defense with Java



Cross Site Scripting (XSS) Defense with JavaJim Manico Cross Site Scripting Defense is difficult. The Java Programming language does not provide native key defenses necessary to throughly prevent XSS. As technologies such as Content Security Policy emerge, we still need pragmatic advice to stop XSS in legacy applications as well as new applications using traditional Java frameworks. First generation encoding libraries had both performance and completeness problems that prevent developers from through, production-safe XSS defense. This talk will deeply review the OWASP Java Encoder Project and the OWASP HTML Sanitizer Project and give detailed code samples highlighting their use. Additional advice on next-generation JavaScript and JSON workflows using the OWASP JSON Sanitizer will also be reviewed.
Top Ten Proactive Web Security Controls v5



Top Ten Proactive Web Security Controls v5Jim Manico It is not easy to build a secure, low-risk or risk-managed web application. Firewalls, “policy” and other traditional information security measures serve as either an incomplete or useless measure in the pursuit of web application security.
As software developers author the code that makes up a web application, they need to do so in a secure manner. All tiers of a web application, the user interface, the business logic, the controller, the database code and more – all need to be developed with security in mind. This can be a very difficult task and developers are often set up for failure. Most developers did not learn about secure coding or crypto in school. The languages and frameworks that developers use to build web applications are often lacking critical core controls or are insecure by default in some way. There may be inherent flaws in requirements and designs. It is also very rare when organizations provide developers with prescriptive requirements that guide them down the path of secure software. When it comes to web security, developers are often set up to lose the security game.
This document was written by developers for developers, to assist those new to secure development. It aims to guide developers and other software development professionals down the path of secure web application software development.
This document is neither scientific nor complete. In fact it is a bit misguided. There are more than 10 issues that developers need to be aware of. Some of these “top ten” controls will be very specific, others will be general categories. Some of these items are technical, others are process based. Some may argue that this document includes items that are not even controls at all. All of these concerns are fair. Again, this is an awareness document meant for those new to secure software development. It is a start, not an end.
AtlasCamp 2014: 10 Things a Front End Developer Should Know About Connect



AtlasCamp 2014: 10 Things a Front End Developer Should Know About ConnectAtlassian If you're a JavaScript developer, you can't miss this session. Atlassian Connect presents some challenges that might be new to JavaScript developers, like third-party cookie policy, window.postMessage, and sending data between multiple iframes, just to name a few. This session will address these challenges and offer practical tips from the trenches of building new add-ons with Atlassian Connect.
Design & Development of Web Applications using SpringMVC 



Design & Development of Web Applications using SpringMVC Naresh Chintalcheru Spring MVC is a web MVC framework that provides a reusable presentation layer for web applications. It removes boilerplate code and standardizes navigation flow and validation. Spring MVC controllers handle HTTP requests and delegate work to service objects. It uses the front controller design pattern and is view-agnostic, allowing different view technologies. Spring MVC applications are configured through XML files and use annotations for components and request mapping.
Cutting the Fat



Cutting the FatCodemotion Rich, interactive web applications AKA fat clients are now commonplace. There are so many frameworks for building these rich client applications, and the debate among developers is which of these frameworks to use. As designers and developers we need to step back, and ask ourselves when and how we should enrich our client applications and when or why not. Let’s dig in to the question: Why do we even want fat clients, and when should we use them? Let’s examine the complications such clients introduce so we can weigh them against all the benefits.
XSS Magic tricks



XSS Magic tricksGarethHeyes This talk shares the various techniques I found whilst building the XSS cheat sheet. It contains auto executing vectors, AngularJS CSP bypasses and dangling markup attacks.
Azure Container Apps



Azure Container AppsICS This document provides an introduction to Azure Container Apps, Azure Container Registry, and GitHub Actions. It discusses that Azure Container Apps provides a serverless environment for running containerized applications without needing to manage infrastructure. It also describes Azure Container Registry as a private Docker registry and GitHub Actions for automating software development workflows. The document concludes with references and a demo of hands-on labs to showcase these services.
The Future of CSS with Web Components



The Future of CSS with Web ComponentsColdFusionConference This document discusses the future of CSS and web development with web components. It introduces some key concepts in web components like templates, shadow DOM, custom elements, and HTML imports. Templates allow creating hidden chunks of HTML, shadow DOM provides encapsulation for styling, custom elements define new HTML tags, and HTML imports bundle related scripts and styles. Web components aim to address issues with current frontend development approaches and enable more modular and reusable code with standards like templates, shadow DOM, and custom elements. Polyfills can provide support for these features in older browsers. Popular web component libraries include Polymer and Mozilla Brick which provide pre-built reusable elements.
Mvvm knockout vs angular



Mvvm knockout vs angularBasarat Syed A presentation I gave at ALT.NET Melbourne on February 26 2013 : http://www.basarat.com/2013/03/knockout-vs-angularjs-mvvm-frameworks.html
An Introduction to webOS



An Introduction to webOSKevin Decker webOS is an open source mobile operating system from Palm built on HTML5, CSS, and JavaScript that uses the Mojo framework for application development and provides services through a plugin development kit and application programming interfaces, with apps distributed through an online app catalog.
Global Windows Azure Bootcamp : Cedric Derue playing with php on azure. (spon...



