Ad
State of DevSecOps - DevOpsDays Jakarta 2019
- 1. The State of DevSecOps
- 2. About me Stefan Streichsbier @s_streichsbier GuardRails.io Move fast, be safe.
- 3. What do these companies have in common? <10 years
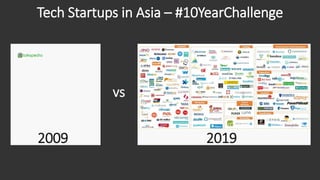
- 4. Tech Startups in Asia – #10YearChallenge 2009 vs 2019
- 5. How is that possible?
- 6. 1. Existing solutions are no longer adequate Provide A Terrible User Experience Enterprise Solutions Come From The Waterfall Era Enterprise Means Overpriced
- 7. 2. SaaS enable wide-spread distribution Your Users Are EverywhereNo Need To Go To A Physical Location No Need to Create WW Sales Teams
- 8. 3. Cheaper to create & operate Software Startup Ecosystems Empower Entrepreneurs Open Source Software Provides Building Blocks Cloud Computing Provides Low Barrier of Entry
- 9. To summarize The existing solutions are ripe for replacement Creating new technology solutions was never faster Software can be Distributed globally
- 10. DevSecOps: How important is it really? • Agile took us from months to days to deliver software • DevOps took us from months to minutes to deploy software • More applications are mission critical • Now security has become the bottleneck
- 11. The real impact of hacks & breaches News is full of high-profile breaches that get widespread attention. But they are not the only target of hackers 43% of all cyber attacks target small businesses. 60% of small businesses that are Hacked go out of business within 6 months. 1/5 data breaches are the result of attackers abusing insecure web applications.
- 13. The Evolution of Security Tools Secure SDLCPenetration Testing DevSecOps Duration 2-4 weeks 1-2 weeks Continuous and Real-time Tools • Port Scanners • Vulnerability Scanners • Exploitation Tools Audience • Security Professionals Tools • Code Security Scanners • Dynamic Security Scanners • Vulnerability Scanners Audience • Security Professionals in Enterprise Security Teams Tools • Code Security Scanners • Interactive Security Scanners • Runtime Application Self Protection Audience • Developers in Product Teams
- 14. Security Development Operations The Evolution of Security Teams Secure SDLCPenetration Testing DevSecOps Security Development Operations Security Development Operations “Department of NO” “Let’s work together” “How can we help you succeed?”
- 15. Modern security teams empower dev teams! 100 10 1 Dev Ops Sec: : : : Looks like we have a scale problem
- 17. - John Willis You build it, you secure it.
- 18. Mindset within your product teams • Have Shared Pain and Shared Goals • Clearly defined global delivery goals (no competing KPIs) • Measure outcome (customer value), not output • Be Autonomous • Maximize flow (minimize cycle times) • Implement fast automated test suites • Never pass defects downstream • Create quality at the source (provide knowledge where needed) • Full decision authority • Full Accountability • Good or bad - you own it. There is no one else to blame
- 20. Understanding benefits of security controls Create Test Monitor Challenges • Changing human behavior • Difficult to enforce • People churn Benefits • Reduce new vulnerabilities Challenges • Vulnerability Noise • Fixing issues • Coverage of issues Benefits • Enforceable • Provide Metrics Challenges • Coverage of issues • Org wide rollout Benefits • Enforceable • Provide Metrics • Block attacks Security
- 21. DevSecOps - Monitor Are your applications currently under attack? Are we automatically defending against this attack? What are attackers going after? • Micro Segmentation • Runtime Application Self Protection (RASP) • Bug Bounties Questions you should be able to answerAvailable Technologies
- 22. DevSecOps - Test Do the latest changes introduce new security issues? Does our code contain hard- coded secrets? Do any of our 3rd party libraries have known security issues? Questions you should be able to answer • Static Application Security Testing (SAST) • Sensitive Information Scanners (SIS) • Software Composition Analysis (SCA/CCA) • Dynamic Security Scanning (DAST) • Interactive Application Security Testing (IAST) Available Technologies
- 23. Automated Security Testing SAST SCA DAST/IASTCCA CommercialOpenSource 60+
- 24. Where do these tools live? Source: https://twitter.com/djschleen
- 25. DevSecOps - Create Do your teams know the most common successful attacks? Who is the dedicated security contact in a team? Do your teams know how to detect and avoid them? Questions you should be able to answer • Security Awareness • Secure Coding Training • Shared Knowledge Base • Security Focused Hackathons • Security Champion Program Available Options
- 26. DevSecOps Do we really need it now? There are some compelling statistics • It’s 30 times cheaper to fix security defects in development vs production • 80% to 90% of modern applications consist of open source components • An average data breach costs 5M+ USD • Most of the DevOps high-performers include security in their delivery process Security as Competitive Advantage
- 27. State of DevSecOps - Conclusion Security TeamTechnologies Product Team • Tools have improved • Choose them wisely • Solve technology problems • Cover the whole portfolio • Start acting on data in prod • Department of YES • Empowering product teams • Use scarce resources wisely • Knowledge is power • Turn developers into security champs • Be mindful that change is slow • Build it, run it, secure it
- 28. Thank you
- 29. Get a curated list of security resources Consisting of: • Awesome security lists • Developer trainings • List of great security tools • Security Page templates • Free digital copy of my book • the slides • … and more Then send an email to: [email protected]
Editor's Notes
- #2: Welcome everonye, good to be here, Great turnout
- #4: The are all from Indonesia! They are all tech companies. The are all considered unicorns (valued over 1 billion) They didn’t exist 10 years ago.
- #5: And by the way, how many of you here today are in a fintech or any other kind of tech company startup? fintech slide -> You may join the unicorn club soon.
- #6: It's astonishing how this game of david and goliath has changed the world in the last decade. Now, why is that possible? Software has become mission-critical!
- #7: 1.) The existing solutions (in all industries) typically suck. -> The foundation of this opportunity. Simply put a lot of the existing incumbent solutions (in all industries) are coming from the waterfall era, have a terrible User Experience and follow an enterprise software model. Think about it, even the online banking solutions that exist today are typically much more user-friendly for consumers than they are for business users. -> Waterfall vs Agile vs DevOps "Wait, I have to use this stuff to collaborate? If I can use Facebook Messenger at home, why do I have this crummy messaging tool at work?" So that's certainly been one angle that I think has changed things.
- #8: 2.) Software as a service and the internet in general allow wide-spread and instant distribution. Second is, obviously software as a service and the internet generally, you know, our ability, so we sell into 170 different countries now, so we never could have done that in a traditional enterprise model. We would have needed sales people all over the world, etc. So we can spread out the revenue generation, if you like, much more around the globe, much more quickly.
- #9: 3.) The cost of producing and operating software has gone down significantly. The entry barrier is almost removed. And at the same time, the cost of producing that service or creating that software has gone down rapidly with open source, and cloud computing in terms of AWS, things like that. So we can effectively deliver a better product for cheaper and kind of instantly get it around the world and just let it bubble up. Cloud providers offer up to 100k credits for startups. Every major Saas product that a company needs either offers free plans for startups or heavily reduced prices. Cloud computing
- #10: Litmus test, how long does it take you to get one line of code through your system?
- #11: DevOps is all about breaking down barriers, have developers work with the business, with the ops team and simply out-innovate and out-ship the competition. Software has become mission-critical!
- #12: While hacking-related data breaches and subsequent ransom demands to large corporations like HBO, Target, and Home Depot understandably garner widespread attention, t he resulting assumption that only large companies face this growing digital threat couldn’t be further from the truth. In fact, a study in 2016 found that 43% of all cyber attacks targeted small businesses. Even more alarming is that a staggering 60% of small businesses hit with a cyber attack or data breach go out of business within 6 months. Software has become mission-critical!