Global Windows Azure Bootcamp : Cedric Derue playing with php on azure. (spon...MUG-Lyon Microsoft User Group This document summarizes a presentation about playing with PHP on Azure using the Zend Framework. It discusses:
- Using the Zend Framework 2 with Azure Web Sites to build scalable PHP applications in the cloud.
- Key Azure services like Web Sites, Storage, and Mobile that can be used to deploy and scale PHP applications.
- Steps to create a new Zend Framework 2 application on an Azure Web Site and connect it to Azure SQL and Storage.
- Ensuring applications can be reversed from the cloud to on-premise environments through configuration.
- Monitoring tools for cloud applications like New Relic and Application Insights.
Security in Node.JS and Express:



Security in Node.JS and Express:Petros Demetrakopoulos - Server-side JavaScript injection, cross-site scripting attacks, SQL injections, and cross-site request forgery are common security vulnerabilities in Node.js and Express applications. The document provides recommendations to prevent each vulnerability, including validating user input, escaping output, using prepared statements, and implementing CSRF tokens.
- Data validation and sanitization should be implemented for all endpoints accepting user data. Packages like express-validator can define validation schemas and sanitize input. Logging each request and response is also important for security monitoring and auditing.
Neoito — Secure coding practices



Neoito — Secure coding practicesNeoito Secure coding is the practice of developing computer software in a way that guards against the accidental introduction of security vulnerabilities. Defects, bugs and logic flaws are consistently the primary cause of commonly exploited software vulnerabilities. Through the analysis of thousands of reported vulnerabilities, security professionals have discovered that most vulnerabilities stem from a relatively small number of common software programming errors. By identifying the insecure coding practices that lead to these errors and educating developers on secure alternatives, organizations can take proactive steps to help significantly reduce or eliminate vulnerabilities in software before deployment.
Session by: Akash S Prakash
Ad
More Related Content
What's hot (20)
Javaland 2017: "You´ll do microservices now". Now what?



Javaland 2017: "You´ll do microservices now". Now what?André Goliath The slides for my talk at JavaLand 2017. Note: The slides are in english, only the title is german. The talk is all about do's and dont's in microservice landscapes.
Von JavaEE auf Microservice in 6 Monaten - The Good, the Bad, and the wtfs...



Von JavaEE auf Microservice in 6 Monaten - The Good, the Bad, and the wtfs...André Goliath This document summarizes a talk about transitioning from JavaEE monoliths to microservices architecture in 6 months. It discusses the reasons for moving to microservices (faster development and deployment, lower costs), and the challenges including organizing configuration, communication between services, and deployment. It then outlines the steps taken to implement microservices at a company, including setting up continuous integration, using Spring Boot and Cloud, and establishing vertical feature teams to overcome organizational barriers. The key lessons are that the transition does not require a "big bang", can start with a single service, and works best by automating the development and deployment process from development to production.
Das kannste schon so machen



Das kannste schon so machenAndré Goliath me ranting about the downsides of Spring Boot / Netflix OSS. Sorry that the slides are a little rare on text, so most likely hard to understand without the actual talk. feel free to send me any questions, though!
Getting started with angular js



Getting started with angular jsMaurice De Beijer [MVP] There are lots of libraries and frameworks you can use when building browser based JavaScript applications. Probably the most popular library is jQuery. But while jQuery makes it easy to write cross browser user interface code that manipulates the DOM it’s UI focus makes it less then perfect for large business applications. One of the JavaScript based MVC frameworks that has been gaining a lot of popularity for creating business applications is AngularJS. Wen using AngularJS you get the benefit of a powerful data-binding framework that guides you towards a proper application model with a proper separation between the UI layer and the business layer. It also contains a powerful dependency injection framework making code much more testable than before.
In this session Maurice de Beijer will show you how to get started with AngularJS and how productive you can be when creating line of business applications.
webcomponents (Jfokus 2015)



webcomponents (Jfokus 2015)Hendrik Ebbers This document provides an overview and introduction to web components. It discusses the key aspects of web components including custom elements, HTML imports, shadow DOM, and templates. It also shows how web components allow building reusable custom elements that encapsulate their styles and functionality independently of the page they are used in. The document demonstrates how to define and register a custom element for displaying activity cards and use templates and shadow DOM to encapsulate its implementation.
Our application got popular and now it breaks



Our application got popular and now it breaksColdFusionConference Our application got popular and now breaks under load. The document discusses common issues that cause applications to break as user load increases, such as overuse of shared scopes, inefficient database queries, and slow client-side performance. It provides examples of better approaches and techniques to optimize performance, such as using distributed caching, improving query efficiency through joins, compressing assets, and prioritizing critical CSS and JavaScript.
Authenticating and Securing Node.js APIs



Authenticating and Securing Node.js APIsJimmy Guerrero The document discusses various topics related to implementing authentication and authorization in LoopBack applications. It covers setting up SSL, configuring OAuth2, adding third-party login support using Passport strategies, defining roles and ACLs, and deploying LoopBack apps for microservices and hyper-scale.
Building Layers of Defense with Spring Security



Building Layers of Defense with Spring SecurityJoris Kuipers It's not enough to secure your applications by simply locking the front door, expecting that that will keep attackers out. Modern web applications require security at many different levels: using appropriate HTTP headers, preventing CSRF and CORS attacks, matching URLs, securing method invocations, performing multi-tenancy and other ownership-based checks, etc.
In this presentation, Joris shows how to address these concerns with Spring Security, an OSS framework for securing Java-based web applications. He covers the built-in features, but also demonstrates how to extend those with custom functionality to meet the security needs that many applications have.
OWASP SF - Reviewing Modern JavaScript Applications



OWASP SF - Reviewing Modern JavaScript ApplicationsLewis Ardern The document provides an overview of reviewing modern JavaScript applications for security. It discusses how JavaScript is used widely, common frameworks like React and Angular, and tools for analyzing JavaScript like ESLint. It also covers real-world examples of vulnerabilities like cross-site scripting and remote code execution. The talk emphasizes embracing developer tools and best practices like code reviews and linting to identify security issues in JavaScript applications.
Cross Site Scripting (XSS) Defense with Java



Cross Site Scripting (XSS) Defense with JavaJim Manico Cross Site Scripting Defense is difficult. The Java Programming language does not provide native key defenses necessary to throughly prevent XSS. As technologies such as Content Security Policy emerge, we still need pragmatic advice to stop XSS in legacy applications as well as new applications using traditional Java frameworks. First generation encoding libraries had both performance and completeness problems that prevent developers from through, production-safe XSS defense. This talk will deeply review the OWASP Java Encoder Project and the OWASP HTML Sanitizer Project and give detailed code samples highlighting their use. Additional advice on next-generation JavaScript and JSON workflows using the OWASP JSON Sanitizer will also be reviewed.
Top Ten Proactive Web Security Controls v5



Top Ten Proactive Web Security Controls v5Jim Manico It is not easy to build a secure, low-risk or risk-managed web application. Firewalls, “policy” and other traditional information security measures serve as either an incomplete or useless measure in the pursuit of web application security.
As software developers author the code that makes up a web application, they need to do so in a secure manner. All tiers of a web application, the user interface, the business logic, the controller, the database code and more – all need to be developed with security in mind. This can be a very difficult task and developers are often set up for failure. Most developers did not learn about secure coding or crypto in school. The languages and frameworks that developers use to build web applications are often lacking critical core controls or are insecure by default in some way. There may be inherent flaws in requirements and designs. It is also very rare when organizations provide developers with prescriptive requirements that guide them down the path of secure software. When it comes to web security, developers are often set up to lose the security game.
This document was written by developers for developers, to assist those new to secure development. It aims to guide developers and other software development professionals down the path of secure web application software development.
This document is neither scientific nor complete. In fact it is a bit misguided. There are more than 10 issues that developers need to be aware of. Some of these “top ten” controls will be very specific, others will be general categories. Some of these items are technical, others are process based. Some may argue that this document includes items that are not even controls at all. All of these concerns are fair. Again, this is an awareness document meant for those new to secure software development. It is a start, not an end.
AtlasCamp 2014: 10 Things a Front End Developer Should Know About Connect



AtlasCamp 2014: 10 Things a Front End Developer Should Know About ConnectAtlassian If you're a JavaScript developer, you can't miss this session. Atlassian Connect presents some challenges that might be new to JavaScript developers, like third-party cookie policy, window.postMessage, and sending data between multiple iframes, just to name a few. This session will address these challenges and offer practical tips from the trenches of building new add-ons with Atlassian Connect.
Design & Development of Web Applications using SpringMVC 



Design & Development of Web Applications using SpringMVC Naresh Chintalcheru Spring MVC is a web MVC framework that provides a reusable presentation layer for web applications. It removes boilerplate code and standardizes navigation flow and validation. Spring MVC controllers handle HTTP requests and delegate work to service objects. It uses the front controller design pattern and is view-agnostic, allowing different view technologies. Spring MVC applications are configured through XML files and use annotations for components and request mapping.
Cutting the Fat



Cutting the FatCodemotion Rich, interactive web applications AKA fat clients are now commonplace. There are so many frameworks for building these rich client applications, and the debate among developers is which of these frameworks to use. As designers and developers we need to step back, and ask ourselves when and how we should enrich our client applications and when or why not. Let’s dig in to the question: Why do we even want fat clients, and when should we use them? Let’s examine the complications such clients introduce so we can weigh them against all the benefits.
XSS Magic tricks



XSS Magic tricksGarethHeyes This talk shares the various techniques I found whilst building the XSS cheat sheet. It contains auto executing vectors, AngularJS CSP bypasses and dangling markup attacks.
Azure Container Apps



Azure Container AppsICS This document provides an introduction to Azure Container Apps, Azure Container Registry, and GitHub Actions. It discusses that Azure Container Apps provides a serverless environment for running containerized applications without needing to manage infrastructure. It also describes Azure Container Registry as a private Docker registry and GitHub Actions for automating software development workflows. The document concludes with references and a demo of hands-on labs to showcase these services.
The Future of CSS with Web Components