- #13: Everyone!!! Ok, but who is accountable?
- #14: Different Tools come from different eras and are focused on outcomes and different audiences.
- #15: Working as an audit/control function Working as security gates in the lifecycle Empowering DevOps teams to move fast and be safe.
- #16: Alright, so the purpose of security teams Is to support the engineering organization To ensure that the business can achieve Their goals. However, there is a scale problem. Think about how many developers you have in your organization. How many DevSecOps ready security folks? There is a global shortage of 2m cyber security professionals,. It just can’t be solved by throwing security people at the problem You gotta be smart,
- #17: The traditional model is that you take your software to the wall that separates development and operations, and throw it over and then forget about it. Let’s look at how the big organizations are doing it. https://www.slideshare.net/ufried/the-truth-about-you-build-it-you-run-it
- #18: You build it you secure it. What does that mean? It’s not a question of responsibility it’s a question of accountability. Why would any third party come and tell you what to do, they don’t know the context, don’t know the other stuff. Why would they run a tool for you that produces a million findings, and leave you with the results to clean it up? Oh and by the way, you have to get rid of all the medium and high before going live. The security team can not be accountable. Ok, so who is accountable? That also means that business can make decisions to override security requirements. Believe me, I am coming from a pentesting background, and there is no perfect security posture. So you gotta think about getting the guardrails established, at the very minimum. Get rid of all the low hanging fruits. Avoid counter productive best practices.
- #21: Outside in approach Get data -> attacks, vulnerabilities, etc Don’t focus on 1 application, focus on getting this data for the whole portfolio (prioritize by business risk). Where can you solve technology problems reliably across Quality, Performance, Security
- #22: Think Application Performance monitoring for security Understanding how your app is abused and misused helps with prioritization.
- #23: Think Application Performance monitoring for security Understanding how your app is abused and misused helps with prioritization.
- #27: To give an analogy, Software doesn't have to be of high quality and excellent user experience. most of the successful enterprise software did not provide these and they did succeed - until now at least. But now many of these organizations are struggling heavily, because their entire culture and processes are outdated and they are moving very slow. No matter how much money these orgs have, it is still a tricky process, because it's attempting to change the culture. Another example is Tesla. Stunning cars, that delight users all over the world. They designed a new car from the ground up. Many of their competitors spending a lot of money and time to retrofit their cars and convert them into more and more smart cars. But Tesla is a supercomputer on wheels and is out innovating the competition. The key point is that certain aspects that may not seem that relevant at the moment, will become the decisive advantage in the future. You can’t develop software and expect it to be secure after an audit at the end. Same way you can’t say now that the feature is shipped make sure it performs well and doesn’t have any bugs. Thebest time to plant a tree was 20 years ago. The second best time is now. That’s why we see many new organisations succeed, because they don’t carry the same baggage and can get things right from the start. Despite the challenges of identifying quality metrics that apply to all organizations, we can identify good proxies for quality that work across companies and industries. These include how time is spent, because it can tell us if we are working on value-add work or non-value-add work.
- #28: Focus on the right improvements, e.g measuring defect density, etc. E.G if a technology can reliably identify and prevent a vulnerability in production, without having to involve humans to fix it, then That’s a good start. If you can have technology that alerts you of breaches while containing them, that’s great. Use it. If you have tools that you can embed in your pipeline to get more continuous security feedback into the hands of developers, then use that Be smart about where to use human efforts on and where not to. Security team should help engineering teams to succeed and achieve their mission. Not say no and delay releases like an audit function. Start with general training programs, there is excellent free training out there for engineers and basic security awareness. As you get more data from your tools, then you will be able to prioritize the next focus areas and teams that require that training. Teaching people and changing the culture is hard and takes a long time. It is still important but make sure all the other aspects are Reducing your risk while simultaneously buying time.