The Future of CSS with Web ComponentsColdFusionConference This document discusses the future of CSS and web development with web components. It introduces some key concepts in web components like templates, shadow DOM, custom elements, and HTML imports. Templates allow creating hidden chunks of HTML, shadow DOM provides encapsulation for styling, custom elements define new HTML tags, and HTML imports bundle related scripts and styles. Web components aim to address issues with current frontend development approaches and enable more modular and reusable code with standards like templates, shadow DOM, and custom elements. Polyfills can provide support for these features in older browsers. Popular web component libraries include Polymer and Mozilla Brick which provide pre-built reusable elements.
Mvvm knockout vs angular



Mvvm knockout vs angularBasarat Syed A presentation I gave at ALT.NET Melbourne on February 26 2013 : http://www.basarat.com/2013/03/knockout-vs-angularjs-mvvm-frameworks.html
An Introduction to webOS



An Introduction to webOSKevin Decker webOS is an open source mobile operating system from Palm built on HTML5, CSS, and JavaScript that uses the Mojo framework for application development and provides services through a plugin development kit and application programming interfaces, with apps distributed through an online app catalog.
Global Windows Azure Bootcamp : Cedric Derue playing with php on azure. (spon...



Global Windows Azure Bootcamp : Cedric Derue playing with php on azure. (spon...MUG-Lyon Microsoft User Group This document summarizes a presentation about playing with PHP on Azure using the Zend Framework. It discusses:
- Using the Zend Framework 2 with Azure Web Sites to build scalable PHP applications in the cloud.
- Key Azure services like Web Sites, Storage, and Mobile that can be used to deploy and scale PHP applications.
- Steps to create a new Zend Framework 2 application on an Azure Web Site and connect it to Azure SQL and Storage.
- Ensuring applications can be reversed from the cloud to on-premise environments through configuration.
- Monitoring tools for cloud applications like New Relic and Application Insights.
Global Windows Azure Bootcamp : Cedric Derue playing with php on azure. (spon...



Global Windows Azure Bootcamp : Cedric Derue playing with php on azure. (spon...MUG-Lyon Microsoft User Group
Similar to Security on Rails (20)
Security in Node.JS and Express:



Security in Node.JS and Express:Petros Demetrakopoulos - Server-side JavaScript injection, cross-site scripting attacks, SQL injections, and cross-site request forgery are common security vulnerabilities in Node.js and Express applications. The document provides recommendations to prevent each vulnerability, including validating user input, escaping output, using prepared statements, and implementing CSRF tokens.
- Data validation and sanitization should be implemented for all endpoints accepting user data. Packages like express-validator can define validation schemas and sanitize input. Logging each request and response is also important for security monitoring and auditing.
Neoito — Secure coding practices



Neoito — Secure coding practicesNeoito Secure coding is the practice of developing computer software in a way that guards against the accidental introduction of security vulnerabilities. Defects, bugs and logic flaws are consistently the primary cause of commonly exploited software vulnerabilities. Through the analysis of thousands of reported vulnerabilities, security professionals have discovered that most vulnerabilities stem from a relatively small number of common software programming errors. By identifying the insecure coding practices that lead to these errors and educating developers on secure alternatives, organizations can take proactive steps to help significantly reduce or eliminate vulnerabilities in software before deployment.
Session by: Akash S Prakash
OWASP ZAP Workshop for QA Testers



OWASP ZAP Workshop for QA TestersJavan Rasokat The document discusses OWASP Zed Attack Proxy (ZAP), a free and open source web application security scanner. It can be used by pentesters, developers, and testers to detect vulnerabilities. ZAP passively and actively scans applications to find issues. It can be integrated into CI/CD pipelines and automated with APIs, command line tools, and programming libraries. The document provides examples of using ZAP to perform passive scanning, active scanning, and automation for testers.
Rails Security



Rails SecurityWen-Tien Chang Rails security best practices involve defending at multiple layers including the network, operating system, web server, web application, and database. The document outlines numerous vulnerabilities at the web application layer such as information leaks, session hijacking, SQL injection, mass assignment, unscoped finds, cross-site scripting (XSS), cross-site request forgery (CSRF), and denial-of-service attacks. It provides recommendations to address each vulnerability through secure coding practices and configuration in Rails.
Breaking Bad CSP



Breaking Bad CSPLukas Weichselbaum This document discusses Content Security Policy (CSP) and strategies for implementing it effectively. It begins with an introduction to CSP and its goals of mitigating risk, reducing privileges, and detecting exploitation. It then covers common CSP policies, mistakes that can undermine security, and ways attacks can bypass CSP restrictions. The document proposes using strict nonce-based CSP with the 'unsafe-dynamic' feature to more easily deploy CSP without whitelists. It concludes with success stories of this approach and a call for feedback on CSP strategies.
DevOps and the Future of Enterprise Security



DevOps and the Future of Enterprise SecurityFrank Kim What security leaders can do to understand, support, and adopt leading DevOps practices to operate at the "speed of business".
JSMVCOMFG - To sternly look at JavaScript MVC and Templating Frameworks



JSMVCOMFG - To sternly look at JavaScript MVC and Templating FrameworksMario Heiderich The document discusses JavaScript MVC and templating frameworks and security issues found during penetration testing. Several frameworks were found to execute arbitrary JavaScript from markup in dangerous ways due to overuse of eval-like functions and lack of separation between code and content. This could lead to bypassing of content security policies. Metrics are proposed to evaluate frameworks on security practices like sandboxing and preventing injection into templates. While challenges exist, following best practices like strict separation of code and content could help frameworks improve security.
Pawel Cygal - SQL Injection and XSS - Basics (Quality Questions Conference)



Pawel Cygal - SQL Injection and XSS - Basics (Quality Questions Conference)Grand Parade Poland Paweł Cygal, a senior system administrator at Grand Parade, gives a presentation covering SQL injection and cross-site scripting (XSS) basics with examples using the Damn Vulnerable Web Application. The presentation defines SQL injection as a code injection technique used to attack data-driven applications by inserting malicious SQL statements. XSS enables attackers to inject client-side scripts by exploiting vulnerabilities in how a web application processes user input. Examples are provided of SQL injection and XSS vulnerabilities, along with solutions like prepared statements, input validation, and output encoding.
09 - express nodes on the right angle - vitaliy basyuk - it event 2013 (5)



09 - express nodes on the right angle - vitaliy basyuk - it event 2013 (5)Igor Bronovskyy 09 - Express Nodes on the right Angle - Vitaliy Basyuk - IT Event 2013 (5)
60 вузлів під правильним кутом - миттєва розробка програмних додатків використовуючи Node.js + Express + MongoDB + AngularJS.
Коли ми беремось за новий продукт, передусім ми думаємо про пристрасть, яка необхідна йому, щоб зробити користувача задоволеним і відданим нашому баченню. А що допомагає нам здобути прихильність користувачів? Очевидно, що окрім самої ідеї, також важлими будуть: зручний користувацький інтерфейс, взаємодія в реальному часі та прозора робота з даними. Ці три властивості ми можемо здобути використовучи ті чи інші засоби, проте, коли все лиш починається, набагато зручніше, якщо інструменти допомагають втілити бажане, а не відволікають від головної мети.
Ми розглянемо процес розробки, використовуючи Node.js, Express, MongoDB та AngularJS як найбільш корисного поєднання для отримання вагомої переваги вже на старті вашого продукту.
Віталій Басюк
http://itevent.if.ua/lecture/express-nodes-right-angle-rapid-application-development-using-nodejs-express-mongodb-angular
ASP.NET Web Security



ASP.NET Web SecuritySharePointRadi The document discusses various web security topics such as SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), and parameter tampering. It provides examples of these vulnerabilities and methods to prevent them, including input validation, output encoding, anti-forgery tokens, and limiting exposed functionality. The document is intended as an educational guide on common web security issues and best practices.
Whatever it takes - Fixing SQLIA and XSS in the process



Whatever it takes - Fixing SQLIA and XSS in the processguest3379bd This document discusses techniques for preventing SQL injection and cross-site scripting (XSS) vulnerabilities. It proposes using prepared statements with separate data and control planes as a "safe query object" approach. It also discusses policy-based sanitization of HTML and focusing code reviews on defect detection through annotating suspicious code regions. The overall goal is to help developers adopt architectures and techniques that thoroughly apply technical solutions to recognize and fix security weaknesses.
StHack 2014 - Mario "@0x6D6172696F" Heiderich - JSMVCOMFG



StHack 2014 - Mario "@0x6D6172696F" Heiderich - JSMVCOMFGStHack JSMVCOMFG is a presentation by Mario Heiderich on looking at JavaScript MVC and templating frameworks. These frameworks are becoming popular and complex, often maintained by large corporations. They extend and abstract the DOM using custom elements, script templates, and data bindings. However, they also introduce security risks by allowing JavaScript execution from data attributes and encoded templates, bypassing XSS filters. Frameworks need to implement better sandboxing and separation of code and content to address these issues.
Hunting Security Bugs in Modern Web Applications



Hunting Security Bugs in Modern Web ApplicationsToe Khaing This document summarizes a presentation on hunting security bugs in modern web applications. It introduces the speaker and their background in bug bounty hunting. It then covers popular web application technologies, frameworks, and content management systems. The rest of the document outlines various types of security vulnerabilities that can be found, including injection flaws, authentication issues, cross-site scripting, access control failures, and insecure direct object references. Specific methodologies are provided for finding each vulnerability, such as testing authentication, session management, and input validation. The benefits of responsible vulnerability discovery and reporting are also mentioned.
They Ought to Know Better: Exploiting Security Gateways via Their Web Interfaces



They Ought to Know Better: Exploiting Security Gateways via Their Web Interfacesmichelemanzotti The document discusses security vulnerabilities found in the web interfaces of security gateways. The author details how they used automated scanners, manual testing with Burp, and SSH access to root to find over 35 exploits in various security gateway products since 2011. Common vulnerabilities included input validation issues, predictable URLs and parameters enabling CSRF, excessive privileges, and session management flaws. The author provides examples of compromising ClearOS and Websense gateways, and demonstrates OSRF through Proofpoint's email system. They conclude many techniques are older but there remains a knowledge gap between secure web and UI development.
手把手教你如何串接 Log 到各種網路服務



手把手教你如何串接 Log 到各種網路服務Mu Chun Wang This document discusses how to connect logs to various network services using Logback. It begins with a brief introduction of common logging frameworks like SLF4J, Log4j 1, Log4j 2 and Logback. It then explains Logback's internal architecture including loggers, appenders and layouts. The main part demonstrates how to develop a custom appender in Logback to send logs to network services by utilizing the ILoggingEvent object. It provides code templates and examples of accessing log content and stack traces. Finally, it introduces some open source Logback appenders and the Logpush service for remote log monitoring.
Hackers vs developers



Hackers vs developersSoumyasanto Sen Hackers and developers are compared in the document. Hackers are described as skillful with deep technical understanding but often unsocial and focused on breaking systems. Developers are portrayed as true professionals who work with people to build applications and believe they can change the world. The document then provides examples of how hacking can look simple, such as cross-site scripting attacks on websites. It offers suggestions for prevention including input sanitization and access control. Later it discusses hacking in Node.js and risks of SQL and NoSQL injection. Finally it addresses how hacking and development skills could be applied for social good or security testing.
Web Security 101



Web Security 101Michael Peters This talk walks through the basics of web security without focussing too much on the particular tools that you choose. The concepts are universal, although most examples will be in Perl. We'll also look at various attack vectors (SQL Injection, XSS, CSRF, and more) and see how you can avoid them. Whether you're an experienced web developer (we all need reminding) or just starting out, this talk can help avoid being the next easy harvest of The Bad Guys.
Application Security around OWASP Top 10



Application Security around OWASP Top 10Sastry Tumuluri Caution: This is a dated presentation; uploaded for reference. While the principles remain valid, specifics may have changed.
This presentation was made for software developers in Chandigarh - as a part of the NULL & OWASP Chandigarh Chapter activities.
It covers the basics of secure software development and secure coding using OWASP Top 10 as a broad guide.
Web Apps Security



Web Apps SecurityVictor Bucutea This document discusses various web application security vulnerabilities and methods for mitigating them. It begins by summarizing the OWASP Top 10 list of most critical web application security risks. It then provides examples of different types of injection attacks, cross-site scripting, broken authentication and session management issues. The document also discusses insecure cryptographic storage, insufficient transport layer protection and other vulnerabilities. It emphasizes the importance of input and output validation, as well as proper encoding to prevent attacks. The OWASP ESAPI framework is presented as a tool to help developers address many of these security issues.
Reviewing AngularJS



Reviewing AngularJSLewis Ardern Reviewing AngularJS applications presented at SteelCon - https://www.youtube.com/watch?v=p6Ji7UYzfk0
Ad
More from David Paluy (15)
Intro to Smart Contracts



Intro to Smart ContractsDavid Paluy This document provides an introduction to smart contract development. It defines smart contracts and Byzantine fault tolerance. Solidity is introduced as a contract-oriented programming language that compiles to bytecode executable on the Ethereum Virtual Machine. The document stresses the importance of security testing given the immutability of bugs in blockchain-based smart contracts. It also lists tools for testing, deploying to networks, and monitoring smart contracts in production.
Decentralizing Everything with Blockchain



Decentralizing Everything with BlockchainDavid Paluy Blockchains use distributed ledgers to allow transactions to be recorded across a network without a central authority. This document discusses how blockchains can be used to decentralize systems using cryptocurrencies and smart contracts. It also describes how initial coin offerings (ICOs) have raised over $1.3 billion in 2017 by selling tokens that can provide rights to participate in blockchain activities or share company profits. However, blockchains still face challenges to widespread adoption including difficulties in understanding, using, and securing the technology that require improvements in applications, security and user interfaces.
Testing with Rspec 3



Testing with Rspec 3David Paluy This document provides an overview and agenda for testing with RSpec 3. It discusses RSpec expectations and matchers, mocks vs stubs, model specs, controller specs, using FactoryGirl for test data, API testing best practices, and references for further reading on RSpec 3. The overview covers setting up RSpec, expectations, mocking, testing models, controllers, factories, shared examples, API testing, and JSON helpers.
Continuous integration for Ruby on Rails



Continuous integration for Ruby on RailsDavid Paluy Continuous integration (CI) is a development practice that requires developers to integrate code into a shared repository multiple times per day. Each check-in is automatically built and tested to find problems early. For Ruby on Rails projects, CI can generate code coverage reports, perform static code analysis, and document APIs. CI builds confidence by continuously integrating and testing code changes. Continuous deployment further automates software delivery through continuous integration.
Tdd - Test Driven Development



Tdd - Test Driven DevelopmentDavid Paluy TDD involves writing tests before writing code to ensure code works as intended and allows for refactoring. The TDD process involves writing specifications, tests, and then code. Tests provide confidence that code works, help design better code, and act as documentation. Tests should be written even for code that currently works perfectly since requirements and needs change over time. The benefits of TDD include producing modular code that is easy to change and refactor.
Knowledge sharing at MESH



Knowledge sharing at MESHDavid Paluy This document discusses various tools for knowledge sharing, including Google Chrome plugins, CRM tools, time zone converters, whiteboarding software, content sharing apps, and guides for startups to get free press and create content that drives traffic. Some of the specific tools mentioned are OneTab, Rapportive, Streak, Point, Chrome to Mobile, Scrum for Trello, JSON Formatter, CloudApp, EveryTimeZone.com, BufferApp, BuzzSumo, and GlyphSearch. The document also references 17 places to find great content to share and analyzes headlines to provide lessons on creating traffic-driving content.
Juicy Ruby 2.1



Juicy Ruby 2.1David Paluy This document summarizes Ruby version 2.1, including its new features like refinements, decimals as native types, and required keyword arguments. It discusses performance improvements in Ruby 2.1 through profiling support, improved garbage collection, and method caching. It also notes some issues with Ruby 2.1 compatibility and recommends production readiness based on work by Github and others to patch problems.
The Secret: How Programmers Develop Code



The Secret: How Programmers Develop CodeDavid Paluy Programmers develop code by searching for solutions online, asking questions on forums like StackOverflow, and checking forums for answers. They may search Google, ask questions on StackOverflow providing their Rails version and issue details, and check the question's date and score to evaluate answers. Forums allow programmers to ask questions so others facing similar issues can find responses.
Tools to help you understand other people's code



Tools to help you understand other people's codeDavid Paluy There are 4 main issues, you should be aware of:
1. Class Diagram
2. Gems
3. Test before the change
4. Take care of your team style
Debugging and Profiling Rails Application



Debugging and Profiling Rails ApplicationDavid Paluy The document discusses debugging and profiling a Ruby on Rails application that is using excessive memory. It explains how the Ruby garbage collector works and that allocating too many objects can lead to longer garbage collection times and eventually running out of memory. Various tools are presented for debugging memory issues, including pry-debugger, ObjectSpace.count_objects, enabling heap dumps, and gdb.rb. Profiling tools discussed include Benchmark, ruby-prof, and perftools.rb for measuring time, allocations, memory usage, and garbage collection metrics. The key message is that allocating too many objects leads to slowdowns from longer garbage collection, so examining the heap and using debugging and profiling tools is important.
Ruby On Rails coding conventions, standards and best practices



Ruby On Rails coding conventions, standards and best practicesDavid Paluy This document discusses Ruby on Rails coding conventions and best practices. It covers philosophies like DRY (Don't Repeat Yourself) and convention over configuration. It also provides style guidelines for source code formatting, commenting practices, and naming conventions for classes, constants, and variables. Additional sections offer tips for formatting code readably and using Git commit messages effectively.
Git flow Introduction



Git flow IntroductionDavid Paluy This document introduces Git Flow, a Git branching model that provides high-level repository operations. It outlines the main branches - master for production, develop for development, and supporting branches like feature, release, and hotfix. Git Flow is a collection of Git extensions that help initialize and manage branches through commands like git flow feature and git flow release. The model forms an easy to understand mental model for teams to share in their branching and releasing processes.
Faster on Rails



Faster on RailsDavid Paluy This document discusses ways to improve the speed of Rails applications. It covers topics like web servers, Rack web servers, the backend, and the frontend. It analyzes how small delays can negatively impact users and recommends measuring site speed, analyzing bottlenecks, and optimizing performance. Specific technologies mentioned include Nginx, Unicorn, SPDY, database queries, and client-side optimizations. The overall message is that scaling a Rails application is challenging but important for providing a good user experience.
Howto prepare fund raising presentation



Howto prepare fund raising presentationDavid Paluy The document provides tips for maintaining hard drives, including defining a goal, telling your story to convey lessons learned, performing daily maintenance such as spinning down and up and scanning data, ensuring critical data redundancy, staying cool, and allowing idle time. It emphasizes there is no second chance to make a good first impression when it comes to hard drive maintenance.
Test driven-development



Test driven-developmentDavid Paluy The document discusses test-driven development (TDD) and its benefits. It explains that TDD involves writing tests before code to ensure code is focused, clear, and passes all tests. TDD follows a process of red-green-refactor where tests are written, then code is written to pass failing tests, and code is optimized. Well-written tests also serve as documentation and examples of how code should work. The document advocates for TDD, as it breeds confidence through testing, helps write better code, and provides documentation without comments. An example demonstrates writing tests for a credit card submission process before coding the functionality.
Ad
Recently uploaded (13)
Spain is a country in southwestern Europe, located on the Iberian Peninsula. ...



Spain is a country in southwestern Europe, located on the Iberian Peninsula. ...leonardoquispeyapu6 Ingles
Pengenalan Berpikir Kritis Critical_Thinking_Intro.pptx



Pengenalan Berpikir Kritis Critical_Thinking_Intro.pptxJabbarAPanggabean Pengenalan Berpikir Kritis Critical_Thinking_Intro.pptx
CUTS Report by JOHN MEYNARD BARRUGA BAUTISTA, SHENE MERRYLAND BAUTISTA, AND A...



CUTS Report by JOHN MEYNARD BARRUGA BAUTISTA, SHENE MERRYLAND BAUTISTA, AND A...johnmeynardbautista9 For phycology report
Embracing Adaptability (setback) - Istvan Patzay



Embracing Adaptability (setback) - Istvan Patzayisti84 I moved from the Hungarian school system to an international high school in 7th grade, adapting to a new language, teaching style, and diverse cultural environment.
Cognitive development revised - Copy.ppt



Cognitive development revised - Copy.pptMasahiroNagasawa1 All about the theory on cognitive development
How to Prepare for and Survive a Power Outage



How to Prepare for and Survive a Power OutageBob Mayer Every person experiences a power outage. Some more than others. They are a fact of life. How do you prepare for it? Especially an extended one? What to do? How do you stay cool or warm as needed? What gear do you need ahead of time?
It is better to be prepared ahead of time.
Unlocking the Secrets of Love: The Science Behind Heartfelt Connections



Unlocking the Secrets of Love: The Science Behind Heartfelt ConnectionsVikash Gautam Explore the fascinating science of love and how chemistry, biology, and psychology shape our deepest connections. Discover the brain’s role in attraction, emotional bonding, and how love impacts our lives. Learn the hidden truths behind the power of love and its life-changing effects.
Violence against women , finding from the 2008 national demografic



Violence against women , finding from the 2008 national demograficoppateamo1234 -introduction
-Measurement
-Results
Sentence-Errors.pptxssssssssssssssssssss



Sentence-Errors.pptxssssssssssssssssssssrexjosiahzosa this is about the correct and error of sentence statements
CUTS Report by JOHN MEYNARD BARRUGA BAUTISTA, SHENE MERRYLAND BAUTISTA, AND A...



CUTS Report by JOHN MEYNARD BARRUGA BAUTISTA, SHENE MERRYLAND BAUTISTA, AND A...johnmeynardbautista9
Security on Rails
- 1. Security On Rails David Paluy October 2012
- 2. "Ruby is simple in appearance, but is very complex inside, just like our human body." Yukihiro "matz" Matsumoto
- 3. Agenda ● Session Hijacking ● CSRF ● Mass Assignment ● SQL Injection
- 4. Websites are all about the data!
- 5. When is a user not a user?
- 6. You have no way of knowing who or where the data that hits your application is coming from.
- 8. Session Hijacking ● Sniff the cookie in an insecure network. ● Most people don’t clear out the cookies after working at a public terminal ● Cross-Site Scripting (XSS) ● CSS Injection ● Header Injection
- 9. config.force_ssl = true ● If you have http assets on an https page, the user’s browser will display a mixed-content warning in the browser bar. ● Rails does most of the work for you, but if you have any hard-coded “http://” internal-links or images, make sure you change them.
- 10. Session Expiry class Session < ActiveRecord::Base def self.sweep(time = 1.hour) if time.is_a?(String) time = time.split.inject { |count, unit| count.to_i.send(unit) } end delete_all "updated_at < '#{time.ago.to_s(:db)}' OR created_at < '#{2.days.ago.to_s(:db)}'" end end
- 11. Provide the user with a log-out button in the web application, and make it prominent.
- 12. XSS Countermeasures strip_tags("some<<b>script>alert('hello')<</b>/script>") RESULT: some<script>alert(‘hello’)</script> <%= h post.text %> <%= sanitize @article.body %> view SanitizeHelper
- 13. CSS Injection ● <div style="background:url('javascript:alert(1)')"> ● alert(eval('document.body.inne' + 'rHTML'));
- 14. Header Injection redirect_to params[:referer] http://www.yourapplication.com/controller/action? referer=http://www.malicious.tld Make sure you do it yourself when you build other header fields with user input.
- 15. Session Storage config.action_dispatch.session = { :key => '_app_session', :secret => '0dkfj3927dkc7djdh36rkckdfzsg...' }
- 16. Cross-Site Request Forgery (CSRF) Most Rails applications use cookie-based sessions
- 17. CSRF Countermeasures Be RESTful Use GET if: ● The interaction is more like a question (i.e., it is a safe operation such as a query, read operation, or lookup). Use POST if: ● The interaction is more like an order, or ● The interaction changes the state of the resource in a way that the user would perceive (e.g., a subscription to a service), or ● The user is held accountable for the results of the interaction. protect_from_forgery :secret => "123456789012345678901234567890..."
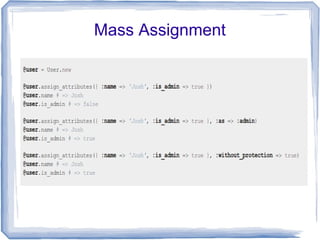
- 18. Mass Assignment attr_accessible :name attr_accessible :is_admin, :as => :admin
- 19. Mass Assignment
- 20. SQL Injection ● Project.where("name = '#{params[:name]}'") SELECT * FROM projects WHERE name = '' OR 1' ● User.first("login = '#{params[:name]}' AND password = '#{params[:password]}'") SELECT * FROM users WHERE login = '' OR '1'='1' AND password = '' OR '2'>'1' LIMIT 1
- 21. SQL Injection Countermeasures ● Model.where("login = ? AND password = ?", entered_user_name, entered_password).first ● Model.where(:login => entered_user_name, :password => entered_password).first
- 22. Tools ● Brakeman - A static analysis security vulnerability scanner for Ruby on Rails applications ● RoRSecurity – explore Rails security ● Techniques to Secure your Website with RoR
- 23. Summary The security landscape shifts and it is important to keep up to date, because missing a new vulnerability can be catastrophic.




